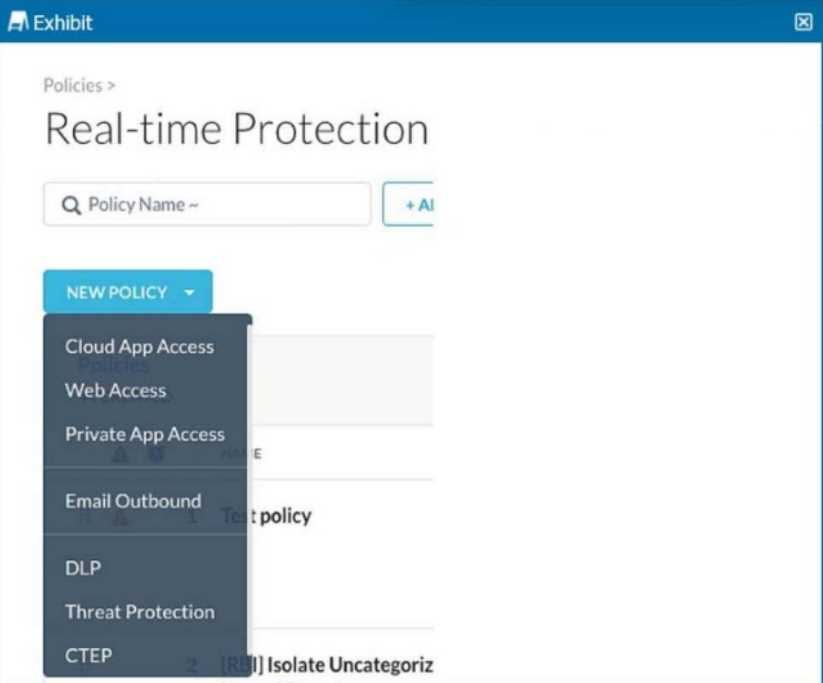
 You are asked to create a new Real-time Protection policy to scan SMTP emails using data loss
prevention (DLP) for personal health information (PHI). The scope is limited to only emails being sent
from Microsoft Exchange Online to outside recipients.
You are asked to create a new Real-time Protection policy to scan SMTP emails using data loss
prevention (DLP) for personal health information (PHI). The scope is limited to only emails being sent
from Microsoft Exchange Online to outside recipients.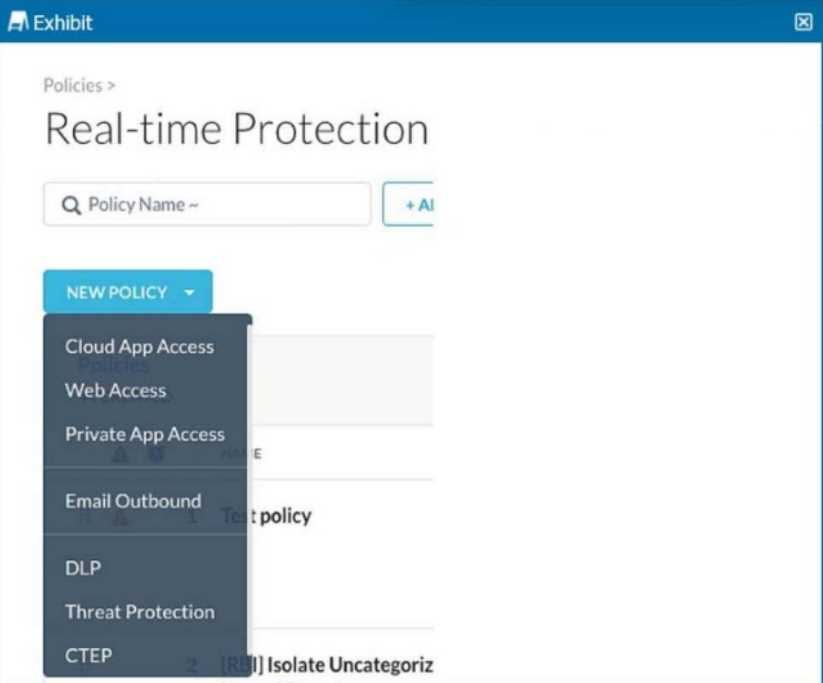 You are asked to create a new Real-time Protection policy to scan SMTP emails using data loss
prevention (DLP) for personal health information (PHI). The scope is limited to only emails being sent
from Microsoft Exchange Online to outside recipients.
