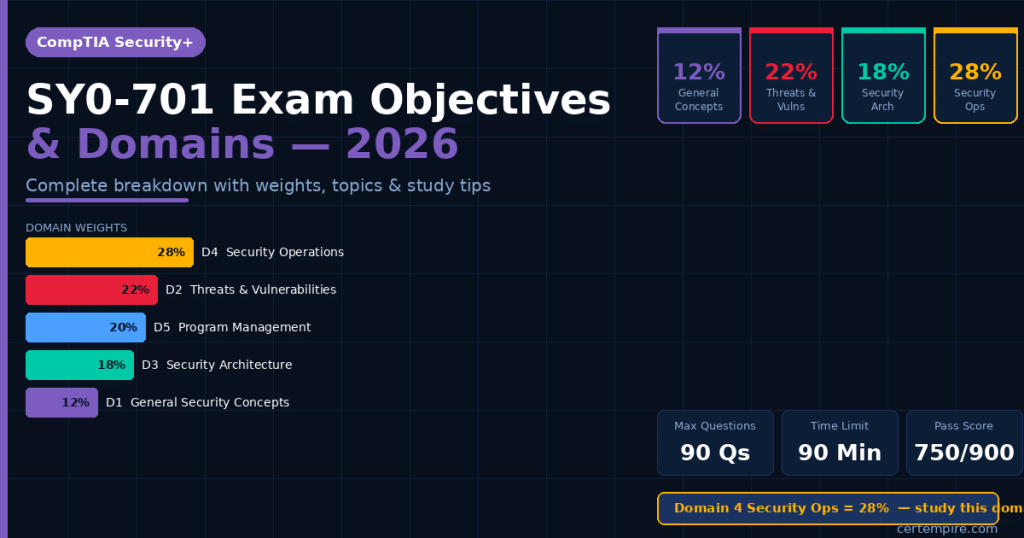
Quick Answer: The SY0-701 exam covers five domains: General Security Concepts (12%), Threats, Vulnerabilities, and Mitigations (22%), Security Architecture (18%), Security Operations (28%), and Security Program Management and Oversight (20%). Security Operations is the largest domain at 28% — it deserves proportionally more study time than any other. The exam has up to 90 questions in 90 minutes with a passing score of 750 out of 900.
Last Reviewed: April 2026 | Exam Code: SY0-701 | Page Title Updated from “2025” to 2026
Why Understanding SY0-701 Objectives Changes How You Prepare
Most candidates approach SY0-701 preparation the same way — buy a course, watch the videos, take some practice questions, repeat until exam day. That approach works for some people. It fails for many others, particularly on the performance-based questions, because it treats all topics as equally important.
The SY0-701 exam objectives are not equally weighted. Domain 4 (Security Operations) covers 28% of your score. Domain 1 (General Security Concepts) covers 12%. If you spend the same amount of study time on both, you are wasting preparation capacity on low-yield content while underinvesting in the section that determines more than a quarter of your result.
Knowing the exact objectives also tells you which specific topics the exam can and cannot test. The official SY0-701 exam objectives document from CompTIA.org is a finite list — everything testable is on it, and nothing outside it appears on the exam. Every hour of study should map to something on that list.
For a broader overview of the exam including cost, format, and career value, see our CompTIA Security+ SY0-701 exam guide.
SY0-701 Domain Overview — Weights at a Glance
| Domain | Weight | Questions (approx.) | Priority |
| 1. General Security Concepts | 12% | ~11 questions | Study 3rd |
| 2. Threats, Vulnerabilities & Mitigations | 22% | ~20 questions | Study 2nd |
| 3. Security Architecture | 18% | ~16 questions | Study 4th |
| 4. Security Operations | 28% | ~25 questions | Study 1st |
| 5. Security Program Management & Oversight | 20% | ~18 questions | Study 5th |
| Total | 100% | ~90 questions |
The “Study Priority” column reflects where to invest the most time relative to exam impact — not the order to study them. Domain 1 is best studied first because it provides the foundational vocabulary for everything else, even though it carries the least weight.
