🆕 New in 2026: OWASP has published its first-ever Top 10 for Agentic Applications, targeting autonomous AI agents that plan, decide, and act across enterprise systems. The EU AI Act high-risk AI requirements hit their August 2, 2026, enforcement deadline. This guide covers both, along with 8 frameworks total. The competing article only covers 4.
Why Enterprise AI Security Frameworks Matter More Than Ever in 2026
Seventy-three percent of organizations experienced an AI-related security breach last year. The average cost of each incident was $4.8 million. It takes an average of 290 days to detect these attacks. That is nearly a full year of undetected exposure.
The reason these numbers are so bad is not a lack of talent or budget. It is a lack of structure. Organizations are deploying AI systems at speed without a consistent framework for identifying threats, managing risk, or proving compliance. Security teams are building controls from scratch, in isolation, jurisdiction by jurisdiction. It is expensive, inconsistent, and ineffective.
AI security frameworks solve this. They give multinational corporations uniform guidelines for safeguarding AI systems across nations with varying legal requirements. Businesses operating in Asia-Pacific, Europe, or North America can put uniform security measures in place. They eliminate the need to reinvent security policy in every market and let teams focus on tightening defenses instead of drafting new documents from zero.
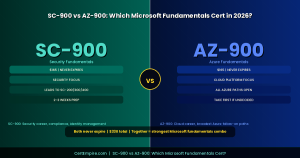
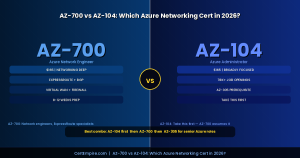
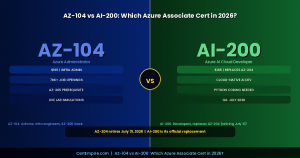
The large number of AI security frameworks and AI governance standards has created what many describe as compliance chaos for Chief Information Security Officers. With new mandates like the EU AI Act, Executive Orders on AI, and various state regulations demanding attention, CISOs face challenges that go beyond traditional security concerns. Professionals looking to validate their ability to navigate this landscape are increasingly turning to specialized credentials, and the AI security certificationsresource at Cert Empire is one of the most referenced starting points for teams building that expertise.
This guide cuts through that chaos. We cover 8 frameworks in depth, explain what each one actually does, who it is designed for, and how to layer them together. We also include a framework selection matrix, a regulatory mapping table, and a practical implementation roadmap.
The 2026 AI Threat Landscape: What Frameworks Are Protecting Against
Before choosing a framework, you need to understand what you are defending against. AI agents are no longer just assistants. They are becoming autonomous actors inside enterprise networks, creating a new and dangerous class of insider threat.
The major threat categories in 2026 are:
Prompt injection and jailbreaking remain the most common attack vector against LLM-based systems. Attackers craft inputs designed to override system instructions and manipulate model behavior.
Model poisoning involves injecting malicious data into training pipelines to corrupt model outputs at scale. Once a model is poisoned, every decision it makes is compromised.
Data exfiltration via model outputs allows sensitive training data to leak through carefully crafted inference queries, exposing personally identifiable information and intellectual property.
Adversarial machine learning uses specially crafted inputs designed to fool AI models into incorrect classifications or decisions, particularly dangerous in high-stakes applications like fraud detection and medical diagnosis.
Agentic AI threats are the newest and fastest-growing category. Rogue agents deviate from their intended function, acting harmfully or deceptively within multi-agent ecosystems. Their individual actions may appear legitimate, but emergent behavior becomes harmful, creating a containment gap for traditional rule-based security systems.
Supply chain attacks target the dependencies, datasets, third-party models, and open-source libraries that AI systems rely on. A compromised dependency can introduce vulnerabilities across every system that uses it.
No single framework addresses all of these threats. That is exactly why understanding which framework covers which threat category is the foundation of an effective enterprise AI security strategy.