You are asked to create a new Real-time Protection policy to scan SMTP emails using data loss
prevention (DLP) for personal health information (PHI). The scope is limited to only emails being sent
from Microsoft Exchange Online to outside recipients.Not B, A makes more sense for filtering Netskope client logs. Tunnel (B) is a trap since that grabs VPN/GRE/IPsec stuff, not the agent events. Using access_method "Client" narrows it down right to what the question asks. Pretty sure that's what Skope IT expects here, unless they're wording is weird.
I'd say C here since normalizing the numbers to 16 digits might help with detection. Maybe the DLP's not picking up patterns because non-standard formatting is being used in your test data? Not totally positive since it could be a validity issue too, but worth considering. Agree?
Yeah, C is tempting but pretty sure it's just a distractor. The DLP policy actually runs the Luhn check for validity, so you won’t see hits unless your sample data contains real, mathematically valid card numbers. That’s B for this one. If anyone’s seen test hits with just any 16 digits, let me know.
I don’t think C works here. With Netskope's DLP, the identifier isn’t just looking for 16-digit strings, it actually runs the Luhn check to make sure they’re true card numbers. So only B explains why no hits would show up if your data doesn’t have valid numbers. Easy to overlook that trap with C. Pretty sure it’s B unless someone’s seen a different behavior in practice?
 You are asked to create a new role that allows analysts to view Events and Reports while providing
user privacy. You need to avoid directly exposing identities and user location information.
Which three fields must you obfuscate in this scenario? (Choose three.)
You are asked to create a new role that allows analysts to view Events and Reports while providing
user privacy. You need to avoid directly exposing identities and user location information.
Which three fields must you obfuscate in this scenario? (Choose three.)A/B/E is right here. User IPs and names are direct identifiers, and source location gives away user whereabouts. Option C is a trap since app names or URLs aren’t PII, and D isn’t required for privacy in this scenario. Pretty sure ABE matches what similar exam questions want, but open to other views.
I’m with A, B, and E on this one. User IPs and names directly point to someone's identity, and source location info can reveal where they are. The other options don't really expose who the user is or their geo position. Pretty sure that’s what they want here but let me know if I’m missing anything.
I get why some folks say A, since ticketing is common for tracking. But I think C fits better if they're asking about assignment inside the Netskope platform. Pretty sure DLP Incident workflow is built for exactly that. Not 100 percent, open to other takes though.
Is anyone sure if Bulk CSV upload (D) actually brings in group membership, or just the user accounts? I know SCIM (A) and Directory Importer (C) do both, but pretty fuzzy on how complete D is for groups.
 A security analyst needs to create a report to view the top five categories of unsanctioned
applications accessed in the last 90 days. Referring to the exhibit, what are two data collections in
Advanced Analytics that would be used to create this report? (Choose two.)
A security analyst needs to create a report to view the top five categories of unsanctioned
applications accessed in the last 90 days. Referring to the exhibit, what are two data collections in
Advanced Analytics that would be used to create this report? (Choose two.)Yeah, it should be B and C here. Application Events gives you actions taken within cloud apps, and Page Events logs each time users hit a web app, which is perfect for usage visibility. D (Network Events) is tempting but more about raw traffic than application context, so not the best fit for app category reporting. Pretty sure this matches the exam style, but let me know if I missed something!
Feels like B and D could work here. Application Events logs what users actually do with the apps, and Network Events should capture all the underlying app connections too. Both seem relevant if you want to catch unsanctioned app categories, at least from a network visibility perspective. Open to pushback though if C is more important for category breakdowns!

