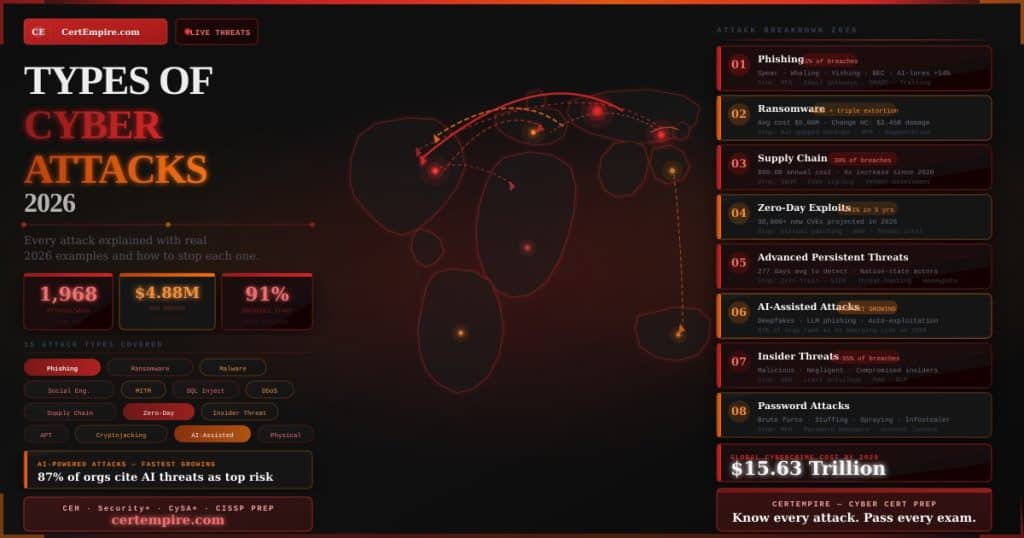
Quick Answer: Weekly volumes of cyber attacks now hit an average of 1,968 attacks per week, an 18 percent year-over-year increase from 2025 and a 70 percent increase since 2023. The average cost of a data breach globally is $4.88 million, a 10 percent increase year-on-year. This guide covers every major type of cyber attack in 2026, how each one works, a real breach example, and the exact controls that stop it. For security professionals preparing to certify their knowledge of these attacks, CertEmpire carries practice exams for every certification that covers offensive and defensive security including CEH, Security+, CySA+, and CISSP.
Why Understanding Attack Types Matters More Than Ever
Over 7.5 million cyber incidents were recorded in 2025, up significantly from the prior year. Ransomware-related attacks drove over half of all global cyberattacks. Phishing still leads as a vector, with 91 percent of successful breaches starting with phishing.
In February 2026, malware led attack techniques at 37 percent, followed by ransomware at 16 percent and account takeovers at 11 percent. Social engineering led initial access vectors at 18 percent, ahead of public-facing application vulnerabilities at 13 percent and supply chain compromises at 12 percent.
According to recent data, the human element is the common root cause of 74 to 95 percent of data breaches. Understanding how each attack type works is not just academic. It is the foundation of every security decision an organization makes, every certification an IT professional earns, and every defense strategy a security team implements.
1. Phishing
How It Works
Phishing is a social engineering attack that uses fraudulent communications, most commonly email, to trick recipients into revealing sensitive information, clicking malicious links, or downloading malware. The attacker impersonates a trusted entity such as a bank, employer, or government agency to create a sense of urgency or legitimacy.
AI-generated phishing lures increase click-through rates by up to 54 percent and eliminate traditional red flags like poor grammar and spelling errors. In 2026, phishing emails generated by large language models are indistinguishable from legitimate corporate communications in most cases.
Phishing Variants
Spear phishing targets a specific individual with personalized content drawn from social media, LinkedIn profiles, or previous data breaches. Whaling targets senior executives specifically. Vishing uses phone calls to impersonate IT support, banks, or government officials. Smishing delivers phishing content via SMS messages. Business email compromise impersonates an executive to authorize fraudulent wire transfers or redirect payroll.
