Quick Answer: Zero trust is a security framework that operates on the principle of “never trust, always verify,” requiring strict identity verification for every user and device requesting access to resources, regardless of their location. It eliminates implicit trust by assuming all users and devices are potential threats and mandates verification at every access point through least privilege access and continuous authentication. 96 percent of organizations favor a zero trust approach and 81 percent plan to implement zero trust strategies within the next 12 months. This guide explains what zero trust actually is, how it works in practice, the seven pillars every security professional needs to know, real implementation examples, and exactly how zero trust appears on Security+, CySA+, and CISSP exams. For candidates preparing for these certifications, CertEmpire’s practice exams cover zero trust architecture across all relevant exam domains with scenario-based questions built around the current blueprints.
Why Zero Trust Is the Most Important Security Concept of 2026
The average breach cost is $5.2 million, with costs 38 percent higher for organizations without zero trust implementation. 84 percent of organizations experienced identity-related breaches in 2025. 72 percent of breaches involve the exploitation of privileged credentials. Attackers spend an average of 11 days moving through networks before detection.
Every one of those statistics points to the same root cause: organizations trusted things they should not have. They trusted that users inside the network were legitimate. They trusted that devices on the corporate Wi-Fi were safe. They trusted that a valid password meant a valid user. Zero trust is the architectural response to that mistake.
The traditional perimeter-based security model has become obsolete in today’s distributed digital environment. With 82 percent of organizations now operating in hybrid or multi-cloud infrastructures and remote work becoming the standard, the concept of a secure network boundary no longer exists.
The castle-and-moat model of security assumed that everything inside the firewall was safe and everything outside was dangerous. In 2026, that assumption is demonstrably false. Employees work from coffee shops, hotels, and home networks. Applications live in AWS, Azure, and dozens of SaaS platforms. Contractors access systems through personal devices. The perimeter no longer exists. Zero trust is the security model built for that reality.
The Origin of Zero Trust: Where It Came From
The zero trust concept was originally proposed by Forrester Research analyst John Kindervag in 2010. Kindervag argued that the traditional trust-but-verify approach was flawed; attackers who managed to breach the perimeter had free access within the network. Zero trust advocated for a shift to “never trust, always verify,” pushing for authentication and authorization at every layer of access, not just the network edge. Since its inception, zero trust has evolved in response to increased cloud adoption, remote work, and the proliferation of mobile devices.
The concept gained institutional momentum in 2020 when the US Executive Order 14028 on Improving the Nation’s Cybersecurity explicitly directed federal agencies to adopt zero trust architectures. NIST followed with Special Publication 800-207, which remains the authoritative reference framework for zero trust implementation. By 2026, zero trust has moved from a conceptual framework to an operational requirement for organizations in regulated industries.
The Three Core Principles of Zero Trust
Every zero trust implementation, regardless of the vendor, technology stack, or organization size, is built on three foundational principles. Understanding these principles is more important than memorizing any specific product or tool.
Principle 1: Never Trust, Always Verify
No user, device, or application is trusted by default, even if they are inside the network perimeter. Every access request undergoes authentication and authorization regardless of origin.
In a traditional security model, a user who authenticated at the VPN was then trusted for the entire session. They could move freely between systems because the initial verification at the perimeter was treated as sufficient. Zero trust eliminates this session-based trust. Every access request to every resource is independently verified, even if the user authenticated five minutes ago and is accessing the same application they use every day.
This principle explains why zero trust is sometimes called identity-centric security. Identity, not network location, is the new security boundary. A user connecting from inside the corporate office gets the same verification treatment as a user connecting from a coffee shop in a different country.
Principle 2: Least Privilege Access
Users and devices are granted only the minimum permissions necessary to perform their specific task, reducing the potential damage from a compromised account.
Least privilege is not a new concept in security but zero trust operationalizes it more aggressively than traditional models. In practice this means users receive access only to the specific application they need for a specific task, not the entire network segment that application sits on. When the task is complete, just-in-time access provisioning removes the elevated permissions automatically. No standing administrator access. No broad database permissions for accounts that only need to read one table.