The 8 Best AI Security Frameworks for Enterprises in 2026
1. NIST AI Risk Management Framework (AI RMF)
Publisher: National Institute of Standards and Technology (U.S. Government)
Type: Governance and risk management
Mandatory: Required for U.S. federal agencies; voluntary but widely adopted across regulated industries
Best For: CISOs and security leaders building enterprise-wide AI risk programs
What It Is
The NIST AI RMF has become the practical backbone of AI assurance, long before any binding regulation takes effect. It is the most widely adopted AI risk management framework globally and serves as a common language connecting technical teams, risk managers, and regulators.
The framework is built around four core functions:
Govern establishes the policies, processes, and accountability structures that define how AI risk is owned and managed across the organization. This includes board-level reporting, risk tolerance definitions, and cross-functional ownership of AI risk.
Map requires organizations to document the context of each AI system: what data it uses, what decisions it makes, who is affected, and what the potential harms are. This inventory becomes the foundation for everything else.
Measure focuses on testing and evaluation. It requires red-teaming environments for adversarial testing before deployment, bias detection pipelines feeding into centralized evaluation harnesses, and automated escalation playbooks that activate when safety or performance thresholds are exceeded.
Manage turns measurement into action. It covers how organizations respond to identified risks, prioritize remediation, and maintain ongoing oversight of deployed AI systems.
Key Strengths
The NIST CSF 2.0 no longer just identifies and protects assets. It now emphasizes explicit cyber risk ownership, alignment with enterprise risk tolerance, and executive and board-level decision accountability.
The NIST Risk Management Framework establishes a governance structure that is essential for regulatory compliance. Its strength lies in mapping regulatory demands across different jurisdictions and providing a common language to discuss AI compliance and risk.
Key Limitation
The framework relies on a catalog of over 1,000 controls (NIST SP 800-53), which can be overwhelming. The key is focusing on 20% of the controls that mitigate 80% of risk.
Implementation Starting Point
Begin with the Map function. Create a living inventory of every AI model your organization uses, including the data it trains on, the decisions it influences, and the teams accountable for it. This single artifact unlocks 80% of the subsequent framework activities.
2. OWASP Top 10 for Large Language Models (LLM Top 10)
Publisher: Open Worldwide Application Security Project (global non-profit)
Type: Technical security checklist for LLM applications
Mandatory: Voluntary but rapidly becoming the baseline for enterprise AppSec programs
Best For: Security engineers, DevSecOps teams, and application security professionals building or deploying LLM-based applications
What It Is
Adoption has been rapid, emerging as the baseline security checklist for GenAI and agentic AI systems, referenced in enterprise AppSec programs, cloud provider guidelines, and AI assurance reports. OWASP’s open-source model makes it uniquely valuable for enterprises: it transforms cutting-edge research and attack intelligence into actionable, testable controls.
The 10 vulnerabilities currently defined by OWASP for LLMs include:
LLM01: Prompt Injection is the most critical vulnerability. Attackers manipulate LLM inputs to override instructions, bypass safety controls, or exfiltrate data. Direct injection targets the model directly. Indirect injection embeds malicious instructions in content the model processes, such as documents, web pages, or emails.
LLM02: Insecure Output Handling occurs when LLM outputs are passed to downstream systems without proper validation, enabling code execution, XSS, or SQL injection via model responses.
LLM03: Training Data Poisoning involves compromising the integrity of training data to introduce backdoors, bias, or vulnerabilities into the model itself.
LLM04: Model Denial of Service uses resource-intensive queries to degrade model performance or availability.
LLM05: Supply Chain Vulnerabilities cover risks in the models, datasets, and third-party components LLM applications depend on.
LLM06: Sensitive Information Disclosure occurs when models reveal confidential training data, proprietary information, or user data through carefully crafted queries.
LLM07: Insecure Plugin Design targets vulnerabilities in plugins and extensions that LLMs use to access external systems.
LLM08: Excessive Agency happens when LLMs are given too much autonomy to take actions, without sufficient oversight or constraints.
LLM09: Overreliance refers to the risk of organizations depending on LLM outputs without appropriate human oversight or validation.
LLM10: Model Theft covers attacks designed to extract model weights, architecture, or training data through repeated queries.
Key Strengths
Immediately actionable. Each vulnerability comes with concrete mitigation guidance that engineering teams can implement now. It is also free and continuously updated by a global community of practitioners.