Real 2026 Example
Phishing will be a part of 42 percent of all global breaches in 2026, with AI-generated lures making detection significantly harder for both humans and email filters. Multiple major financial institutions reported in early 2026 that AI-crafted spear phishing campaigns targeting finance department employees achieved initial compromise in organizations that had previously withstood conventional phishing attempts.
How to Stop It
Multi-factor authentication prevents credential theft from succeeding even when phishing captures a password. Email security gateways with AI-powered analysis filter known phishing patterns. Security awareness training that includes simulated phishing campaigns keeps employees calibrated. DMARC, DKIM, and SPF email authentication records prevent domain spoofing. Reporting buttons in email clients that flag suspicious messages create organizational threat intelligence.
Certification coverage: Security+ Domain 2 tests phishing variant identification directly. CEH v13 Module 9 covers social engineering including phishing campaign construction and AI-assisted attacks.
2. Ransomware
How It Works
Ransomware is a type of malware that encrypts a user’s files or locks their computer, demanding a ransom payment for their return. Attackers gain access through phishing emails, malicious downloads, or unpatched vulnerabilities, then use the software to encrypt data and sometimes steal sensitive information before demanding a ransom, typically in cryptocurrency.
Ransomware-as-a-Service is the dominant engine driving the threat landscape in 2026. Major ransomware operators act as software vendors, developing the malware and running fake customer support for victims. They then lease these tools to affiliates who execute the attacks, with operators taking a cut of every successful ransom payment.
The Evolution to Triple Extortion
In 2025, double extortion became common where attackers encrypted systems and stole data. In 2026, many groups skip encryption entirely. Instead of encrypting systems, attackers focus on data theft and immediate extortion, putting organizations under immediate legal, compliance, and reputational pressure even if systems remain operational.
Stolen credentials, vulnerability exploitation, and phishing remain by far the most common initial access vectors for ransomware groups. Ransomware groups made less money in 2025 despite a 47 percent increase in publicly reported attacks, pushing them to adopt new approaches including DDoS-as-a-Service, insider recruitment, and gig worker exploitation.
Real 2026 Example
Kettering Health, a system responsible for 14 medical centers and dozens of clinics, was targeted by the Interlock ransomware group, knocking critical systems offline before exfiltrating sensitive data. Less than a month after the attack, a class-action lawsuit was filed alleging that patients were forced to miss scheduled chemotherapy treatments and others could not access prescriptions due to the disruption.
Change Healthcare represents the standout ransomware episode through 2026. A single portal without MFA helped trigger over $2.45 billion in total damage at Change Healthcare. Cencora reportedly paid about $75 million as attackers exploited flat access and broad internal permissions.
How to Stop It
Practical prevention strategies include robust cybersecurity training, regular patching, multi-factor authentication, and comprehensive backup plans. Network segmentation and continuous monitoring with SIEM tools help detect threats early, while a well-prepared incident response plan ensures quick recovery and minimizes disruption.
Air-gapped backups that cannot be reached by ransomware through the network are the most critical recovery control. The 3-2-1 backup rule specifies three copies of data, on two different media types, with one stored offsite.
Certification coverage: CEH v13 Module 7 covers malware threats including ransomware deployment techniques. CySA+ CS0-003 Domain 2 covers ransomware response and containment procedures.
3. Malware
How It Works
Malware is the umbrella category covering all malicious software. The major subcategories each have distinct behaviors, propagation methods, and purposes.
Viruses attach to legitimate executable files and activate when the host file runs. Unlike worms they require user action to spread. Worms spread across networks autonomously without user interaction, exploiting vulnerabilities in network services. Trojans disguise themselves as legitimate software to trick users into installing them, then execute their malicious payload once inside. Spyware operates silently to collect user data including credentials, keystrokes, and browsing history. Keyloggers specifically record every keystroke to capture passwords and sensitive information. Rootkits modify the operating system itself to hide the presence of other malware and provide persistent privileged access. Fileless malware operates entirely in memory without writing to disk, evading signature-based detection tools that scan for files.