Domain 1: General Security Concepts — 12%
What This Domain Covers
Domain 1 is the smallest by weight but the most foundational. Every other domain builds on the vocabulary and concepts introduced here. Candidates who skip or rush Domain 1 consistently struggle with scenario questions in Domains 2 through 5 because they are missing the conceptual framework.
Key topics tested:
Security controls and their categories. You need to know control categories (technical, managerial, operational, physical) and control types (preventive, detective, corrective, deterrent, compensating, directive). The exam tests these through scenarios — given a described situation, which type of control is being implemented? Understand the difference between what a control does (type) and how it is implemented (category).
CIA triad and its applications. Confidentiality, Integrity, and Availability are the three pillars of information security. More importantly, the exam tests how attacks affect the CIA triad — a ransomware attack primarily affects availability, a man-in-the-middle attack primarily affects confidentiality, data tampering primarily affects integrity. Know the attack-to-triad mapping.
Cryptography fundamentals. Symmetric encryption (same key for encryption and decryption — faster, used for bulk data), asymmetric encryption (public/private key pair — slower, used for key exchange and digital signatures), hashing (one-way, produces fixed-length output, used for integrity verification), and digital signatures (asymmetric + hashing combined for authenticity and non-repudiation). You do not need to implement cryptographic algorithms — you need to know when and why each type is used.
Authentication concepts. Authentication factors (something you know, something you have, something you are, somewhere you are, something you do), MFA implementation scenarios, single sign-on (SSO), and federation concepts.
Zero trust at the conceptual level. Verify explicitly, use least privilege access, assume breach. Know what zero trust means in principle and what distinguishes it from traditional perimeter-based security. For a detailed explanation, see our zero trust security guide.
PKI and certificate management. Certificate authorities (CAs), certificate revocation (CRL and OCSP), certificate types (DV, OV, EV, wildcard, SAN), and the chain of trust.
How Domain 1 Appears on the Exam
Domain 1 questions are mostly multiple-choice with clear right answers once you know the definitions. This is the least scenario-heavy domain. Expect questions like “Which type of control is a security guard?” (physical, preventive) or “A company wants to ensure that only authorized users can view patient records. Which component of the CIA triad does this address?” (confidentiality).
Domain 1 Study Tip
Create a two-column reference sheet: control categories on one side, control types on the other. Do the same for cryptography types. These classification frameworks appear repeatedly across all five domains and being able to recall them instantly saves time under exam conditions.
Domain 2: Threats, Vulnerabilities, and Mitigations — 22%
What This Domain Covers
Domain 2 is the second largest and the most directly connected to real-world attacker behavior. It tests whether you can recognize threats, understand how they work at a conceptual level, identify indicators of compromise, and select appropriate mitigations.
Key topics tested:
Malware types and behaviors. Ransomware (encrypts data, demands payment), trojans (disguises itself as legitimate software), rootkits (hides its presence on a system), keyloggers (captures keystrokes), spyware (collects user information without consent), adware, worms (self-replicating, spreads across networks), and fileless malware (operates in memory, no disk footprint). Know what each type does and how it typically enters a system.
Social engineering attacks. Phishing (email-based), spear phishing (targeted phishing), whaling (executive-targeted), vishing (voice phishing), smishing (SMS phishing), pretexting (fabricated scenario to gain trust), baiting (uses physical media like USB drives), quid pro quo (offers something in exchange for information), and tailgating (physical access bypass). The SY0-701 version expanded coverage of AI-driven phishing and deepfake-based social engineering.
Network-based attacks. DoS and DDoS attacks, man-in-the-middle (on-path attacks), ARP spoofing, DNS poisoning, SSL stripping, and replay attacks. Know how each works at a high level — not the implementation but the mechanism.
