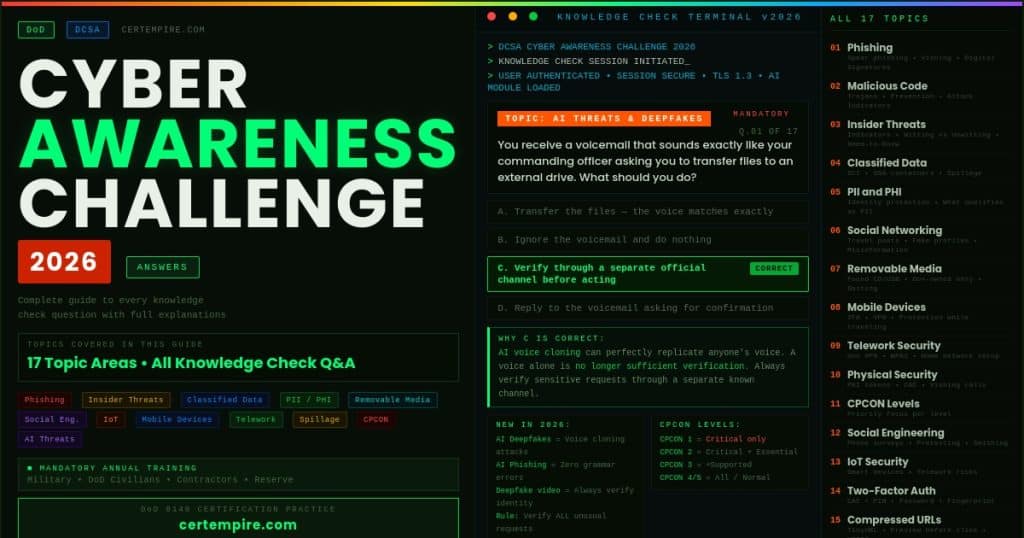
Quick Answer: The DoD Cyber Awareness Challenge 2026 Knowledge Check covers 17 topic areas including phishing, malicious code, insider threats, classified data, PII, social networking, removable media, mobile devices, telework, physical security, social engineering, IoT security, and newly expanded AI-based threats. This guide walks through every question category with the correct answers and the reasoning behind each one so you pass the knowledge check and actually understand the material. If your role also requires a formal DoD 8140 certification such as CompTIA Security+ or CEH, CertEmpire has practice exams for every approved credential in the framework.
What Is the Cyber Awareness Challenge 2026
The Cyber Awareness Challenge is mandatory annual training developed by the Defense Counterintelligence and Security Agency (DCSA). Its purpose is to educate DoD personnel on protecting government systems and sensitive information from evolving threats including phishing, social engineering, insider risks, malware, data spillage, and in the 2026 version, AI-generated attacks.
The training is required for all active duty military personnel across all branches, Department of Defense civilian employees, government contractors with access to DoD networks or data, Reserve and National Guard members, and individuals sponsored for access to DoD systems.
The knowledge check at the end of the training draws questions from every topic area covered. This guide covers every topic with the correct answers and complete explanations so you understand the reasoning, not just the answer letter.
What Changed in the 2026 Version
The 2026 Cyber Awareness Challenge introduced meaningful updates compared to the 2025 version. The core topic areas remain consistent but the training now explicitly addresses AI-generated phishing emails, deepfake audio and video used in social engineering, large language model abuse in spear phishing campaigns, and updated guidance on handling AI-generated content in government communications.
The physical security and mobile device sections also received updated scenarios reflecting current threat patterns. The CPCON section remains unchanged in structure but includes updated threat context. If you completed the 2025 version, expect approximately 20 percent new or updated question scenarios.
For personnel who need to go beyond awareness training and prepare for a formal cybersecurity certification under DoD 8140, CertEmpire’s all exams preparation material library covers Security+, CySA+, CISSP, CEH, and every other credential on the approved list.
How the Knowledge Check Works
The knowledge check is not a trick exam. Every question maps directly to a scenario or principle covered in the training content. Questions are presented in multiple choice format. The training allows you to retake the knowledge check if you do not pass on the first attempt.
The most important thing to understand before starting: the correct answer is almost always the most cautious, security-conscious option available. When in doubt between two answers, choose the one that involves reporting to your security point of contact, verifying through an official channel, or taking no action on the suspicious item.