Real 2026 Example
The growing use of AI chatbots and agents in business operations creates a new attack surface for infostealer malware. In 2025, IBM X-Force researchers found more than 300,000 ChatGPT credentials listed for sale on the dark web. As AI agents require access to data to function effectively, organizations face a difficult balancing act enabling productivity while securing credentials stored by AI tools.
How to Stop It
Endpoint detection and response platforms provide behavioral analysis that catches malware not detectable by signatures. Application allowlisting prevents unauthorized executables from running. Regular system patching eliminates the vulnerabilities malware exploits for initial access. Network traffic monitoring identifies command-and-control communications from installed malware. User privilege restriction limits the damage malware can cause even after installation.
Certification coverage: Security+ Domain 2 covers malware classification and identification. CEH v13 Module 7 covers malware construction, evasion, and analysis techniques.
4. Social Engineering
How It Works
Social engineering manipulates human psychology rather than exploiting technical vulnerabilities. Attackers exploit trust, authority, urgency, fear, and reciprocity to convince targets to take actions they would otherwise refuse.
Pretexting creates a fabricated scenario to justify a request for information or access. An attacker might impersonate a new IT contractor, a vendor representative, or an auditor to gain access or information. Baiting places infected physical media such as USB drives in locations where curious individuals might pick them up. Tailgating physically follows an authorized person through a secure entrance without using credentials. Quid pro quo offers something of value in exchange for information or access, such as pretending to provide IT support in exchange for login credentials.
The human element is the common root cause of 74 to 95 percent of all data breaches. Social engineering targets that human element directly, bypassing technical controls entirely.
Real 2026 Example
A ransomware group attempted to recruit a reporter at the BBC in a notable example of insider recruitment via social engineering. Private reporting indicates that insider recruitment attempts increased significantly throughout 2025 and will likely continue growing, especially if workforce reductions at major companies persist into 2026. A gig worker was found to be unknowingly working for hackers, believing they were performing a legitimate IT task.
How to Stop It
Security awareness training that covers all social engineering variants is the primary control because the human is the attack surface. Strict verification procedures for any request involving credentials, access, or sensitive information prevent social engineering from succeeding even when attackers are convincing. Physical security controls including visitor management, badge verification, and mantrap entries prevent tailgating. Reporting culture that rewards employees for flagging suspicious requests creates organizational resilience.
Certification coverage: CEH v13 Module 9 covers the full social engineering toolkit including AI-assisted deepfake attacks. Security+ Domain 2 tests identification of social engineering variants from scenarios.
5. Man-in-the-Middle Attacks
How It Works
A man-in-the-middle attack intercepts communications between two parties without their knowledge, allowing the attacker to eavesdrop on, capture, or modify data in transit.
ARP spoofing poisons the ARP cache of devices on a local network to redirect traffic through the attacker’s system. DNS spoofing corrupts DNS cache entries to redirect legitimate domain requests to malicious IP addresses. SSL stripping downgrades an HTTPS connection to HTTP, removing encryption and exposing data in plaintext. SSL interception with certificate spoofing presents a forged certificate to the victim while maintaining a legitimate connection to the actual server. Evil twin attacks create rogue wireless access points with the same SSID as a legitimate network to capture traffic from devices that connect automatically.
Real 2026 Example
Recent incidents involving platforms such as Salesloft and Drift showed attackers leveraging compromised OAuth tokens to access Salesforce environments, illustrating how a compromise of a trusted third party can enable indirect access to customer environments through MITM-style token interception in ways organizations had not fully prepared for.
How to Stop It
TLS encryption with certificate pinning prevents certificate spoofing. HTTP Strict Transport Security headers prevent SSL stripping by forcing browsers to use HTTPS. VPN connections encrypt traffic on untrusted networks, preventing traffic interception on public Wi-Fi. DNSSEC authenticates DNS responses, preventing DNS spoofing. 802.1X port-based network access control prevents unauthorized devices from connecting to network segments.
Certification coverage: Security+ Domain 3 covers secure protocols and network design. CEH v13 Module 8 covers sniffing and MITM attack techniques.