Application vulnerabilities. SQL injection (unsanitized input executed as SQL), cross-site scripting (XSS — malicious script injected into web pages), cross-site request forgery (CSRF), buffer overflow (writing beyond allocated memory), race conditions, and insecure direct object references. These appear heavily in PBQ scenarios.
Supply chain and third-party risks. This is significantly expanded in SY0-701 compared to SY0-601. Expect scenarios involving software supply chain attacks, hardware tampering, and third-party vendor compromise. The SolarWinds-style attack is the canonical example — malicious code inserted into legitimate software updates.
Vulnerability assessment concepts. CVE (Common Vulnerabilities and Exposures) identifiers, CVSS (Common Vulnerability Scoring System) scores and what they measure, vulnerability scanning versus penetration testing, false positives in scanner output, and the difference between credentialed and non-credentialed scans.
Indicators of compromise (IoCs). Unusual outbound traffic, unexpected account privilege changes, large data transfers, modified system files, new unknown services, and communication with known malicious IP addresses. The exam tests whether you can look at a described scenario and identify which IoC is present.
For real-world examples of every attack type covered in this domain, see our types of cyber attacks guide.
How Domain 2 Appears on the Exam
This domain has the highest proportion of scenario-based multiple-choice questions. You will be given a described situation and asked to identify the attack type, the most likely threat actor, the appropriate mitigation, or the best tool for detection. PBQs in this domain may ask you to analyze a described network incident and match it to an attack type.
Domain 2 Study Tip
For each attack type, build a three-column reference: attack name | how it works | primary mitigation. When you can fill in all three columns from memory for every attack on the exam objectives list, you are ready for this domain.
Domain 3: Security Architecture — 18%
What This Domain Covers
Domain 3 covers the design and evaluation of secure systems. It is less about identifying threats and more about building environments that minimize attack surface and maximize resilience.
Key topics tested:
Network segmentation and design. VLANs (virtual separation of network traffic), DMZ (demilitarized zone — hosts publicly accessible services while protecting the internal network), microsegmentation (granular segmentation, often in software-defined networks), air-gapping (physical isolation from external networks), and network access control (NAC). Know the purpose and appropriate use case for each.
Zero trust architecture in practice. Beyond the conceptual coverage in Domain 1, Domain 3 tests the implementation implications of zero trust — continuous verification, device health assessment, identity-based access regardless of network location, and the shift from perimeter-focused to identity-focused security.
Cloud and hybrid security. The shared responsibility model (what the cloud provider secures versus what the customer secures — varies by service model: IaaS, PaaS, SaaS), cloud security posture management (CSPM), cloud access security brokers (CASBs), and securing workloads in hybrid environments. This topic has grown substantially in SY0-701.
Secure protocols. TLS (replaces SSL for encrypted web traffic), HTTPS, SSH (encrypted remote access), SFTP/FTPS (encrypted file transfer), DNSSEC (DNS integrity), VPN protocols (IPsec, SSL/TLS-based VPNs), and wireless security protocols (WPA2, WPA3, 802.1X for enterprise wireless). Know what each protocol secures and why older versions (SSL, WEP, TLS 1.0/1.1) are considered insecure.
Infrastructure resilience. RAID (redundant storage — know RAID 0, 1, 5, 10 and what each provides), high availability and failover clustering, geographic redundancy, backup types (full, incremental, differential), recovery time objective (RTO) and recovery point objective (RPO), and business continuity planning at the infrastructure level.
Secure software development. Secure SDLC concepts, input validation, secure coding practices, code signing, dependency management, and static vs dynamic application security testing (SAST vs DAST).
How Domain 3 Appears on the Exam
Architecture questions often present a described network environment and ask you to identify the security weakness or select the most appropriate design decision. Expect questions like “A company wants to allow web servers to be accessible from the internet while protecting internal database servers. Which architecture should they implement?” (DMZ).