Key Limitation
OWASP LLM Top 10 is a threat awareness document, not a governance framework. It tells you what to fix, not how to build the organizational program around fixing it. Pair it with NIST AI RMF for governance and MITRE ATLAS for adversary modeling.
3. OWASP Agentic AI Top 10 (New in 2026)
Publisher: Open Worldwide Application Security Project
Type: Security risk framework for autonomous AI agent systems
Mandatory: Voluntary; just published in early 2026
Best For: Security teams deploying autonomous AI agents in production environments
What It Is
OWASP has published its first-ever Top 10 for Agentic Applications, identifying the most critical security risks for AI agents that plan, decide, and act autonomously. Agentic AI systems amplify traditional LLM vulnerabilities through multi-step reasoning, tool access, and inter-agent communication.
This is the newest framework on this list and one of the most important for 2026. As organizations move from simple LLM chatbots to autonomous agents that take actions on behalf of users, the threat surface changes dramatically.
The three overarching principles from the OWASP Agentic Top 10 are:
Go beyond least privilege. Avoid deploying agentic behavior where it is not needed. Unnecessary autonomy expands the attack surface without adding value. Every tool, permission, and delegation chain should be justified by a clear business requirement. Require human approval for high-impact, irreversible, or privilege-escalating actions. Implement adaptive trust calibration that adjusts agent autonomy based on contextual risk scoring.
Key risks covered include Rogue Agent behavior, where agents deviate from intended function within multi-agent ecosystems; autonomous data exfiltration; self-replication via provisioning APIs; and reward hacking that leads to critical data loss.
Key Strengths
The first framework to specifically address the agentic AI threat category in a structured, actionable way. If your organization is deploying AI agents in production, this is required reading.
Key Limitation
Very new. Organizational adoption, tooling support, and implementation guidance are still maturing. Treat it as an essential risk awareness layer, not a complete governance program.
4. MITRE ATLAS (Adversarial Threat Landscape for AI Systems)
Publisher: MITRE Corporation (U.S. federally funded research center)
Type: Adversary knowledge base for AI and ML systems
Mandatory: Voluntary; widely adopted for red teaming and threat modeling
Best For: Red teams, penetration testers, threat intelligence analysts, and security architects
What It Is
MITRE ATLAS transforms AI security by addressing unique vulnerabilities like prompt injection and model extraction. The framework’s 14 tactics help organizations anticipate attacks and build resilient defenses.
MITRE ATLAS is the AI equivalent of MITRE ATT&CK, the framework used to classify cyberattack techniques against traditional IT systems. Where ATT&CK focuses on network, cloud, and endpoint attacks, ATLAS focuses on the AI and machine learning ecosystem.
MITRE ATT&CK focuses on traditional cybersecurity threats against enterprise networks, cloud, and mobile systems. MITRE ATLAS is specifically designed for the AI and ML ecosystem, addressing unique vulnerabilities like data poisoning and model extraction that traditional security frameworks do not cover.
The framework documents real-world adversarial tactics and techniques used against AI systems. It includes:
Techniques such as data poisoning (introducing malicious data into training sets), prompt injection, model inversion (recovering training data from model outputs), and model evasion (crafting adversarial inputs that fool models).
Tactics that represent the high-level goals of an attacker: reconnaissance against AI systems, resource development for ML attacks, initial access to AI infrastructure, and impact through corrupted model behavior.
Case studies based on real-world AI attacks, which provide concrete scenarios for threat modeling exercises and red team engagements.
Key Strengths
Use MITRE ATLAS techniques to threat-model each critical workflow. This exercise often uncovers data-poisoning paths that traditional reviews miss. The framework integrates naturally with existing ATT&CK-based security operations, making adoption easier for teams already using ATT&CK.
Key Limitation
ATLAS is an offensive knowledge base, not a governance framework. It tells you how attacks happen and where to look for them. Combine it with NIST AI RMF for governance and OWASP LLM Top 10 for application-level controls.