6. SQL Injection
How It Works
SQL injection inserts malicious SQL commands into input fields that are passed directly to a database without sanitization. When a web application constructs database queries by concatenating user input with SQL syntax, an attacker can modify the query logic to extract unauthorized data, modify records, delete tables, or in some configurations execute operating system commands.
A basic SQL injection might enter ‘ OR ‘1’=’1 into a login field to bypass authentication by making the query always return true. More sophisticated attacks use blind injection to extract data character by character, union-based injection to retrieve data from other tables, or time-based injection to infer information from database response timing.
Vulnerability exploitation was the initial access method in 20 percent of breaches based on analysis of confirmed incidents. Unpatched vulnerabilities continue to be the biggest driver of breaches, with 54 percent of ransomware incidents traced back to outdated or poorly patched systems. SQL injection vulnerabilities often persist in systems for years without being addressed.
Real 2026 Example
In Q1 2026 alone, there were 486 data breach events across transportation, retail, government, and education sectors. Many of these involved web application vulnerabilities including injection flaws, with exposed databases containing personal information including names, email addresses, phone numbers, passwords, bank accounts, and insurance documents.
How to Stop It
Parameterized queries and prepared statements are the primary defense, separating SQL syntax from user input so the database never interprets user-supplied data as part of the query structure. Input validation rejects inputs that contain SQL syntax. Web application firewalls detect and block common injection patterns. Least-privilege database accounts limit the damage possible if injection occurs. Regular application security testing including automated scanning and penetration testing identifies injection vulnerabilities before attackers do.
Certification coverage: CEH v13 Module 15 provides dedicated deep coverage of SQL injection. Security+ Domain 2 covers application vulnerabilities including injection attacks. CISSP Domain 8 covers secure coding practices and SDLC security controls.
7. Denial of Service and Distributed Denial of Service
How It Works
Denial of service attacks overwhelm a target system with traffic or requests until it becomes unavailable to legitimate users. Distributed denial of service attacks coordinate thousands or millions of compromised machines in a botnet to amplify the attack volume beyond what any single source could generate.
Volumetric attacks saturate bandwidth with high volumes of traffic. Protocol attacks exploit weaknesses in network protocol implementation such as SYN floods that exhaust connection state tables. Application layer attacks target specific application functions, sending requests that consume excessive server resources to process. Amplification attacks use misconfigured services such as DNS resolvers or NTP servers to reflect and amplify small requests into large responses directed at the target.
The finance and telecommunications industries account for approximately 60 percent of all DDoS targeted attacks.
Real 2026 Example
Officials confirmed that the Milano Cortina Winter Olympic Games faced attempted cyberattacks including DDoS campaigns targeting venues, hotels, and digital systems. Italian authorities and cybersecurity experts raced to maintain availability of critical infrastructure during the high-profile international event.
Ransomware groups are now offering bundled DDoS services to affiliates. The newly formed Chaos ransomware group provides DDoS capabilities to all affiliates as a differentiator, creating triple-threat scenarios where organizations simultaneously face encryption, data theft, and availability attacks.
How to Stop It
DDoS mitigation services from specialized providers such as Cloudflare and Akamai absorb volumetric attacks before they reach organizational infrastructure. Network-level rate limiting restricts the number of requests any single source can make in a given period. Anycast network distribution spreads traffic across multiple geographic points of presence, preventing any single location from being overwhelmed. Traffic scrubbing services analyze incoming traffic and filter malicious packets while passing legitimate requests.
Certification coverage: CEH v13 Module 10 covers DoS and DDoS attack types and execution techniques. Security+ Domain 2 covers DoS attacks and countermeasures.
8. Supply Chain Attacks
How It Works
Supply chain attacks compromise software, hardware, or services before they reach the end target, exploiting the trust organizations place in their vendors, suppliers, and third-party integrations. Rather than attacking a well-defended organization directly, attackers target a less-defended supplier with access to the ultimate target.