Domain 3 Study Tip
Draw network diagrams for common secure architectures — DMZ with public servers, internal segmented networks, zero trust access scenarios. Visualizing the topology helps you answer diagram-based PBQs and makes design-choice questions much more intuitive.
Domain 4: Security Operations — 28%
What This Domain Covers
Domain 4 is the largest and most operationally focused domain. It reflects what security professionals actually do day-to-day in security operations centers and incident response roles. This domain has the highest proportion of performance-based questions.
Key topics tested:
Incident response lifecycle. The six phases: Preparation → Identification → Containment → Eradication → Recovery → Lessons Learned. The exam tests the correct sequence and what happens in each phase. Common trap: candidates confuse Eradication (removing the threat) with Containment (limiting the damage while the threat is still present). These are distinct phases with different actions.
Log analysis and SIEM. Security Information and Event Management (SIEM) systems aggregate logs from across an environment and correlate events to identify security incidents. You need to understand what types of events generate security-relevant logs (failed authentications, privilege escalations, unusual process executions, outbound connections to unfamiliar IPs), how to read basic Windows Event Log entries (Event ID 4625 = failed logon, Event ID 4672 = special privileges assigned, Event ID 4688 = new process created), and how SIEM alert triage works.
Digital forensics. Order of volatility (collect most volatile evidence first: CPU registers/cache → RAM → swap space → HDD → remote logs → paper/optical media), chain of custody, legal hold, forensic imaging (bit-for-bit copy, never work on original evidence), and the difference between live forensics and dead-box forensics.
Vulnerability management operations. Running vulnerability scans, interpreting CVSS scores in context (a CVSS 9.8 on an internet-facing system is higher priority than the same score on an isolated internal system with compensating controls), patch management lifecycle, and remediation prioritization based on asset value and exploitability.
Identity and access management (IAM). Role-based access control (RBAC), mandatory access control (MAC), discretionary access control (DAC), attribute-based access control (ABAC), the principle of least privilege, privileged access management (PAM), account lifecycle management (provisioning, modification, deprovisioning), and directory services.
Endpoint security. Endpoint detection and response (EDR), host-based intrusion detection/prevention systems (HIDS/HIPS), application allowlisting and denylisting, disk encryption (BitLocker, FileVault), and mobile device management (MDM).
Data loss prevention (DLP). DLP solutions that monitor and prevent unauthorized transmission of sensitive data — network DLP (monitors traffic), endpoint DLP (monitors endpoint activity), and cloud DLP (monitors cloud storage and sharing).
SOAR (Security Orchestration, Automation, and Response). Automated playbooks that respond to security alerts without human intervention — reducing response time and analyst fatigue. This is a newer topic expanded in SY0-701.
How Domain 4 Appears on the Exam
This domain has the most PBQs. Expect to be given a log file and asked to identify the suspicious activity. Expect scenario questions where you must select the correct incident response phase action. Expect questions about which IAM control fits a described access scenario. Hands-on lab practice is essential — theory alone will not prepare you for the applied format of these questions.
Domain 4 Study Tip
Spend 30 minutes every other day in your lab analyzing logs. Use Windows Event Viewer to review security logs on any Windows machine. Filter for Event IDs 4625, 4672, and 4688 and understand what each tells you. This single habit, done consistently over 3–4 weeks, will dramatically improve your performance on Domain 4 PBQs.
Domain 5: Security Program Management and Oversight — 20%
What This Domain Covers
Domain 5 received a significant weight increase in SY0-701 compared to SY0-601. It covers the governance, risk, and compliance layer of security — the organizational and policy framework that ensures security controls are consistent, effective, and legally compliant.
