NSE5_EDR-5.0.pdf
Q: 1
Refer to the exhibit.
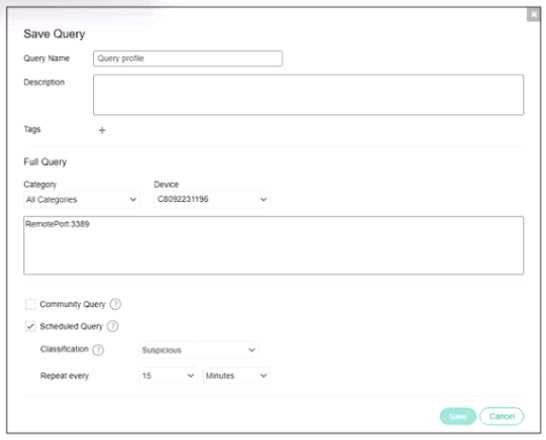 Based on the threat hunting query shown in the exhibit which of the following is true?
Based on the threat hunting query shown in the exhibit which of the following is true?
 Based on the threat hunting query shown in the exhibit which of the following is true?
Based on the threat hunting query shown in the exhibit which of the following is true?Options
Q: 2
A FortiEDR security event is causing a performance issue with a third-parry application. What must
you do first about the event?
Options
Q: 3
A company requires a global communication policy for a FortiEDR multi-tenant environment.
How can the administrator achieve this?
Options
Q: 4
Refer to the exhibit.
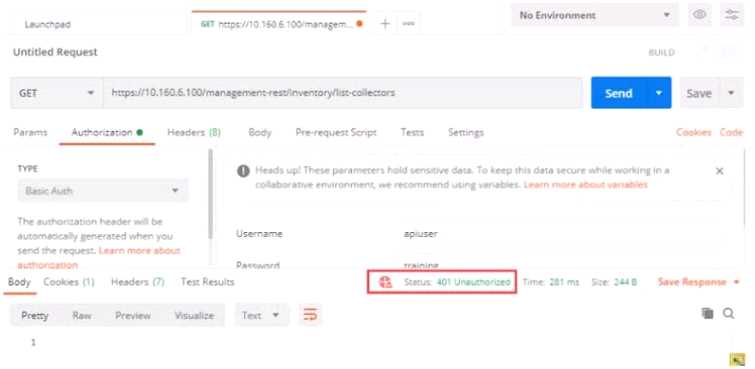 Based on the postman output shown in the exhibit why is the user getting an unauthorized error?
Based on the postman output shown in the exhibit why is the user getting an unauthorized error?
 Based on the postman output shown in the exhibit why is the user getting an unauthorized error?
Based on the postman output shown in the exhibit why is the user getting an unauthorized error?Options
Q: 5
Exhibit.
 Based on the forensics data shown in the exhibit, which two statements are true? (Choose two.)
Based on the forensics data shown in the exhibit, which two statements are true? (Choose two.)
 Based on the forensics data shown in the exhibit, which two statements are true? (Choose two.)
Based on the forensics data shown in the exhibit, which two statements are true? (Choose two.)Options
Q: 6
Refer to the exhibits.
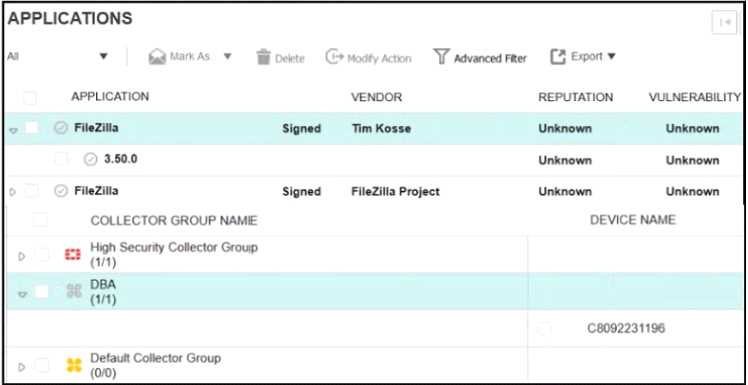
 The exhibits show application policy logs and application details Collector C8092231196 is a member
of the Finance group
What must an administrator do to block the FileZilia application?
The exhibits show application policy logs and application details Collector C8092231196 is a member
of the Finance group
What must an administrator do to block the FileZilia application?
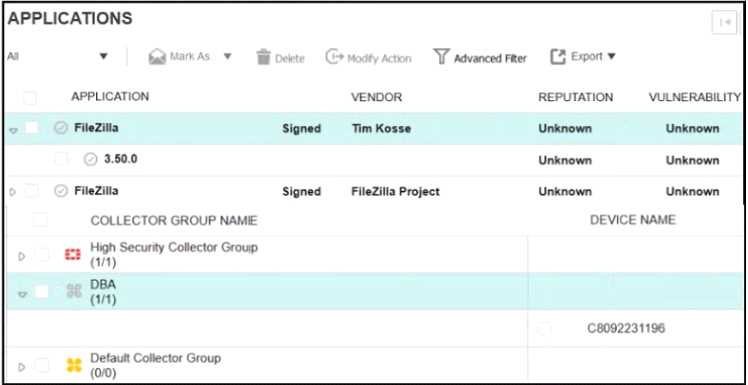
 The exhibits show application policy logs and application details Collector C8092231196 is a member
of the Finance group
What must an administrator do to block the FileZilia application?
The exhibits show application policy logs and application details Collector C8092231196 is a member
of the Finance group
What must an administrator do to block the FileZilia application?Options
Q: 7
What is the purpose of the Threat Hunting feature?
Options
Q: 8
What is the role of a collector in the communication control policy?
Options
Q: 9
An administrator finds a third party free software on a user's computer mat does not appear in me
application list in the communication control console
Which two statements are true about this situation? (Choose two)
Options
Q: 10
FortiXDR relies on which feature as part of its automated extended response?
Options
Question 1 of 10