5. ISO/IEC 42001 (AI Management Systems Standard)
Publisher: International Organization for Standardization (ISO)
Type: Certifiable international standard for AI management systems
Mandatory: Voluntary globally; increasingly required by enterprise procurement and regulated industries
Best For: Large enterprises and multinationals seeking formal third-party certification of AI governance
What It Is
ISO/IEC 42001 is the first international standard that organizations can certify to for AI Management Systems (AIMS). Unlike optional frameworks, this standard allows companies to secure third-party certification, offering concrete proof of compliance to regulators, customers, and stakeholders alike. It is part of an extensive set of over 40 AI-related standards under development by SC 42, addressing areas like data, models, and governance.
ISO 42001 is the AI governance equivalent of ISO 27001 for information security. Organizations that have already implemented ISO 27001 will find significant structural overlap, making adoption considerably easier.
The standard covers the entire AI management lifecycle: establishing an AI policy, defining roles and responsibilities, conducting AI risk assessments, implementing controls, measuring performance, and continuously improving the AI management system through internal audits and management reviews.
Key Strengths
ISO 27001 continues to serve as the formal assurance mechanism for information security programs, particularly when certification, customer trust, or regulatory signaling is required. The same logic applies to ISO 42001 in the AI domain. When you need to prove AI governance maturity to enterprise customers, regulators, or partners, third-party certification against this standard is the strongest signal available.
Organizations already using NIST’s Cybersecurity Framework can integrate the 2025 Cyber AI Profile into their existing security strategies, embedding AI risk management into broader enterprise operations rather than treating it as a standalone issue.
Key Limitation
ISO/IEC 42001 demands well-structured organizational processes. It is documentation-heavy and requires dedicated resourcing for implementation and audit preparation. It is not suitable as a first framework for organizations just beginning their AI security journey. Build operational maturity with NIST AI RMF first, then formalize it with ISO 42001 certification.
6. EU AI Act
Publisher: European Union
Type: Legally binding regulation with enforceable requirements
Mandatory: Yes, for organizations operating in or serving the EU market
Best For: Legal, compliance, and governance teams; any organization with EU market exposure
What It Is
The EU AI Act is not a framework in the traditional sense. It is law. As the first comprehensive AI regulation worldwide, it sets a global benchmark that influences emerging standards. By 2026, half of all governments are expected to mandate enterprise compliance with AI laws.
The Act uses a risk-tiered model. AI systems are classified into four categories:
Unacceptable risk systems are prohibited entirely. These include AI used for social scoring, real-time biometric surveillance in public spaces, and systems that exploit psychological vulnerabilities.
High-risk systems face the most stringent requirements. This includes AI used in critical infrastructure, employment decisions, credit scoring, law enforcement, and medical devices. High-risk AI requirements hit their August 2, 2026 enforcement deadline.
Limited risk systems must meet transparency requirements. Chatbots must disclose they are AI. Deepfakes must be labeled.
Minimal risk systems face no additional obligations beyond existing law.
For high-risk AI systems, enterprises must demonstrate full data lineage tracking, knowing exactly what datasets contributed to each model’s output; human-in-the-loop checkpoints for workflows impacting safety, rights, or financial outcomes; and risk classification tags labeling each model with its risk level, usage context, and compliance status.
Failure to demonstrate these controls is not just an administrative issue. It can lead to forced shutdowns of production AI systems or bans on EU market access. Penalties can reach EUR 35 million or 7% of global annual turnover for prohibited practice violations.
Key Strengths
The EU AI Act creates legal accountability for AI security failures in a way no voluntary framework can. For organizations with EU operations or customers, it is the most powerful forcing function for AI security investment available.
Key Limitation
The Act defines what is required but not precisely how to implement it. Pair with NIST AI RMF and ISO 42001 to build the operational controls that satisfy EU AI Act obligations. Organizations can streamline compliance by mapping internal policies to NIST AI RMF or ISO/IEC 42001 and then aligning these to the EU’s specific requirements, reducing duplication of effort.
7. Google Secure AI Framework (SAIF)
Publisher: Google
Type: Technical security framework for AI system development and deployment
Mandatory: Voluntary
Best For: AI and ML engineering teams building and deploying AI systems at scale
What It Is
Google’s Secure AI Framework is a vendor-published framework that translates Google’s own internal AI security practices into a structured set of principles and controls. While it carries a vendor label, the substance is genuinely useful and increasingly referenced in enterprise AI security programs alongside NIST and OWASP.