Key topics tested:
Regulatory compliance frameworks. GDPR (EU — personal data of EU residents, applies globally when handling EU data), HIPAA (US — protected health information, applies to healthcare providers and business associates), PCI-DSS (global — payment card data for any organization accepting card payments), CMMC (US DoD — defense contractors handling Controlled Unclassified Information), and SOX (US — financial reporting for publicly traded companies). Know which framework applies to which industry and data type — this is a common exam topic.
Risk management. Risk identification (asset-based threat modeling), qualitative vs quantitative risk analysis, risk treatment options (accept, avoid, transfer, mitigate), residual risk (risk remaining after controls are applied), risk appetite versus risk tolerance, and inherent risk (risk before controls). The exam tests these through scenario questions — given a described situation and possible responses, which risk treatment is being applied?
Security policies and governance. Acceptable use policies, data classification policies (public, internal, confidential, restricted/secret), change management policies, incident response policies, and how policies relate to standards, guidelines, and procedures in the governance hierarchy.
Third-party and vendor risk management. Vendor risk assessments, supply chain security, right-to-audit clauses, data processing agreements, and due diligence when onboarding vendors with access to sensitive data.
Business continuity and disaster recovery. Business impact analysis (BIA), recovery time objective (RTO), recovery point objective (RPO), mean time to recover (MTTR), mean time between failures (MTBF), tabletop exercises, and the difference between a hot site, warm site, and cold site for disaster recovery.
Security awareness and training. Phishing simulation programs, role-based security training, security culture metrics, insider threat prevention programs, and the human element of security controls.
How Domain 5 Appears on the Exam
Domain 5 questions are scenario-based and test organizational decision-making rather than technical implementation. You will be given a business scenario and asked which framework applies, which risk treatment is most appropriate, or which policy element addresses a described concern. These questions reward structured thinking — knowing the framework and applying it — over memorization.
Domain 5 Study Tip
Map each major compliance framework to three things: what data/industry it covers, who it applies to, and what its most notable requirements are. Creating a one-page table covering GDPR, HIPAA, PCI-DSS, CMMC, and SOX gives you a reference you can use through your entire preparation and makes scenario questions significantly easier.
What Changed from SY0-601 to SY0-701
If you have any study materials from SY0-601 preparation, here is exactly what you need to update:
| What Changed | SY0-601 | SY0-701 |
| Number of domains | 6 domains | 5 domains |
| Number of objectives | 35 objectives | 28 objectives |
| Security Operations weight | Lower | 28% — largest domain |
| Program Management weight | Lower | 20% — significant increase |
| Implementation domain | Standalone domain | Content absorbed into Architecture and Operations |
| Cloud coverage | Basic | Significantly expanded (hybrid, CSPM, CASB) |
| Zero trust | Mentioned | Full coverage in both Domain 1 and Domain 3 |
| Supply chain attacks | Minimal | Expanded in Domain 2 |
| AI/automation topics | Not present | SOAR, AI-driven threats introduced |
| SY0-601 retirement | — | July 31, 2024 — all candidates now take SY0-701 |
For a detailed look at what specifically changed and what it means for your preparation, see our what’s new in SY0-701 guide.
How to Use the Objectives as Your Study Checklist
The most effective way to use the official SY0-701 exam objectives is as a literal checklist. Download the PDF from CompTIA.org and work through it systematically:
For each objective, ask yourself: can I explain this concept clearly without looking it up? Can I identify a real-world scenario where this applies? Can I select the correct answer to a scenario question testing this objective?
If the answer to all three is yes, check it off. If not, that objective goes on your weak areas list and gets dedicated study time before you move on.
Use CertEmpire’s SY0-701 exam questions as your objective-by-objective testing tool. After studying each domain, run through domain-specific practice questions to verify you have actually mastered the material rather than just read through it. For a starting benchmark, take the free SY0-701 practice test before beginning your preparation — it shows you which domains need the most attention before you spend a single hour studying.
