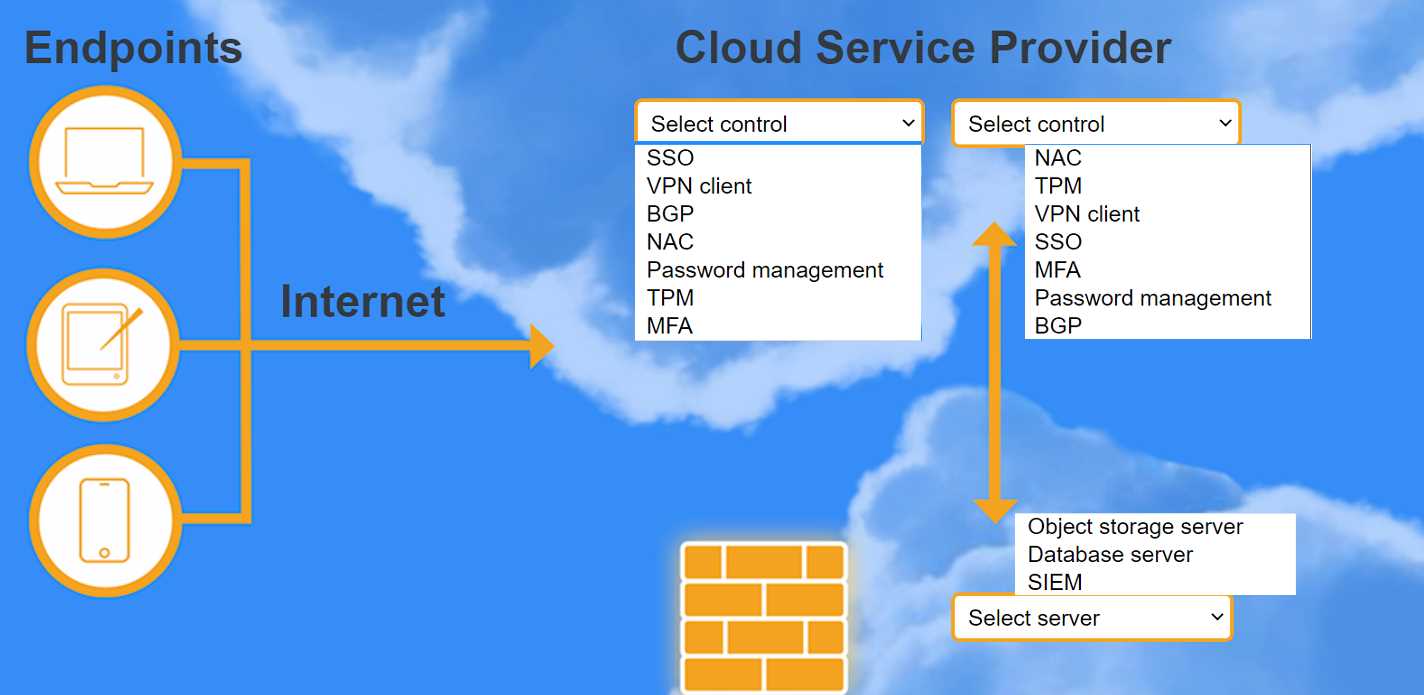
HOTSPOT A highly regulated business is required to work remotely, and the risk tolerance is very low. You are tasked with providing an identity solution to the company cloud that includes the following: secure connectivity that minimizes user login tracks user activity and monitors for anomalous activity requires secondary authentication INSTRUCTIONS Select controls and servers for the proper control points. 
Had something like this in a mock, and SSO for first control makes sense to limit user logins. MFA gives the secondary authentication they want, and SIEM is what you use to track user actions and spot weird activity. Pretty sure this covers all low risk tolerance requirements, unless compliance asks for a CASB. Agree?
SSO then MFA, with SIEM server, looks like the best combo here. SSO minimizes user logins for convenience, MFA adds the required extra layer, and SIEM's great for activity monitoring but I could see arguments for CASB instead of SIEM too if compliance focus was heavier. Pretty sure SIEM's right though. Agree?
SSO, MFA, SIEM is probably right for this. SSO helps cut down the number of logins, which is key for remote users, and MFA covers the secondary authentication requirement. With SIEM you get user activity monitoring and alerts. Pretty sure this fits the "low risk tolerance" piece but open if anyone thinks a different server should be used?