I don’t think B’s right here. Usage reports do actually surface packet loss stats from Teams calls, enough for pilot analysis, even if it’s not super detailed per user. Looks like B is a distractor if you’re thinking about deeper diagnostics.
Does the official MS-700 guide mention anything about tenant-wide policies interfering with these user-level audio conferencing settings? I remember seeing something similar but wasn't sure if those policies override the customized number sequence for specific users.
Pretty sure it's A. Azure AD handles guest domain restrictions, not the Teams admin center. External access (which is C) deals with federation, not true guest invites. If we're locking it down to fabrikam.com specifically for guests, A just fits better. If I'm off on this let me know.
I don’t think network/location config is needed if you enable external location lookup mode. Teams just uses the device OS to grab the current address for emergency calls. The trap is thinking you have to pre-define physical networks, but that's not needed here. Pretty sure that's correct-anyone see it different?
I don't think D is right here. The group settings in the M365 admin center won't handle the 30-day restore or enforce group expiration for Teams like B does. Pretty sure that's the catch-B handles both requirements.
Pretty sure it's B here. Only the New-AzureADMSGroupLifecyclePolicy cmdlet actually sets the group to expire and covers that 30-day content restore part directly, D just doesn't let you manage that lifecycle cleanly. If someone tried D and got it working, let me know, but B matches what MS docs say.
B . The New-AzureADMSGroupLifecyclePolicy cmdlet lets you set group expiration and the restore window fits the 30-day recovery requirement. D looks like a trap since Office 365 group settings don't cover the lifecycle policy part fully. If anyone's tried D and had it work, let me know because I'm not 100% certain.
Honestly, Microsoft loves to bury these alert settings deep. I'm going with B since alert policies in Security & Compliance are pretty much made for tracking things like new group or team creation. Not 100% sure given their confusing admin interfaces, but that's what I remember from similar exam questions.
Doesn't look like this solution fully meets the Teams requirements. B. Those PowerShell cmdlets set basic Azure AD guest policies, but not the Teams-specific controls for domains or invite restrictions. I think it's a trap if you miss the product scope, but happy to discuss if someone has another angle.
B for sure. Changing Sharing settings in the Microsoft 365 admin center affects access to files and folders, not device features like cameras. The trap is thinking that "sharing" covers all permissions, but camera access for guests is managed in Teams meeting policies instead. I think this matches what I've seen on similar questions, but happy if someone can prove otherwise.
Call it A. The Sharing settings in Microsoft 365 admin center affect guest permissions, so pretty sure it can restrict what guests do, including cameras. Maybe I'm missing a detail but feels like a trap for B.
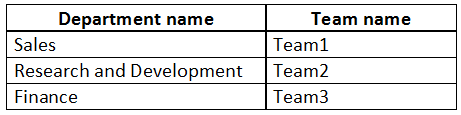 You need to recommend a solution to prevent the users in each department from inviting users from
other departments to their team.
What should you include in the recommendation?
You need to recommend a solution to prevent the users in each department from inviting users from
other departments to their team.
What should you include in the recommendation?I picked C here. Supervision policies sound like they’d watch for users inviting others outside their department, which matches the monitoring vibe. Might not be a full block though, so maybe I’m off. Anyone else think C?

