

Pretty sure it's D. That rule would cover the parent process and exact command, so you wouldn't see this alert for that specific case again. I saw a similar question in old practice sets and D was close to what they wanted, but maybe I'm missing something about category-wide suppression? Disagree?
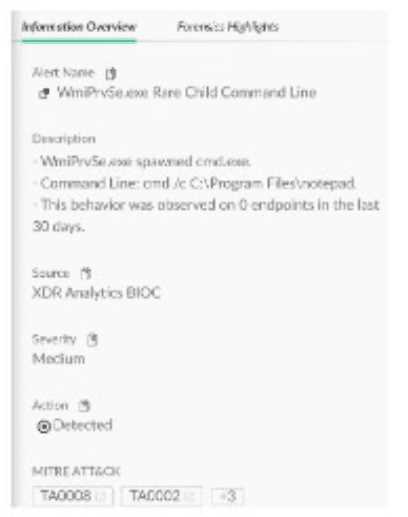
B makes sense here. The question wants to allow all similar lateral movement alerts in the future, not just for one process or command. Creating an alert exclusion rule by source and name covers that category across the board, which matches how XDR handles alert silencing at scale. I think that’s what Palo Alto expects but wouldn’t mind seeing confirmation from the official guide or lab materials if anyone has them.
Just to clarify, are people maybe confusing the trim set here? If you specify only "a" as the trim char in L_TRIM, it won’t remove the space or special chars, just any leading 'a's. So the result wouldn’t be B or C, unless they change the trim set to include more chars.
I don't think it's C. A is the best pick here since with default profiles, Host Inventory -> Mounts will show removable device mount events. C is a trap because extra config isn't needed for this data (unless defaults were changed). Disagree?
Option D makes sense for dynamic endpoint groups in Cortex XDR since they're defined by fields like OS or segment, auto-populating as endpoints match those criteria. B would apply if the question was about static groups, but "dynamic" is the key here. I think some folks mix this up since other EDRs blur the lines. Agree?
Looks like it's pulling the latest activity for connected endpoints in general, not just firewalls since there's no endpoint_type filter. A is correct from what I've seen in official guides and practice sets. If anyone's found a resource pointing to C though, let me know.
In official docs and most practice tests for XDR, configuration retention is usually set to the default (90 days), but I've seen some guides reference 7 days too. Anyone confirm from the latest admin guide?
I don't think D is right here since config data isn't wiped instantly. C makes sense because the uninstallation waits for the next heartbeat and keeps config for 90 days, that's in line with what I’ve seen in exam reports.
My vote is it’s A and C. Setting up P2P downloads (A) means agents can pull updates from each other instead of all hitting the cloud, which really cuts bandwidth. C lets you actually limit how much bandwidth gets used for content updates. Unless your network is really segmented, D isn’t as useful here. If anyone’s implemented D in a straightforward setup and saw benefit, let me know!
I was thinking C and D since Broker VM (D) acts as local relay, so less cloud traffic. C is obvious for direct bandwidth management. Not totally sure though, maybe A helps more internally? Open to better logic here.
I don't think it's B or D here. The collector applet setup just asks for a valid SQL query that pulls the activity you want, not access to logs. Option A matches what I've seen in similar practice material. Happy if someone sees it differently but pretty sure A's correct since the others are more for audit/forensic cases.
Setup needs a valid SQL query so the Database Collector knows what data to ingest, so A fits best. Accessing logs (B or D) is more for continuous monitoring, but for initial setup the query is critical. Seen similar in exam prep materials too. I think A is right but always possible there’s some corner case I missed-anyone seen otherwise?