Topic 1: Phishing
Phishing remains the most heavily tested topic in the Cyber Awareness Challenge and the most common real-world attack vector against DoD personnel.
Q: John receives an email about a potential shutdown of a major social service unless a petition receives enough signatures. Which of the following actions should John NOT take with the email?
Answer: Forward it.
Forwarding a potential phishing email spreads it to additional recipients and potentially spreads malware or social engineering content. Even if the email appears legitimate, forwarding unverified content is never the correct action. Delete it or report it to your security point of contact.
Q: You receive an email with a link to run an anti-virus scan. Your IT department has not sent links like this in the past. The email is not digitally signed. What action should you take?
Answer: Report the email to your security POC or help desk.
Two red flags are present: the email is not digitally signed, and the request is unexpected. Legitimate IT communications use digitally signed government email. When an email does not match established patterns and lacks a digital signature, treat it as a phishing indicator. Never click links in suspicious emails.
Q: You receive an email marked important from your agency head asking you to call them using a number you do not recognize. The email was sent from a personal email address, but it addresses you by name. What action should you take?
Answer: This may be a spear phishing attempt. Report it to your security POC or help desk.
This is a classic spear phishing scenario. Using your name is not proof of legitimacy. Attackers collect names from social media, organizational directories, and previous breaches. An unrecognized personal address and unknown phone number are clear red flags regardless of how personalized the message appears.
Q: Which of the following is an appropriate use of government email?
Answer: Using a digital signature when sending hyperlinks.
Digital signatures authenticate the sender and verify the email has not been tampered with in transit. This is the DoD standard for email trust and is especially important when sending links.
Topic 2: AI-Generated Threats (New in 2026)
This is the most significant new topic area in the 2026 version. DCSA added explicit coverage of AI-assisted attacks in response to the rapid proliferation of tools capable of generating convincing fake audio, video, and written content.
Q: You receive a voicemail from what sounds exactly like your commanding officer asking you to transfer files to an external drive immediately. What should you do?
Answer: Verify the request through an official, separate channel before taking any action.
AI-generated voice cloning can produce audio indistinguishable from a real person’s voice using only a few seconds of source material. A voice alone is no longer sufficient verification for a sensitive request. Always verify through a separate official channel such as calling back on a known number or confirming in person.
Q: Which of the following is a potential indicator that a video call participant may be using a deepfake?
Answer: All of the above.
Deepfake indicators include unnatural blinking or facial movement, audio that does not perfectly sync with lip movement, inconsistent lighting on the face versus the background, unusual pixelation around the edges of the face or hair, and responses that seem slightly delayed or misaligned with the conversation. No single indicator is conclusive, but multiple indicators together warrant verification.
Q: An email arrives that is perfectly written, contains no spelling errors, references accurate details about your organization, and asks you to click a link. Which of the following is true?
Answer: AI-generated phishing emails can be grammatically flawless. Absence of errors is not a reliable indicator of legitimacy.
Traditional phishing detection advice included looking for poor grammar and spelling errors. AI language models have eliminated that indicator. The 2026 training explicitly addresses this shift. Evaluate emails based on the sender address, digital signature, unexpectedness of the request, and whether the link destination can be verified, not grammar quality alone.
Topic 3: Malicious Code
Q: How can you prevent viruses and malicious code?
Answer: Scan all email attachments.
Scanning all email attachments before opening them is the primary behavioral defense against malware delivered via email. This applies regardless of whether the sender appears legitimate, because attackers can compromise trusted accounts.
Q: Which of these is NOT a potential indicator that your device may be under a malicious code attack?
Answer: An operating system update.
Operating system updates are legitimate scheduled events. Genuine malware indicators include unexpected slowdowns, programs opening or closing without user input, unusual outbound network activity, unfamiliar processes in task manager, and unexpected changes to files or settings.
Q: How can malicious code do damage?
Answer: All of these.
Malicious code can corrupt or delete files, steal sensitive data, provide unauthorized remote access, disrupt system operations, spread to other systems on the network, and log keystrokes to capture passwords. The answer all of these reflects the broad capability of modern malware.
Q: Which of the following is an example of malicious code?
Answer: Trojan horses.
A Trojan horse disguises itself as legitimate software to trick users into installing it, then executes malicious functions once installed. Other examples include viruses, worms, ransomware, spyware, and rootkits.