The practical impact of least privilege on breach damage is significant. When an account is compromised, the attacker can only reach what that account was authorized to access. In an environment with broad permissions, a single compromised credential gives an attacker access to everything. In a zero trust environment, the same compromised credential gives an attacker access to very little.
Principle 3: Assume Breach
Assume breach is the practice of designing security architectures with the expectation that cyber adversaries already have access to the internal environment. Rather than focusing solely on keeping attackers out, this principle demands strategies and controls that identify, contain, and mitigate threats once the perimeter is breached. Continuous monitoring, rapid response mechanisms, and constant validation of identities and behaviors are key elements.
Assume breach is the most psychologically challenging principle for organizations to internalize. Security teams have historically operated with the goal of keeping attackers out. Assume breach says that goal alone is insufficient. Even if your perimeter controls are perfect, you must design your internal architecture as if an attacker is already present.
This principle drives the emphasis on microsegmentation in zero trust. If an attacker is assumed to already have a foothold somewhere in the network, the architecture must limit how far they can move from that foothold. Every internal segment boundary becomes a potential containment barrier.
The 7 Pillars of Zero Trust
The widely accepted 7 pillars of zero trust form the foundation of a mature security architecture: Identity, Devices, Network, Applications, Data, Infrastructure, and Visibility.
Pillar 1: Identity
Identity is the foundation of the entire zero trust model. In 2026, organizations will increasingly adopt solutions powered by machine learning, artificial intelligence, and real-time analytics to enforce zero trust identity management, significantly reducing the risk of unauthorized access.
Identity verification in zero trust goes beyond a username and password. It includes multi-factor authentication as a baseline requirement, contextual analysis that evaluates where the user is connecting from, what device they are using, what time of day it is, and what behavior patterns they normally exhibit. Risk-based authentication adjusts the verification requirements in real time based on the assessed risk level of the request.
Identity and access management systems including Microsoft Entra ID, Okta, and Ping Identity are the primary tools implementing this pillar. The goal is a single authoritative identity source that governs every access decision across every system.
Pillar 2: Devices
Every device requesting network access must be verified as healthy and compliant before access is granted. Multi-factor authentication remains the strongest control when it comes to stopping an attack and reducing the likelihood of an incident.
Device verification checks include whether the device has current security patches applied, whether endpoint protection software is installed and active, whether the device belongs to the organization’s inventory, whether disk encryption is enabled, and whether the device configuration meets the organization’s security baseline.
A user who authenticates perfectly with valid credentials from a personal device that has not been patched in six months should receive either no access or significantly reduced access compared to the same user on a compliant managed device. The device health signal is an independent factor in the access decision, not just the user identity.
Pillar 3: Network
Zero trust replaces the concept of a trusted internal network with microsegmentation. Fine-grained access controls and data segmentation prevent over-privileged access and support enforcement of policies like least privilege and need-to-know.
Microsegmentation divides the network into small zones, each requiring separate authentication and authorization to access. An attacker who compromises a workstation in the HR segment cannot use that foothold to reach the finance database or the engineering source code repository without going through separate verification for each.
Zero Trust Network Access (ZTNA) is the technology category that implements this pillar. ZTNA replaces traditional VPNs by providing application-specific access rather than network-level access. Instead of connecting a remote user to the entire corporate network, ZTNA connects them directly and only to the specific application they need. 65 percent of organizations plan to replace VPN services within the year, a 23 percent jump from the prior year’s findings.
Pillar 4: Applications
Applications themselves become access control enforcement points in a zero trust architecture. Application-level access controls ensure that even users who have authenticated to the network can only access specific application functions that their role requires.
Web application firewalls, API gateways, and application-aware firewalls implement access policies at the application layer. A customer service representative authenticated to the CRM system can view customer records but cannot export them to an external file, even though both actions are technically possible within the same application.
Pillar 5: Data
Data is the ultimate target of most attacks. Zero trust data protection controls govern who can access, copy, modify, or exfiltrate specific data regardless of where it resides.
Continuous monitoring and logging enable detailed auditing and real-time alerts on suspicious activity, supporting compliance with regulations such as HIPAA, PCI-DSS, and GDPR.