Over the past five years, major supply chain and third-party breaches increased sharply, with incidents quadrupling according to IBM X-Force findings. This reflects a shift in attacker behavior: rather than breaking through a single organization’s defenses, adversaries increasingly target interconnected systems and trusted integrations such as vendors, open-source dependencies, identity integrations, CI/CD workflows, and cloud interfaces.
Software supply chain attacks specifically inject malicious code into legitimate software before distribution. Attackers may compromise a software vendor’s build system, insert malicious packages into open-source repositories, or hijack developer credentials to push malicious updates through legitimate channels.
Real 2026 Example
In July 2025, the ransomware group SafePay infiltrated Ingram Micro, a global technology distributor, disrupting operations for nearly a week. The attack paralyzed the supply chain for thousands of value-added resellers and MSPs, preventing them from procuring licenses or hardware for their clients. SafePay leveraged custom dynamic link libraries and sophisticated techniques to evade detection, proving that even industry giants are vulnerable to supply chain compromise.
Cyberattacks targeting the software supply chain are expected to cost the global economy $80.6 billion annually by 2026. In 2025, 30 percent of breaches involved third-party vendors, twice the rate reported the previous year.
How to Stop It
Third-party risk management requires evaluating the cybersecurity practices of external vendors to reduce vulnerability within the provider’s controlled infrastructure. Software bill of materials documentation tracks every software component and its origin. Code signing verifies that software has not been modified since it was signed by a trusted developer. Vendor security assessments evaluate supplier security posture before granting access. Zero trust architecture limits the blast radius of a supply chain compromise by refusing to trust any vendor connection by default.
Certification coverage: CISSP Domain 1 covers third-party risk management and supply chain security governance. CEH v13 Module 19 covers cloud and supply chain attack techniques.
9. Zero-Day Exploits
How It Works
A zero-day exploit targets a vulnerability that is unknown to the software vendor and for which no patch exists. The term zero-day refers to the zero days the defender has had to fix the flaw. Once a zero-day is discovered by an attacker and used in the wild, the clock starts for vendors to develop and release a patch, but during the window between discovery and patching every system running the vulnerable software is exposed.
Zero-day exploits have jumped 141 percent in the last five years. While zero-day attacks were once reserved for large nation-states with expansive resources, the rising profitability of ransomware means that even small extortion gangs can now acquire and deploy zero-day exploits purchased from underground markets.
The CVE database holds over 305,000 recorded vulnerabilities, with projections of over 30,000 new disclosures in 2026 alone.
Real 2026 Example
CVE-2025-40551, a critical flaw in SolarWinds Web Help Desk with a CVSS score of 9.8, was actively exploited before a patch was widely applied. Critical and high-severity vulnerabilities frequently remain unpatched for extended periods, with 33 percent remaining unpatched for over 180 days.
How to Stop It
Virtual patching through web application firewalls and intrusion prevention systems creates a protective layer around vulnerable systems before official patches are available. Attack surface reduction minimizes the number of externally exposed systems and services that could be targeted. Threat intelligence feeds provide early warning of zero-day activity in the wild. Endpoint detection and response with behavioral analysis can identify exploitation attempts even when the specific vulnerability is unknown. Rapid patch deployment processes reduce the window between patch availability and deployment.
Certification coverage: CEH v13 covers zero-day research methodology and exploit development concepts. CySA+ CS0-003 covers vulnerability management and prioritization of unpatched systems.
10. Insider Threats
How It Works
Insider threats originate from individuals who have authorized access to organizational systems and use that access to cause harm, either deliberately or inadvertently. The authorization that makes insiders productive is the same attribute that makes them dangerous.
Malicious insiders intentionally steal data, sabotage systems, or sell access to external attackers. Negligent insiders cause breaches through careless actions such as misconfiguring cloud storage, falling for phishing, or storing sensitive data on personal devices. Compromised insiders are legitimate users whose credentials have been stolen by external attackers who then act as a trusted insider.
Ransomware operators are increasingly turning to native English speakers to recruit corporate insiders. Insider recruitment attempts increased significantly throughout 2025 and will likely continue growing, especially if workforce reductions at major companies persist into 2026.