Topic 4: Insider Threats
Q: What is an insider threat?
Answer: Someone who uses authorized access, either wittingly or unwittingly, to harm national security.
The key word is authorized. An insider threat is not an external attacker breaking in. It is someone who already has legitimate access and uses it harmfully, whether deliberately or accidentally.
Q: An individual who has attempted to access sensitive information without need-to-know and has made unusual requests for sensitive information is displaying indicators of what?
Answer: Potential insider threat.
Both behaviors are documented insider threat indicators. Neither alone is necessarily conclusive, but together they warrant reporting to a supervisor or security officer.
Q: Based on the description provided, how many insider threat indicators are present? Edward has worked for the DoD agency for 2 years. He takes a great deal of interest in his work and occasionally asks for classified details of colleagues’ projects. He otherwise gets along well with coworkers.
Answer: 1 to 2.
Asking for classified details of others’ projects beyond assigned responsibilities is an insider threat indicator. The general work interest and positive colleague relationships are not indicators. The aggressive interest in others’ classified work is the red flag.
Topic 5: Classified Data
Q: Which of the following is a way to protect classified data?
Answer: Store it in a GSA-approved container.
GSA-approved containers are specifically certified to protect classified materials from unauthorized access. Using an unauthorized storage location does not meet the regulatory requirement regardless of how secure it appears.
Q: What are the requirements for access to Sensitive Compartmented Information (SCI)?
Answer: Top Secret clearance and indoctrination into the SCI program.
SCI requires more than a Top Secret clearance. Personnel must also be specifically indoctrinated into the SCI program through additional screening and a formal briefing process.
Q: Which of the following is true of working within a Sensitive Compartmented Information Facility (SCIF)?
Answer: Badges must be worn while in the facility and removed when leaving.
Physical badge discipline is a core SCIF requirement. Badges must be visible at all times inside to allow personnel to verify others’ authorization. Removing the badge when leaving prevents unauthorized use outside the facility.
Q: Peter enters an empty conference room and finds a document with a Top Secret coversheet. Peter has a Secret clearance. What should Peter do?
Answer: Immediately notify his security POC and not handle the file.
Peter does not have the clearance to access Top Secret material. Handling the document in any way constitutes unauthorized access. Leave it in place and notify the security POC immediately.
Topic 6: Personally Identifiable Information (PII) and Protected Health Information (PHI)
Q: Which of the following is a best practice to protect your identity?
Answer: Ask how information will be used before giving it out.
Before providing personal information to any party, ask how it will be used, who will access it, and whether providing it is necessary. This reduces the amount of personal information in circulation that can be exploited.
Q: When linked to a specific individual, which of the following is NOT an example of PII?
Answer: Smartphone brand and model.
A smartphone brand and model does not identify a specific individual and is not PII even when associated with a person. PII includes information that can identify, locate, or contact an individual such as name, address, Social Security number, date of birth, or phone number.
Q: Which of the following is an example of Protected Health Information (PHI)?
Answer: An individual’s medical record maintained by a healthcare provider.
PHI is health information linked to a specific individual and maintained by a healthcare provider, health plan, or their business associates.
Topic 7: Social Networking
Q: How can you protect yourself on social networking sites?
Answer: Validate connection requests through another source if possible.
Attackers create fake profiles of people you know to gain access to your network and the information visible to your connections. Verify connection requests through another channel before accepting.
Q: What information should you avoid posting on social networking sites?
Answer: All of the above.
Multiple categories of information should be avoided including travel plans, work assignments, organizational information, personal details that could facilitate identity theft, and information about colleagues or operations.
Q: When is the safest time to post on social media about your work-related travel?
Answer: After returning from travel.
Posting before or during travel creates operational security risks. Adversaries can use travel announcements to identify when personnel are away, potentially vulnerable, or in specific geographic locations.
Topic 8: Removable Media and Portable Electronic Devices
Q: Which of the following is true of removable media and portable electronic devices?
Answer: They cannot be adequately secured, so they are prohibited by the DoD.
Personally owned removable media and portable devices introduce uncontrolled pathways for data exfiltration and malware. Because they cannot be adequately secured to DoD standards, they are generally prohibited.
Q: You are having lunch at a local restaurant and find a CD labeled “favorite songs.” What should you do?