Domain-by-Domain Study Allocation
Based on the exam weights, here is how to allocate your available study hours if you have a fixed preparation timeline:
| Domain | Weight | Recommended Study Allocation |
| General Security Concepts | 12% | 12% of total study hours |
| Threats, Vulnerabilities & Mitigations | 22% | 22% of total study hours |
| Security Architecture | 18% | 18% of total study hours |
| Security Operations | 28% | 30–35% of total study hours (extra for PBQ practice) |
| Security Program Management | 20% | 18–20% of total study hours |
Domain 4 gets slightly more than its 28% weight because it contains the most performance-based question content — and PBQs require hands-on practice time in addition to conceptual study.
For a complete week-by-week implementation of this allocation, see our Security+ study plan and our full SY0-701 preparation guide.
Frequently Asked Questions
What are the five domains of the SY0-701 exam?
General Security Concepts (12%), Threats, Vulnerabilities, and Mitigations (22%), Security Architecture (18%), Security Operations (28%), and Security Program Management and Oversight (20%).
Which SY0-701 domain is the hardest?
Domain 4 (Security Operations) is the hardest for most candidates because it carries the most weight (28%), has the most performance-based questions, and requires hands-on skills in SIEM analysis, incident response, and vulnerability management — not just conceptual knowledge.
How many questions come from each domain?
With up to 90 questions total, approximately 11 questions come from Domain 1, 20 from Domain 2, 16 from Domain 3, 25 from Domain 4, and 18 from Domain 5. These are approximations — exact question counts per domain vary by exam session.
Did the SY0-701 domains change from SY0-601?
Yes significantly. SY0-601 had six domains including a standalone “Implementation” domain. SY0-701 has five domains with Implementation content absorbed into Architecture and Operations. Domain weights also shifted — Security Operations grew to 28% and Program Management to 20%.
Where can I download the official SY0-701 exam objectives?
The official exam objectives PDF is available free at CompTIA.org. Search “SY0-701 exam objectives” and download directly from CompTIA’s certification page.
How long does it take to study all five domains?
With Network+ and IT experience, 8–10 weeks of consistent study covering all five domains is typical. Without IT background, plan 14–16 weeks. Domain 4 should receive the most time due to its weight and PBQ content.
What is the best way to prepare for Domain 4 (Security Operations)?
Combine conceptual study with hands-on lab practice. Set up a virtual lab using VirtualBox, install Windows Server, and practice reviewing security event logs daily. Also use SIEM practice tools and work through incident response scenario questions consistently in the weeks before your exam.
What topics are completely new in SY0-701 that were not in SY0-601?
The most significant additions are SOAR (Security Orchestration, Automation, and Response), expanded zero trust implementation coverage, AI-driven phishing and deepfake social engineering threats, supply chain attack coverage, cloud-native security tools (CASB, CSPM), and the expanded compliance framework coverage in Domain 5.
Final Thoughts
The SY0-701 exam objectives are not just a list of study topics — they are the exact specification of what the exam tests. Candidates who study the objectives systematically, allocate time proportionally to domain weights, and practice applied skills through hands-on labs and scenario-based questions consistently outperform those who study more hours but less strategically.
Domain 4 deserves your most focused preparation time. Domain 2 deserves your second most. Together they represent 50% of your entire exam score — and understanding them at an applied level, not just a definitional level, is what separates first-attempt passers from those who need a retake.
At CertEmpire, our SY0-701 exam questions are built around the current exam objectives and updated to reflect the active SY0-701 blueprint. Start with the free SY0-701 practice test to identify which domains need the most attention, then build your study plan accordingly.
Once you pass, visit our guide on what to do after Security+ for your next steps — whether that is CompTIA CySA+,CISSP, or a different direction entirely based on your career goals. For a full map of where Security+ fits in the broader cybersecurity landscape, see our cybersecurity certification roadmap.
For the official SY0-701 exam objectives PDF and registration information, visit CompTIA.org. For Security+ exam cost details, see our Security+ exam cost guide.