For User1 to review prompts and responses in Purview without extra permissions, I'm thinking C and E are exactly what's needed. Those roles let you see the list of items and open their contents, following least privilege. Not totally sure if there's a hidden catch with Al-specific stuff, but everything I've seen points to these two. Anyone come across a scenario where A or D would make sense here?
I don't think it's A. You can't even configure any forensic settings until you've claimed capacity, so B should be first. That "first" word in these risk management setups is a classic trap for folks who just want to jump into config steps like A or D. Anyone else seen this sequence in practice exams?
Option B makes sense to me since you have to claim the forensic evidence capacity before any other config is possible in Purview. Without that, none of the settings for capture even become available. I think D comes later when scoping who gets monitored. Pretty sure but if someone actually tried this in a lab and got a different result, let me know!
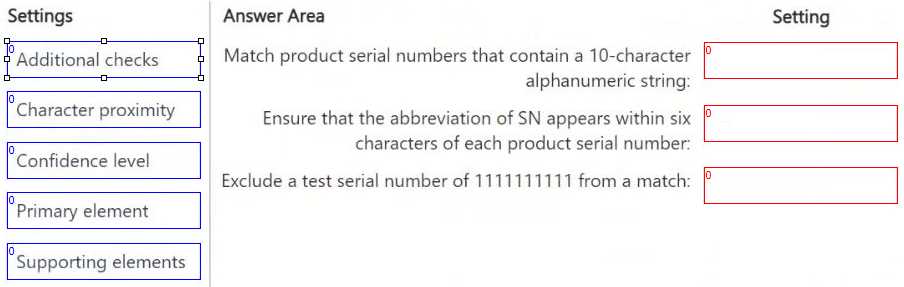
DRAG DROP You have a Microsoft 365 E5 subscription that has data loss prevention (DLP) implemented. You need to create a custom sensitive info type. The solution must meet the following requirements: ● Match product serial numbers that contain a 10-character alphanumeric string. ● Ensure that the abbreviation of SN appears within six characters of each product serial number. ● Exclude a test serial number of 1111111111 from a match. Which pattern settings should you configure for each requirement? To answer, drag the appropriate settings to the correct requirements. Each setting may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
Pretty sure it's B. Set-AuditConfig is just org-wide, doesn't turn on auditing for a single mailbox like User1. You'd need Set-Mailbox -AuditEnabled $true for that user instead. Someone let me know if Microsoft changed this recently.
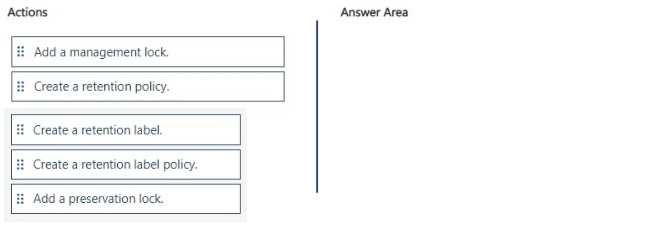
DRAG DROP You have a Microsoft 365 tenant. A new regulatory requirement states that all documents containing a patent ID be labeled, retained for 10 years, and then deleted. The policy used to apply the retention settings must never be disabled or deleted by anyone. You need to implement the regulatory requirement. Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
I thought management lock was the right control here to stop any changes or deletions on the policy. Pretty sure that's closer to Azure admin restrictions but the wording in the requirement about never being disabled made me pick that. If I missed something, let me know.
Option B makes more sense here since passwordless authentication is supported for both interactive and service accounts (like User3), but passkey (D) won't work for non-interactive scenarios. D looks tempting but is a trap for service use. Anyone disagree?
I was thinking D makes sense here since FIDO2 passkeys are super secure for logins. Since all three would be covered for strong auth, seemed solid. Not sure if the service account setup would be tricky with this though, so maybe I'm missing something.
Don't think it's C, since you can use just one custom SIT for all project names. The rest are built-in types like credit card and NHS numbers, so that makes B the best fit in my view. Maybe I'm missing something but I really doubt it's more than five.
I don't think it's C, since grouping all project keywords in one custom SIT is allowed. Built-ins cover credit cards, NHS, addresses, and credentials. So B makes more sense-C is a trap if you miss that detail. Agree?
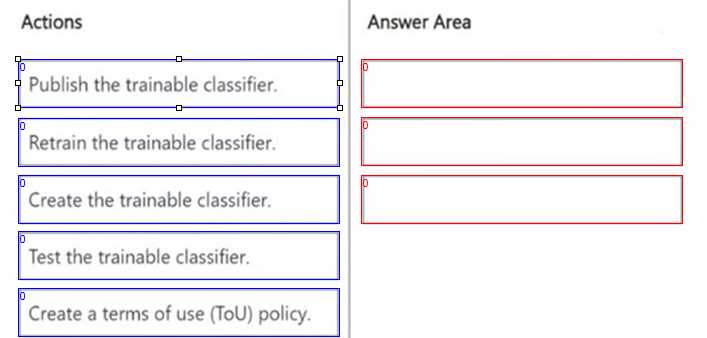
DRAG DROP You need to create a trainable classifier that can be used as a condition in an auto-apply retention label policy. Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
This is the right order because you always have to create it first, test and tweak it so it works well, then publish for use in policies. "Retrain" isn’t a required step unless accuracy isn’t good and ToU doesn’t fit here. Pretty sure on this sequence from similar questions.
Looks right to me: Create the trainable classifier, Test the trainable classifier, Publish the trainable classifier. That's the actual sequence in Purview for using it in auto-apply policies. Retrain only matters if it fails testing first time, pretty sure. Someone correct me if I missed anything.
Create the trainable classifier → Test the trainable classifier → Publish the trainable classifier. That's the typical flow for Microsoft Purview classifiers if you want to use them in retention policies. Retrain only comes up if testing fails, which isn't part of the base requirement here. Confident this is right, but open to corrections if I missed an edge case.
DRAG DROP You have a Microsoft 365 E5 subscription that uses Microsoft Purview insider risk management and contains three users named User1, User2, and User3. All insider risk management policies have adaptive protection enabled and the default conditions for insider risk levels configured. The users perform the following activities, which trigger insider risk policy alerts: User1 performs at least one data exfiltration activity that results in a high severity risk score. User2 performs at least three risky user activities within seven days, that each results in a high severity risk score. User3 performs at least bwo data exfiltration activities within seven days, that each results in a high severity risk score. Which insider risk level is assigned to each user? To answer, drag the appropriate levels to the correct users. Each level may be used once, more than once, or not at all. You may need to drag the split bar between panes or seroll to view content. NOTE: Each correct selection is worth one point.