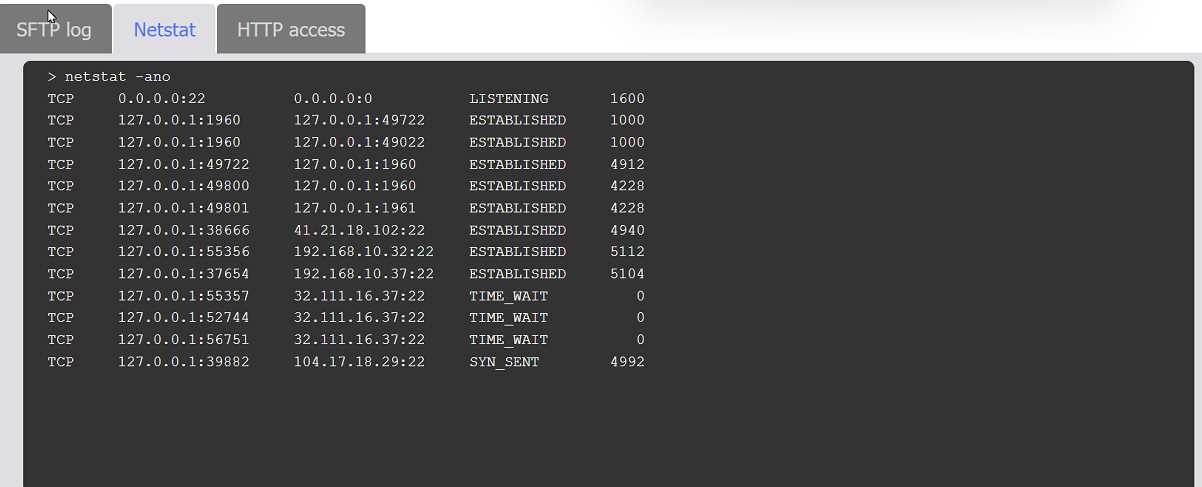
SIMULATION An organization's website was maliciously altered. INSTRUCTIONS Review information in each tab to select the source IP the analyst should be concerned about, the indicator of compromise, and the two appropriate corrective actions. 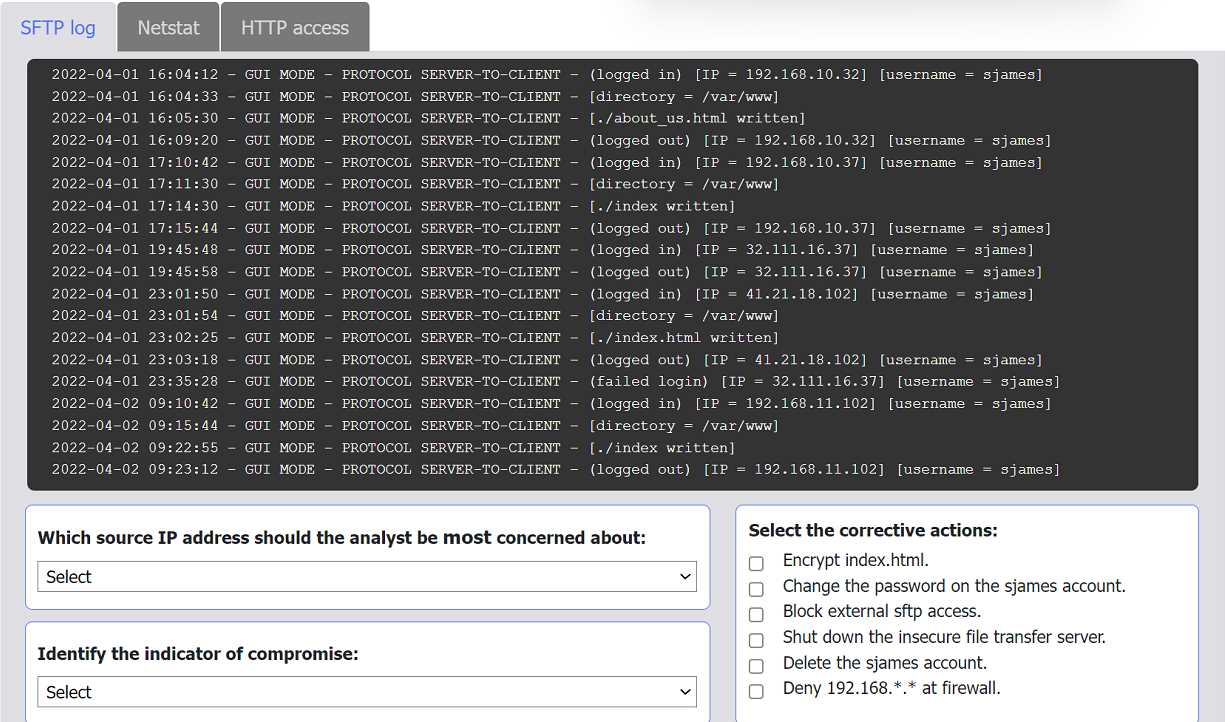
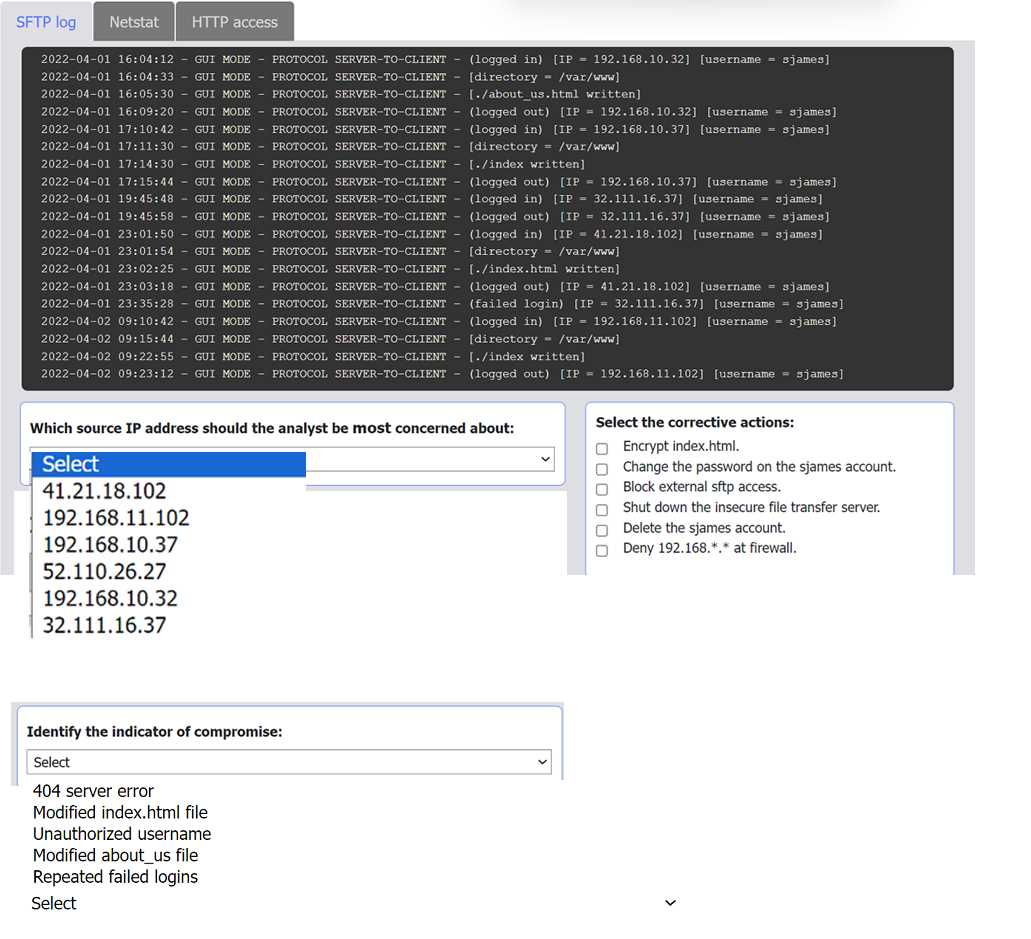

Not quite the internal address. The suspicious activity comes from 41.21.18.102, which logs in as sjames and alters index.html. The two key steps are changing that account's password and deleting it, since internal IPs just reflect normal ops. Seen this logic in other CySA+ practice sets, pretty sure that's right.
Source IP: 10.7.34.82
Indicator: suspicious login times
Actions: disable sjames account, reset web server
I saw a similar question but not totally sure if the internal IP is right here since it connects right before the change. Did anyone else pick these values?