SAIF is organized around six core principles:
Expand strong security foundations to the AI ecosystem by applying existing security controls (identity, access, monitoring) to AI infrastructure and extending them to cover model-specific risks.
Extend detection and response to bring AI into scope of SOC operations by building monitoring capabilities that can detect model drift, adversarial inputs, and unusual inference patterns.
Automate defenses to keep pace with threats using AI-powered security automation to counter AI-powered attacks in near real time.
Harmonize platform-level controls by ensuring that the infrastructure layer provides consistent security guarantees for AI workloads regardless of the model or application running on it.
Adapt controls to address the unique risks of AI by implementing specific controls for training data integrity, model versioning, and supply chain security.
Contextualize AI risk in surrounding business processes by mapping AI system risks to the specific business decisions and workflows they influence.
Key Strengths
Highly practical and immediately applicable to teams building on cloud infrastructure. Google has open-sourced significant guidance and tooling around SAIF, making implementation more accessible than frameworks that require expensive consultants to operationalize.
Key Limitation
As a vendor-published framework, SAIF is better suited as an operational complement to NIST AI RMF than as a standalone governance structure. It does not provide the regulatory coverage of EU AI Act or the certifiability of ISO 42001.
8. CSA AI Controls Matrix
Publisher: Cloud Security Alliance
Type: Cloud-focused AI security controls framework
Mandatory: Voluntary
Best For: Cloud security architects and teams running AI workloads across multi-cloud environments
What It Is
The CSA AI Controls Matrix is particularly strong in cloud settings, featuring 243 controls across 18 domains such as Model Security and Bias Monitoring. It remains vendor-neutral and aligns seamlessly with ISO/IEC 42001 and EU AI Act requirements, making it an excellent choice for multi-cloud environments.
The 18 domains cover areas including AI governance, data security, model lifecycle management, inference security, bias and fairness monitoring, supply chain security, and incident response for AI systems. Each domain contains specific, testable controls that security teams can map to their existing cloud security posture.
Key Strengths
The CSA AI Controls Matrix is the most operationally specific framework on this list for cloud-based AI workloads. Its 243 controls provide the granularity that teams need to actually implement and audit AI security in AWS, Azure, GCP, and hybrid environments. Its alignment with ISO 42001 and the EU AI Act means that implementing it simultaneously advances multiple compliance objectives.
Key Limitation
Primarily relevant for cloud-hosted AI workloads. Organizations running AI on-premises or in highly specialized environments may find the cloud-centric framing less applicable.
Framework Comparison: Which One Does What
| Framework | Type | Mandatory? | Hands-On Controls | Governance | Regulatory Coverage | Best Starting Point For |
| NIST AI RMF | Risk management | U.S. federal (voluntary elsewhere) | Medium | Strong | High | Any enterprise |
| OWASP LLM Top 10 | Threat checklist | No | High | None | Low | Engineering teams |
| OWASP Agentic Top 10 | Threat checklist | No | High | None | Low | Teams deploying AI agents |
| MITRE ATLAS | Adversary knowledge | No | High | None | Low | Red teams, threat modeling |
| ISO/IEC 42001 | Certifiable standard | Procurement-driven | Medium | Strong | High | Enterprises needing certification |
| EU AI Act | Law | Yes (EU market) | Low | Strong | Very High | Legal and compliance teams |
| Google SAIF | Technical framework | No | High | Low | Low | Engineering and DevSecOps |
| CSA AI Controls Matrix | Cloud controls | No | Very High | Medium | Medium | Cloud security architects |
Regulatory Mapping: Which Frameworks Satisfy Which Regulations
One of the biggest practical challenges for enterprise security teams is understanding which frameworks help satisfy which regulatory requirements. This table maps the most important 2026 AI regulations to the frameworks that address them.