Data classification is the foundation of this pillar. Data must be labeled by sensitivity before access controls can be meaningfully applied. Unclassified data in a zero trust environment is data that cannot be properly protected. Data loss prevention tools, rights management systems, and encryption controls implement the data pillar in practice.
Pillar 6: Infrastructure
Infrastructure covers servers, containers, virtual machines, cloud services, and IoT devices. Zero trust applied to infrastructure means that even internal administrative access to servers is mediated through privileged access workstations and just-in-time access systems rather than persistent standing administrator credentials.
Infrastructure as Code practices also fall under this pillar. Security controls built into deployment pipelines ensure that infrastructure is never deployed in a misconfigured or insecure state. Every infrastructure component is enrolled in the organization’s identity system and treated as a verified entity rather than an implicitly trusted asset.
Pillar 7: Visibility and Analytics
The zero trust approach minimizes the risk of breaches by enforcing strict access controls, minimizing the attack surface, and providing real-time monitoring. This results in a robust, adaptive security framework that protects sensitive data, reduces insider risks, and strengthens compliance with regulatory requirements.
Visibility without the ability to act on what you see is insufficient. Zero trust architectures generate enormous volumes of telemetry from every verification decision, every access attempt, and every session activity. SIEM platforms, user and entity behavior analytics tools, and extended detection and response platforms aggregate and analyze this telemetry to identify anomalies that represent compromise indicators.
This pillar is where zero trust connects directly to the work of security analysts. The continuous verification events generated by a zero trust architecture feed the monitoring systems that analysts use daily.
Zero Trust vs. Traditional Perimeter Security: The Key Differences
Understanding what zero trust replaces makes the concept clearer than any abstract description.
Trust model: Traditional security trusted everything inside the network perimeter. Zero trust trusts nothing by default regardless of location.
Authentication: Traditional security authenticated users once at the perimeter. Zero trust authenticates continuously for every resource access request.
Access scope: Traditional security granted network-level access after authentication. Zero trust grants application-specific access only.
Lateral movement: Traditional security allowed authenticated users to move freely within the network. Zero trust contains each access to the minimum required scope, limiting lateral movement.
Failure mode: When traditional perimeter security fails, the attacker has broad access to everything inside. When zero trust architecture contains a breach, the attacker has access only to what the compromised account was authorized to access.
Organizations completing all zero trust pillars are two times less likely to report incidents, reducing incident rates from 66 percent to 33 percent. Organizations completing the Identity pillar are nearly 11 percent less likely to have a ransomware event.
Real Zero Trust Implementation Examples
Example 1: Google BeyondCorp
Google’s BeyondCorp project is the most famous real-world zero trust implementation. After experiencing the Aurora attacks in 2010, Google redesigned its entire internal access model to eliminate the privileged internal network entirely. All Google employees access internal applications through the same mechanism regardless of whether they are in a Google office or working remotely. Access decisions are based on device compliance, user identity, and contextual signals rather than network location.
The result is that Google has no internal network that grants elevated trust. A laptop in a Google headquarters office receives the same verification as a laptop in a coffee shop because network location is irrelevant to the access decision.
Example 2: US Federal Government
Following the SolarWinds breach in 2020 and Executive Order 14028 in 2021, US federal agencies were directed to implement zero trust architectures. CISA published the Zero Trust Maturity Model as the implementation guide. Agencies are now required to achieve specific zero trust maturity levels across all seven pillars by defined deadlines.
This federal mandate has accelerated zero trust adoption across the defense contractor ecosystem because contractors handling federal data must align with federal security requirements.
Example 3: Healthcare Organization
A major healthcare system implemented zero trust in response to a ransomware attack that spread across their entire network from a single compromised workstation. The implementation focused on microsegmentation between clinical systems and administrative systems, device health verification before any access to patient records, and just-in-time privileged access for system administrators.
After implementation, a subsequent ransomware attempt that successfully compromised a workstation in the administrative network was contained entirely within that segment and never reached clinical systems or patient data.
