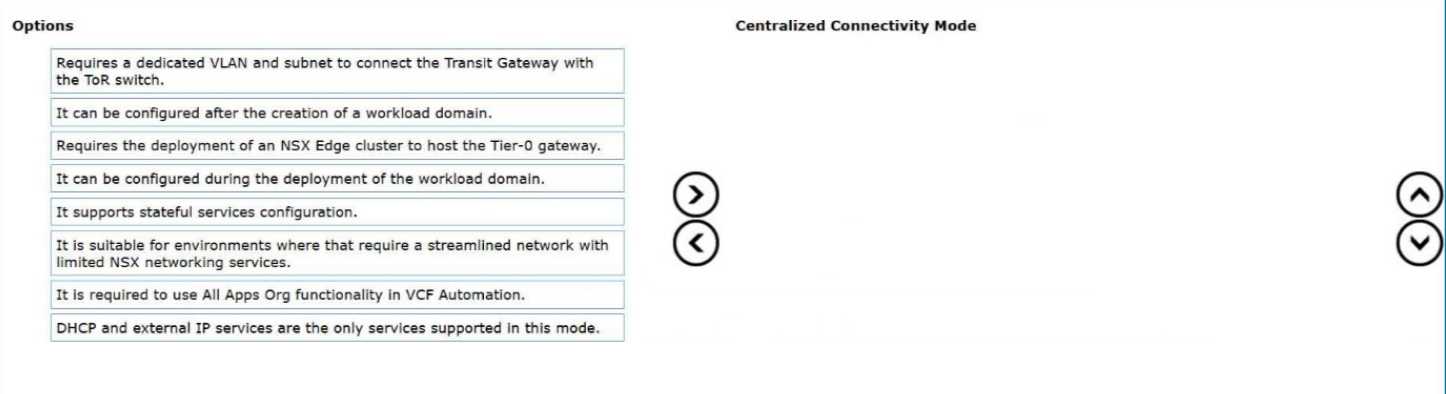
Requires the deployment of an NSX Edge cluster to host the Tier-0 gateway.
It can be configured during the deployment of the workload domain.
It supports stateful services configuration.
It is suitable for environments that require a streamlined network with limited NSX networking
services.
In VMware Cloud Foundation (VCF) 9.0, the networking architecture introduces specialized
connectivity modes to cater to different organizational needs, with Centralized Connectivity Mode
being a primary option for streamlined deployments. This mode is fundamentally anchored to the
physical infrastructure via localized resources rather than distributed components across the entire
cluster.
The most critical technical requirement for this mode is that it requires the deployment of an NSX
Edge cluster to host the Tier-0 gateway. Unlike distributed models, centralized connectivity funnels
North-South traffic through specific Edge nodes that serve as the demarcation point between the
virtual overlay and the physical Top-of-Rack (ToR) switches. This centralization is what enables the
next key characteristic: it supports stateful services configuration. Because traffic is anchored to
specific Service Routers (SR) on Edge nodes, stateful operations such as NAT, Load Balancing, and
stateful firewalls can maintain session persistence, which is not natively possible in a purely
distributed Active/Active ECMP environment without specialized configuration.
From a lifecycle perspective, this mode is highly integrated into the SDDC Manager workflows and
can be configured during the deployment of the workload domain. This allows architects to define
the networking posture of a new domain at "Day 0," ensuring that the necessary Edge resources and
Tier-0/Tier-1 hierarchies are provisioned automatically to meet the domain's specific requirements.
Finally, Centralized Connectivity Mode is suitable for environments that require a streamlined
network with limited NSX networking services. It provides a "cloud-lite" approach to networking,
offering the necessary isolation and security of NSX without the complexity of managing a full-scale
distributed fabric. This makes it an ideal choice for smaller workload domains, specialized labs, or
legacy application environments that do not require the massive scale of a distributed transit
gateway but still need robust stateful security and simplified North-South egress.