| Regulation | Primary Framework | Supporting Frameworks | Key Requirements |
| EU AI Act | EU AI Act + ISO 42001 | NIST AI RMF, CSA Matrix | Risk tiering, data lineage, human oversight, audit logs |
| U.S. Federal AI Executive Order | NIST AI RMF | Google SAIF, MITRE ATLAS | Risk management, transparency, red teaming |
| GDPR (AI implications) | ISO 42001 | NIST AI RMF, OWASP LLM Top 10 | Data minimization, purpose limitation, explainability |
| DORA (EU financial sector) | NIST AI RMF + ISO 42001 | CSA Matrix | Operational resilience, incident reporting, third-party risk |
| HIPAA (healthcare AI) | NIST AI RMF | OWASP LLM Top 10, CSA Matrix | Data protection, audit controls, access management |
| SOC 2 (AI systems) | CSA AI Controls Matrix | NIST AI RMF, Google SAIF | Security, availability, confidentiality controls |
How to Choose the Right Framework: A Decision Matrix
When selecting an AI security framework, factors like your organization’s size, industry, and regulatory requirements should guide your choice.
If you are building or deploying LLM applications, start with the OWASP LLM Top 10. It gives engineering teams concrete, actionable controls they can implement immediately. Add MITRE ATLAS for threat modeling and NIST AI RMF to build the governance layer around your technical controls.
If you are deploying autonomous AI agents, the OWASP Agentic AI Top 10 is now essential reading. It is the only framework that specifically addresses the threat surface created by agents that can plan, reason, and take actions autonomously.
If you have EU operations or EU customers, compliance with the EU AI Act is not optional. Start by classifying your AI systems by risk tier, then build the governance and evidence infrastructure using NIST AI RMF and ISO 42001.
If you need formal third-party certification, ISO 42001 is the only certifiable AI management standard. Build operational maturity using NIST AI RMF first, then formalize it through ISO 42001 audit and certification.
If you run AI workloads on cloud infrastructure, the CSA AI Controls Matrix provides the most operationally specific guidance for securing cloud-hosted AI systems across AWS, Azure, and GCP.
If you are a CISO building a board-level AI risk program, NIST AI RMF is your anchor. Its Govern function provides the governance language that connects security operations, risk management, and executive reporting.
If your team conducts red teaming or adversarial testing, MITRE ATLAS is the standard reference. Use it to threat-model AI workflows and design adversarial test cases that go beyond what traditional penetration testing covers.
The Framework Stack: How to Layer Them Effectively
The most effective organizations in 2026 will not operate eight separate programs. Instead, they will adopt a single integrated operating model.
The recommended enterprise stack for most large organizations is:
Governance layer:
NIST AI RMF as the operating model, with ISO 42001 for formal certification and EU AI Act as the regulatory overlay.
Technical controls layer:
OWASP LLM Top 10 for application security controls, OWASP Agentic Top 10 for agent-specific risks, and CSA AI Controls Matrix for cloud infrastructure security.
Adversary intelligence layer:
MITRE ATLAS for threat modeling, red team exercises, and threat intelligence.
Operational layer:
Google SAIF principles embedded into the AI development lifecycle and MLOps processes.
This unified approach allows for faster decision-making, cleaner audits, improved board communication, and reduced compliance friction.
Implementation Roadmap: Where to Start
The most common mistake enterprises make when adopting AI security frameworks is trying to implement everything at once. The biggest mistake is trying to do everything at once. Here is a phased approach that works.
Phase 1 (Weeks 1 to 4): Visibility
Begin with patching the biggest holes first. Apply OWASP LLM Top-10 mitigations including prompt sanitization, output filtering, and strict dependency pinning. Create a living asset inventory using the NIST AI RMF Map function, documenting every AI model, dataset, and third-party AI service in your environment.
Phase 2 (Weeks 5 to 12): Governance
Establish a cross-functional AI governance committee with a clear RACI matrix covering security, data science, legal, and product teams. Define AI risk tolerance at the executive level. Begin mapping your controls to NIST AI RMF and identify gaps.
Phase 3 (Months 4 to 6): Controls
Use MITRE ATLAS techniques to threat-model each critical AI workflow. Implement the CSA AI Controls Matrix for cloud-hosted AI workloads. Begin the EU AI Act risk classification process for systems with EU exposure.