Answer: Leave the CD where it is.
This is a baiting attack scenario. Malicious actors deliberately place infected media in public locations hoping curious individuals will plug them into a system. Never insert unknown media into any device.
Q: A coworker has left an unknown CD on your desk. What should you do?
Answer: Give it to your security point of contact.
Do not plug it in. Give it to your security POC who can assess it appropriately.
Topic 9: Mobile Devices
Q: How can you protect data on a mobile device?
Answer: Use two-factor authentication.
Two-factor authentication requires both something you know and something you have or are. This significantly reduces the risk of unauthorized access if the device is lost or stolen.
Q: How can you protect a mobile device while traveling?
Answer: Connect with a Government VPN.
A Government VPN encrypts all traffic between your device and the network, protecting data from interception over untrusted networks such as hotel Wi-Fi, airport hotspots, or foreign cellular networks.
Topic 10: Telework and Home Computer Security
Q: Which of the following is a best practice for telework?
Answer: Connect to your Government Virtual Private Network (VPN).
Government VPN is the required connection method for accessing DoD systems remotely. It encrypts the connection between your remote location and the government network.
Q: Which of the following is a best practice for protecting your home wireless network for telework?
Answer: Implement, at a minimum, Wi-Fi Protected Access 2 (WPA2) Personal encryption.
WPA2 is the minimum acceptable wireless security standard for home networks used for telework. WPA3 is preferred where available, but WPA2 is the minimum acceptable baseline. Older protocols like WEP have known vulnerabilities.
Q: Steve occasionally runs errands during virtual meetings on his approved government device. Does this pose a security concern?
Answer: Yes. Eavesdroppers may be listening to Steve’s conversation.
Sensitive meeting content is audible in public spaces. Using an approved government device does not eliminate the risk of information exposure when attending meetings in public environments.
Topic 11: Physical Security and Access Control
Q: Which of the following is an appropriate use of a DoD PKI token?
Answer: Only leave it in a system while actively using it for a PKI-required task.
PKI tokens must never be left unattended in a system. Remove the token whenever you step away from your workstation to prevent unauthorized use of your credentials.
Q: You receive a phone call from an unknown person asking for a directory name on your government laptop so a software update can be made. What should you do?
Answer: Document the interaction and contact your security POC or help desk.
This is a vishing attack. Legitimate IT personnel do not call users to ask for directory information. Do not provide any information. Document the call details and report immediately.
Q: You receive a text message from a vendor saying your order is on hold and provides a shortened link to update payment information. What is the best course of action?
Answer: Delete the message.
This is a smishing attack. Shortened links conceal the destination URL. Legitimate vendors do not request payment updates through unsolicited texts with shortened links.
Topic 12: Cyberspace Protection Conditions (CPCON)
Q: Under which CPCON is the priority focus limited to critical functions only?
Answer: CPCON 1.
CPCON 1 is the highest protection condition indicating the most severe cybersecurity threat level. At CPCON 1, operations are restricted to only the most critical functions.
The five levels from highest to lowest threat are CPCON 1 which limits activity to critical functions only, CPCON 2 which covers critical and essential functions, CPCON 3 which covers critical, essential, and supported functions, CPCON 4 which covers all functions at a medium threat level, and CPCON 5 which represents normal readiness at a very low threat level.
Topic 13: Internet of Things (IoT)
Q: Which of the following poses a security risk while teleworking in an environment where IoT devices are present?
Answer: All of these.
Smart speakers, smart TVs, home security cameras, and connected appliances can all present security risks. They may eavesdrop on meetings, transmit data over unsecured connections, or represent vulnerable entry points into the home network.
Topic 14: Social Engineering
Q: You receive a call on your work phone asking you to participate in a phone survey. The caller asks for your birth date and address. What type of attack might this be?
Answer: Social engineering.
Phone surveys requesting personal information are a common technique used to gather data for identity theft or to build a profile enabling more targeted attacks. Decline and report.
Q: Which of the following is NOT a social engineering tip?
Answer: When using a public device with a card reader, only use your DoD CAC to access unclassified information.
DoD employees are prohibited from using a CAC in any card-reader-enabled public device regardless of classification level. This is prohibited behavior, not a tip.
Topic 15: Two-Factor Authentication
Q: Which of the following would work in combination for two-factor authentication?