Zero Trust and AI: The 2026 Evolution
Zero Trust AI Security integrates two transformative approaches to cybersecurity: the zero trust security model and artificial intelligence-driven threat detection and response. This combination creates a dynamic security posture that continuously validates, monitors, and adapts to emerging threats.
The integration of AI into zero trust architectures in 2026 is changing how verification decisions are made. Traditional zero trust systems applied static policy rules to access requests. AI-enhanced zero trust systems apply behavioral models that continuously update based on observed patterns.
An AI-enhanced zero trust system learns that a specific user typically authenticates from three cities, uses two devices, and accesses seven applications during business hours. When that user suddenly authenticates from a new location, uses an unrecognized device, and attempts to access fifteen applications at 3 AM, the AI model flags the anomaly and triggers additional verification or blocks access automatically, without requiring a human analyst to write a rule that anticipated exactly that scenario.
Zero trust implementation delivers an average ROI of 285 percent when AI security capabilities are integrated.
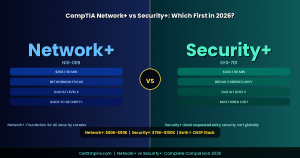
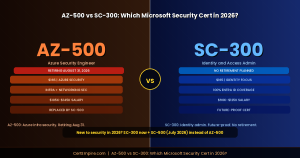
Zero Trust in Cybersecurity Certifications: What the Exams Actually Test
This is the section that most competitor pages on this topic completely miss. Zero trust appears directly on multiple major certifications and understanding how each exam tests the concept helps candidates prepare more effectively.
Security+ SY0-701
Zero trust is tested in Domain 3 (Security Architecture) at 18 percent of the exam. Specific areas include zero trust architecture design principles, the difference between zero trust and traditional perimeter models, microsegmentation implementation, and identity-aware access controls. Expect scenario questions that ask you to identify which control or architecture decision aligns with zero trust principles.
CySA+ CS0-003
Zero trust appears in Domain 1 (Security Operations) as part of monitoring and detection strategy. The exam tests whether candidates understand how zero trust telemetry feeds security monitoring, how behavioral analytics integrate with continuous verification, and how microsegmentation affects incident response and containment.
CISSP
Zero trust is tested most deeply in Domain 3 (Security Architecture and Engineering) and Domain 1 (Security and Risk Management). CISSP-level questions test governance and risk aspects of zero trust including how to justify a zero trust initiative to executive leadership, how to measure zero trust maturity against frameworks, and how zero trust affects organizational risk posture.
For scenario-based practice questions that test zero trust knowledge across all three exams, CertEmpire’s practice exam library provides updated question banks for Security+, CySA+, and CISSP with complete answer explanations that train the specific reasoning each exam requires.
How to Implement Zero Trust: Practical Starting Points
Zero trust works best when it is grounded in execution, not theory. A mature approach includes identifying exposure and eliminating implicit trust, continuous monitoring, and ongoing validation to ensure your zero trust strategy keeps pace with reality.
Most organizations cannot implement zero trust overnight. The practical approach follows a maturity progression.
Phase 1: Identity and Access Foundation
Start with MFA for all users, particularly administrators and anyone with access to sensitive systems. Implement single sign-on to consolidate identity verification at a central point. Deploy conditional access policies that evaluate device health and user context before granting access. This phase alone addresses the majority of credential-based attack vectors.
Phase 2: Device Compliance and Visibility
Deploy endpoint management to establish device health baselines. Enroll all managed devices in the identity platform. Create policies that deny or restrict access from non-compliant devices. Implement endpoint detection and response to provide continuous device security monitoring.
Phase 3: Network Microsegmentation
Begin segmenting the network into logical zones based on data sensitivity and application function. Implement ZTNA to replace VPN for remote access. Apply strict access controls between segments. Log all inter-segment traffic for analysis.
Phase 4: Application and Data Controls
Implement application-level access controls beyond network-level permissions. Deploy data classification and label sensitive data. Apply data loss prevention policies to classified data. Implement just-in-time privileged access for administrative functions.