Phase 4 (Months 7 to 12): Formalization
If your industry demands formal proof, begin an ISO 42001 gap analysis. The earlier phases supply 80% of the evidence auditors need, making certification a documentation exercise rather than a security overhaul.
Common Implementation Mistakes to Avoid
Treating frameworks as compliance checklists rather than operating models. Frameworks must become controls: NIST AI RMF and OWASP LLM Top 10 only help when guardrails are measurable, enforceable, and continuously monitored. Checking boxes without enforcing controls gives you the cost of compliance without the benefit.
Starting with ISO 42001 before establishing operational maturity. ISO 42001 certification requires documented evidence of an operating AI management system. Organizations that attempt certification without first establishing NIST AI RMF-aligned operations fail audits and waste significant resources.
Ignoring the EU AI Act deadline. EU AI Act timelines are real: compliance requires risk-tiering, audit trails, and evidence that stands up to regulators, customers, and internal assurance. The August 2, 2026 deadline for high-risk AI systems is not a soft target.
Not accounting for agentic AI threats. Many enterprises built their AI security programs around LLM chatbots and are now deploying AI agents without updating their threat models. The OWASP Agentic AI Top 10 addresses risks that none of the older frameworks were designed to cover.
Building framework programs in isolation. Most organizations will need some combination of frameworks rather than relying on a single model. Strong governance depends on visibility: without logs, prompts, user activity, or model traces, compliance becomes guesswork.
Frequently Asked Questions
Which AI security framework should an enterprise start with?
For most enterprises, start with the NIST AI RMF. It provides a universal governance structure, maps to most regional regulatory requirements, and is flexible enough for organizations of any size. Pair it immediately with OWASP LLM Top 10 for application-level technical controls.
Is the EU AI Act a framework or a regulation?
It is a legally binding regulation, not a voluntary framework. If your organization operates in or sells to the EU market, compliance is mandatory. Voluntary frameworks like NIST AI RMF and ISO 42001 help you build the controls needed to satisfy EU AI Act requirements.
What is the difference between MITRE ATLAS and MITRE ATT&CK?
MITRE ATT&CK focuses on traditional cybersecurity threats against enterprise networks, cloud, and mobile systems. MITRE ATLAS is specifically designed for the AI and ML ecosystem, addressing unique vulnerabilities like data poisoning and model extraction that traditional security frameworks do not cover.
How do NIST AI RMF and ISO 42001 relate to each other?
They are complementary. Organizations already using NIST’s Cybersecurity Framework can integrate the 2025 Cyber AI Profile into their existing security strategies, embedding AI risk management into broader enterprise operations rather than treating it as a standalone issue. Use NIST AI RMF to build operational maturity, then use ISO 42001 to formalize and certify it.
Do small and medium enterprises need all of these frameworks?
No. NIST AI RMF is known for its adaptability. It is voluntary, applicable across various use cases, and suitable for organizations of all sizes. However, small and medium-sized enterprises may find implementation challenging due to limited resources. Start with OWASP LLM Top 10 for immediate technical controls and NIST AI RMF Govern and Map functions for governance basics. Add additional frameworks as your AI program matures.
How often should we reassess our framework alignment?
You should check your security at least every six months, or whenever your AI systems change. Given the pace of regulatory change in 2026, quarterly reviews of your regulatory mapping are also recommended.
The Bottom Line
The AI security framework landscape in 2026 is complex but navigable. The organizations that struggle are the ones trying to implement everything at once or ignoring frameworks entirely until a breach or regulator forces their hand.
The ones that succeed start with visibility: a complete inventory of their AI assets, the threats against them, and the regulatory obligations that apply. They build governance on top of that visibility using NIST AI RMF. They apply technical controls using OWASP and MITRE ATLAS. They formalize it with ISO 42001 when certification is needed. And they use the EU AI Act not as a burden but as a forcing function for exactly the kind of structured, evidence-based AI security program that protects the organization anyway.
No single framework covers everything. The right approach is a deliberate stack, not a checklist. And the professionals who build and manage those stacks need validated, up-to-date skills to do it effectively. If you are looking to certify your AI security knowledge or prepare your team for the credentials that prove it, the AI security certification resources at CertEmpire cover everything from exam prep to hands-on practice guides.