Answer: Common Access Card and PIN, or password and fingerprint.
Two-factor authentication requires two different categories of credential: something you know such as a password or PIN, something you have such as a CAC or token, or something you are such as a fingerprint or face ID. Two factors from the same category do not constitute true two-factor authentication.
Topic 16: Compressed URLs and Internet Safety
Q: Which of the following is true of compressed URLs such as TinyURL?
Answer: They may be used to mask malicious intent.
Compressed URLs hide the actual destination of a link. A malicious actor can create a shortened URL that redirects to a phishing page or malware download.
Q: Which of the following is a best practice when browsing the internet?
Answer: Look for HTTPS in the URL.
HTTPS indicates the connection between your browser and the website is encrypted. Always verify HTTPS before submitting any sensitive information.
Topic 17: Spillage
Q: What is the best response if you find classified information on the internet?
Answer: Note any identifying information such as the URL and immediately report it to your security POC.
Do not download, share, or attempt to handle classified information found in an unauthorized location. Note the location and report immediately. Downloading it would itself be a security violation even with good intent.
Q: What can you do to prevent spillage?
Answer: All of the above.
Spillage prevention combines multiple behaviors: understanding classification levels before transmitting information, using only authorized systems for classified work, verifying classification before sharing, and following all handling procedures.
Common Mistakes That Cause People to Fail the Knowledge Check
Clicking through without reading the scenarios is the most common problem. The training is scenario-based for a reason. Read each scenario completely before looking at the answer options.
Choosing the most helpful answer rather than the most secure answer is the second most common mistake. The correct answer always prioritizes security over convenience. If one answer involves reporting and another involves taking action yourself, report.
Relying on 2025 instincts for the new AI threat questions. The 2026 version specifically tests whether you understand that grammar quality, voice similarity, and visual accuracy are no longer reliable indicators of legitimacy. Apply extra scrutiny to these new question types.
Assuming a supervisor or senior official’s request bypasses security rules. No rank overrides security policy. If any request from any person violates a security rule, the correct answer is to follow the security rule.
Frequently Asked Questions
How long does the Cyber Awareness Challenge 2026 take to complete?
Approximately one hour depending on how quickly you move through the interactive scenarios. The knowledge check is not separately timed.
What happens if you fail the knowledge check?
You can retake it. There is no penalty for failing on the first attempt. The training allows multiple attempts.
What is new in the 2026 version compared to 2025?
The 2026 version adds explicit coverage of AI-generated threats including deepfake audio and video used in social engineering, AI-generated phishing emails that contain no grammar errors, and voice cloning attacks. Updated scenarios also appear in the physical security and mobile device sections.
Who is required to complete the Cyber Awareness Challenge?
All active duty military personnel, DoD civilian employees, government contractors with access to DoD networks or systems, and Reserve and National Guard members are required to complete it annually.
Where do you access the Cyber Awareness Challenge 2026?
The training is accessed through Joint Knowledge Online at jko.jten.mil for most DoD personnel, or through your organization’s learning management system if your agency hosts it separately.
Does the Cyber Awareness Challenge count toward cybersecurity certifications?
The certificate does not replace or substitute for formal certifications such as CompTIA Security+, CEH, or CISSP. It is a mandatory awareness training requirement, not a professional certification. For formal DoD 8140 certifications, visit CertEmpire for practice exams across the full certification lineup.
Beyond Awareness Training: DoD 8140 Certifications
The Cyber Awareness Challenge is the DoD baseline for end-user awareness training. It is not a cybersecurity certification. If your role requires a formal cybersecurity certification under DoD Directive 8140, the awareness challenge does not satisfy that requirement.
DoD 8140 approved certifications by work role include Information Assurance Technical Level I which requires CompTIA A+, Network+, or Security+. Level II requires CompTIA Security+, CySA+, or SSCP. Level III requires CISSP, CISA, or CASP+. Management Level I requires Security+ or GISF. Management Level II requires CAP, CASP+, or CISM. System Architect and Engineer positions require CISSP-ISSAP or ISSEP.
CertEmpire provides free practice exams for every DoD 8140 approved certification. If you are working toward a formal cybersecurity credential to satisfy your DoD position requirement, the CertEmpire practice exam library gives you scenario-based question banks with complete answer explanations for every exam in the 8140 framework.