Real 2026 Example
South Korea attributed e-commerce retailer Coupang’s data breach to management failures rather than a sophisticated external attack. A former engineer familiar with flaws in the authentication process broke into the system in April, with the breach lasting until November. They attempted to gain access again in January. The attacker exploited user authentication vulnerabilities to access user accounts without a proper login, causing large-scale unauthorized information leaks.
How to Stop It
User behavior analytics establishes baselines for normal user activity and alerts on deviations such as unusual data downloads or access at atypical hours. Principle of least privilege ensures users have only the access their current role requires, limiting the damage any single insider can cause. Privileged access management controls and monitors the highest-risk accounts with additional authentication and session recording. Data loss prevention tools detect and block unauthorized data exfiltration. Background checks and security clearance processes reduce the risk of deliberately malicious insiders gaining positions of trust.
Certification coverage: CISSP Domain 7 covers insider threat indicators and security operations response. Security+ Domain 5 covers governance controls for insider threat prevention.
11. Advanced Persistent Threats
How It Works
Advanced persistent threats are sophisticated, long-duration attacks conducted by well-resourced threat actors including nation-states, state-sponsored groups, and organized criminal enterprises. APT attacks prioritize stealth and persistence over speed, often remaining inside a target environment for months or years before executing their primary objective.
Security teams take an average of 277 days to identify and contain a data breach, while breaches involving lost or stolen credentials take 328 days to identify and contain. APT actors exploit this detection gap by moving slowly and deliberately to avoid triggering security alerts.
The APT lifecycle follows a consistent pattern. Initial access is typically gained through spear phishing, zero-day exploitation, or supply chain compromise. Attackers then establish persistence mechanisms, conduct internal reconnaissance, move laterally to high-value targets, escalate privileges, and ultimately exfiltrate data or execute their mission over an extended period.
Real 2026 Example
IBM X-Force’s 2026 Threat Intelligence Index identified supply chain APT campaigns where adversaries maintained persistent access to interconnected systems for extended periods, targeting CI/CD workflows and cloud interfaces to position for long-term intelligence collection rather than immediate financial gain.
How to Stop It
Network segmentation with zero trust principles limits lateral movement by requiring authentication for every internal access attempt. Security information and event management platforms correlate logs across the environment to detect the low-and-slow patterns characteristic of APT activity. Threat hunting proactively searches for indicators of compromise rather than waiting for automated alerts. Deception technologies including honeypots and honeytokens detect APT reconnaissance activity before attackers reach production systems.
Certification coverage: CISSP Domain 7 covers APT incident response. CEH v13 covers APT techniques across multiple modules. CySA+ CS0-003 Domain 1 covers threat intelligence and APT actor profiling.
12. Cryptojacking
How It Works
Cryptojacking installs cryptocurrency mining software on victim systems without their knowledge or consent, using the victim’s computing resources and electricity to generate cryptocurrency for the attacker. Unlike ransomware, cryptojacking is designed to operate silently for as long as possible without disrupting the victim’s operations enough to trigger investigation.
Browser-based cryptojacking executes mining scripts through compromised websites without installing any software, running as long as the victim has the malicious page open. File-based cryptojacking installs persistent mining software that runs in the background. Cloud cryptojacking compromises cloud infrastructure to spin up mining instances at the victim’s expense, resulting in massive unexpected cloud bills.
How to Stop It
Browser extensions that block known cryptocurrency mining scripts provide immediate protection for end users. Endpoint detection and response with behavioral analysis identifies the high CPU utilization patterns that indicate mining activity. Cloud resource monitoring and alerting on unusual instance creation or cost spikes catches cloud cryptojacking quickly. Network traffic analysis identifies communications with known mining pool addresses.
Certification coverage: CEH v13 Module 7 covers malware types including cryptominers. Security+ Domain 2 covers malware classification and detection.
13. AI-Assisted Attacks
How It Works
AI-driven attacks are the fastest-growing risk in cybersecurity with 87 percent of organizations ranking AI-related vulnerabilities as the fastest-growing cyber risk.