Phase 5: Continuous Monitoring and Improvement
Integrate zero trust telemetry into SIEM. Deploy user and entity behavior analytics to detect anomalies. Conduct regular access reviews to remove unnecessary permissions. Measure progress against the NIST Zero Trust Maturity Model or CISA’s framework.
Organizations should adopt a phased approach focusing on highest-risk areas first. Organizations attempting comprehensive overnight transitions typically experience implementation failures and user resistance.
Zero Trust Market: The Numbers That Matter
As of 2025, the size of the zero trust market is estimated at $38.37 billion. This market is projected to grow to $86.57 billion by 2030 with a CAGR of 17.7 percent.
The industry-wise budget for security initiatives to adopt zero trust policies is highest in software companies at 28 percent, followed by finance at 19 percent, the public sector at 19 percent, and healthcare at 17 percent.
More than 86 percent of survey respondents shared that their organizations have already begun moving to zero trust. The downside is that only 2 percent have achieved maturity across zero trust pillars.
That 2 percent maturity figure is the most important number in the market data. It means that the vast majority of organizations claiming to be implementing zero trust are in the early phases of a multi-year journey. Security professionals who understand zero trust architecture deeply are in short supply and high demand precisely because the gap between stated intent and actual implementation is so large.
Common Zero Trust Misconceptions
Zero trust is a product you buy. Zero trust is an architectural philosophy and a set of design principles. No single product delivers zero trust. Vendors who claim their product makes you zero trust are oversimplifying. Implementing zero trust requires integrating multiple capabilities across identity, devices, networks, applications, and data.
Zero trust means no trust at all. Zero trust does not mean users are never trusted. It means trust is continuously earned through verification rather than assumed based on network location. A user who passes MFA, uses a compliant device, and accesses a resource appropriate to their role will complete that access smoothly in a well-implemented zero trust environment.
Zero trust is only for large enterprises. The principles of zero trust apply at any organizational scale. MFA, least privilege, and microsegmentation are not enterprise-only concepts. Small organizations with ten employees can and should apply zero trust principles to their cloud environments and SaaS applications.
Zero trust eliminates the need for other security controls. Zero trust is an architecture, not a complete security strategy. Endpoint protection, vulnerability management, incident response capability, and security awareness training remain essential components of a mature security program that operates within a zero trust architecture.
Frequently Asked Questions
What is zero trust security in simple terms?
Zero trust security means that no user, device, or application is automatically trusted just because it is inside your network. Every request to access any resource must be verified every time, based on who is asking, what device they are using, and whether the request makes sense in context. Traditional security trusted everything inside the firewall. Zero trust trusts nothing until it is verified.
What are the three principles of zero trust?
The three core principles are never trust always verify, least privilege access, and assume breach. Never trust always verify means every access request is independently authenticated regardless of origin. Least privilege means users get only the minimum access their task requires. Assume breach means the architecture is designed to contain and limit damage as if an attacker is already present.
Is zero trust the same as VPN?
No. A VPN connects a remote user to the entire corporate network and trusts them once authenticated. Zero trust network access connects a user directly to a specific application without granting broad network access. 65 percent of organizations plan to replace VPN services within the year as part of their zero trust adoption.
How does zero trust appear on Security+ exam?
Zero trust is tested in Security+ Domain 3 (Security Architecture) at 18 percent of the exam. Questions test zero trust design principles, the difference from perimeter security, and which controls implement zero trust concepts including microsegmentation, identity-aware access, and continuous verification.
What is the biggest challenge in implementing zero trust?
The biggest challenges include cultural resistance from employees and IT staff who perceive new controls as obstacles, integration complexities with legacy systems that lack modern authentication capabilities, and cost and resource requirements for comprehensive implementation. The technical challenges are solvable. The organizational and cultural challenges require executive sponsorship and change management investment.
Which organizations must implement zero trust?
US federal agencies are required to implement zero trust under Executive Order 14028. Defense contractors handling federal data must align with federal zero trust requirements. Regulated industries including healthcare, finance, and critical infrastructure are increasingly subject to compliance requirements that effectively mandate zero trust controls even when the term is not used explicitly.