AI is transforming every phase of the attack lifecycle. In reconnaissance, AI tools automate the collection and correlation of open-source intelligence across social media, public records, and corporate websites. In phishing, large language models generate convincing, personalized luring content at scale without the grammatical errors that historically identified phishing. In exploitation, AI-powered vulnerability scanning identifies attack paths faster than human researchers. In social engineering, deepfake audio and video impersonate executives and trusted contacts convincingly enough to authorize fraudulent transactions.
AI-generated phishing lures increase click-through rates by up to 54 percent. They eliminate red flags like poor grammar and spelling errors easily.
Research suggests companies adopting generative AI to support hyper-personalized training could result in 40 percent fewer employee-caused security incidents by 2026. AI defends as well as attacks. The question for every organization is whether their defensive AI keeps pace with offensive AI deployment.
Real 2026 Example
Accelerating AI adoption, geopolitical fragmentation, and widening cyber inequity are reshaping the global risk landscape according to the World Economic Forum’s 2026 Global Cybersecurity Outlook. While the percentage of respondents assessing the security of AI tools ahead of deployment has nearly doubled over the past year from 37 to 64 percent, 87 percent of leaders still see AI-related vulnerabilities as the fastest-growing cyber risk.
How to Stop It
AI-powered security tools including next-generation endpoint protection, email security, and SIEM platforms match the automation capability of AI-assisted attackers. Security awareness training that specifically covers AI-generated phishing and deepfake scenarios teaches employees to verify through out-of-band channels before acting on any unusual request regardless of how legitimate it appears. Multi-factor authentication ensures that AI-crafted phishing campaigns cannot succeed with credentials alone.
Certification coverage: CEH v13 is the world’s first AI-integrated ethical hacking certification, covering AI-assisted attack techniques across all five phases. This is covered explicitly in CEH v13 Module 9 for social engineering and throughout the reconnaissance and exploitation modules.
14. Password Attacks
How It Works
Password attacks attempt to gain unauthorized access by compromising authentication credentials through various methods.
Brute force attacks systematically try every possible combination of characters until the correct password is found. Dictionary attacks try a predefined list of common passwords, dictionary words, and known password patterns. Credential stuffing uses username and password combinations from previous data breaches against other services, exploiting the widespread practice of password reuse. Password spraying tries a small number of commonly used passwords against a large number of accounts to avoid account lockout thresholds. Rainbow table attacks use precomputed hash tables to reverse password hashes quickly. Pass-the-hash attacks capture and reuse the password hash directly without needing to crack it.
Infostealer malware such as RedLine sucks up saved passwords from browser caches on personal devices, which are then sold on the dark web. Attackers simply log in to VPN or Microsoft 365 accounts using purchased credentials without needing to crack anything.
How to Stop It
Multi-factor authentication makes stolen passwords insufficient for access. Password managers enable users to maintain unique, complex passwords for every account without memorizing them. Account lockout policies limit brute force attempts. NIST SP 800-63B guidelines recommend checking new passwords against known breach databases rather than requiring arbitrary complexity rules that users circumvent by creating predictable patterns. Salted password hashing makes rainbow table attacks ineffective.
Certification coverage: CEH v13 Module 6 covers all password attack techniques. Security+ Domain 4 covers authentication best practices and IAM controls.
15. Physical Attacks
How It Works
Physical attacks target information systems through direct physical access rather than network-based intrusion. Organizations that invest heavily in logical security often leave physical attack vectors unaddressed.
Dumpster diving recovers sensitive documents, printed reports, or discarded storage media from waste containers. Shoulder surfing observes victims entering credentials or viewing sensitive information in public places. Evil maid attacks involve physical access to an unattended device to install hardware keyloggers or boot-level rootkits. USB drop attacks leave infected drives in parking lots, lobbies, or common areas for curious individuals to plug in. Tailgating physically follows an authorized person through secured entry points without authenticating.
How to Stop It
Clean desk policies ensure sensitive information is not left visible or accessible. Document shredding policies prevent dumpster diving from yielding usable information. Screen privacy filters prevent shoulder surfing in public spaces. Physical device security including cable locks, laptop encryption with pre-boot authentication, and BIOS passwords protect against evil maid attacks. Security awareness training covers physical attack scenarios including USB drop attacks specifically.
Certification coverage: CISSP Domain 3 covers physical security design and controls. CEH v13 and the DoD Cyber Awareness Challenge both cover physical attack scenarios.
The 2026 Threat Landscape: What Changed This Year
In February 2026, supply chain compromises accounted for 12 percent of initial access vectors, equal to public-facing application vulnerabilities and behind only social engineering at 18 percent.
Where 2025 still featured a handful of recognizable ransomware brands, 2026 is defined by fragmentation. New strains appear frequently, affiliates shift platforms quickly, and attribution has become harder for defenders and law enforcement alike. One of the most important changes in 2026 is the growing use of data-only extortion. Instead of encrypting systems, attackers focus exclusively on data theft and immediate extortion pressure.
Cybercrime is evolving at a staggering pace. Much like legitimate tech enterprises, cybercriminals are adopting scalable business models, offering cybercrime-as-a-service platforms that make it easier for less experienced actors to launch cyberattacks. This democratization of cybercrime is driving exponential growth in the threat landscape.
How Certifications Map to Cyber Attack Knowledge
Understanding cyber attacks conceptually is the foundation. Proving that knowledge with a certification is what turns understanding into career advancement.
CompTIA Security+ covers attack identification and mitigation across all categories tested in Domain 2 (Threats, Vulnerabilities, and Mitigations at 22 percent) and Domain 4 (Security Operations at 28 percent). It is the baseline credential for every cybersecurity role.
CEH v13 goes deeper into every offensive technique covered in this guide, teaching professionals to replicate attacks in authorized environments to find vulnerabilities before malicious actors do. CEH v13’s AI integration makes it the only certification that explicitly covers AI-assisted attack techniques as part of its core curriculum.
CySA+ focuses on detecting and responding to the attacks described in this guide from the blue team perspective, covering threat intelligence, vulnerability management, incident response, and security monitoring.
CISSP covers the governance and management dimensions of cyber attack prevention and response, including risk management frameworks, security architecture, and incident response at the senior leadership level.
For practice exams across every certification that maps to cyber attack knowledge, CertEmpire provides updated question banks with complete answer explanations built around the current exam blueprints for Security+, CEH, CySA+, CISSP, and every other certification in the cybersecurity track.
Frequently Asked Questions
What is the most common type of cyber attack in 2026?
Malware leads attack techniques at 37 percent of incidents, followed by ransomware at 16 percent and account takeovers at 11 percent. Social engineering leads initial access vectors at 18 percent. Phishing remains the entry point for the majority of all attack types.
How much does a cyber attack cost on average?
The average cost of a data breach globally is $4.88 million, a 10 percent increase year-on-year. Ransomware attacks cost organizations an average of $5.08 million, over $600,000 more than a typical data breach.
What is the fastest-growing type of cyber attack?
AI-driven attacks are the fastest-growing risk, with 87 percent of organizations ranking AI-related vulnerabilities as the fastest-growing cyber risk. AI-generated phishing lures increase click-through rates by up to 54 percent.
How often do cyber attacks happen?
Weekly volumes of cyber attacks now hit an average of 1,968 per week. Cybercrime is set to cost businesses as high as $15.63 trillion by 2029.
Which industries are most targeted?
Healthcare organizations are particularly vulnerable and targeted because they possess information of high monetary and intelligence value. Government data breaches have nearly tripled since 2020. Finance and telecommunications account for approximately 60 percent of all DDoS targeted attacks.
What certification teaches the most about cyber attacks?
CEH v13 provides the most comprehensive offensive security curriculum, covering all five phases of ethical hacking across 20 modules with 221 hands-on labs. Security+ provides the best breadth-to-effort ratio for professionals entering the field. CISSP provides the deepest governance and management-level coverage. CertEmpire carries practice exams for all three.