Your network contains an on-premises Active Directory domain that syncs to an Azure Active Directory (Azure AD) tenant. The tenant contains the users shown in the following table. 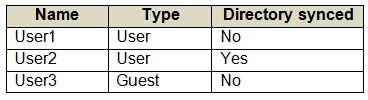
You have an Azure AD tenant named contoso.com that contains the resources shown in the following table. You create a user named Admin 1. 
I see where you're coming from, JasonR. I'd probably pick C too since the Conditional Access policy can block enabling Security defaults. Deleting CAPolicy1 looks like it would remove that blocker. Not totally sure because Admin1 still needs the right permissions, but the question said "first" so C feels closer to what they want. More input?
Wouldn't B be a trap here since hardware tokens need admin setup, not available at first login?
A and E are correct here. FIDO2 security keys and Microsoft Authenticator app are the two supported methods during initial combined registration. D (Windows Hello) needs device enrollment first, so it's a common trap. Pretty sure on this based on recent exam updates, but open to correction if Azure changed something.
Did anyone try checking audit logs (C) for these access errors, or is everyone relying just on sign-in logs? Sometimes I see people mix up where access failure events actually show up. Wondering if there's any reason to use Log Analytics here instead?
You have a Microsoft 365 tenant. You have 100 IT administrators who are organized into 10 departments. You create the access review shown in the exhibit. (Click theExhibittab.) 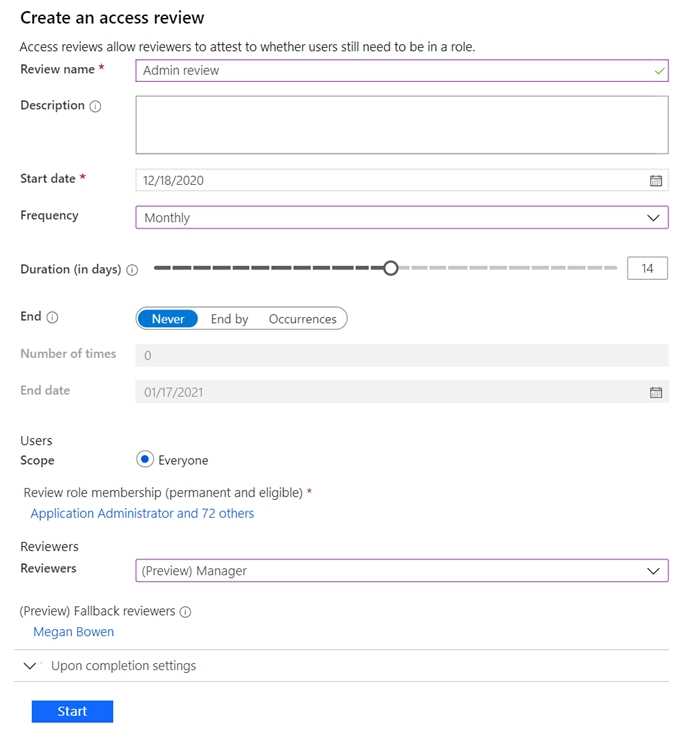
A or A/B? I'm a bit unsure because if the reviewer type is set to "Managers of users" then updating the Manager property on each user should work (so A). But if that's not configured, changing the user properties wouldn't matter. From the context though, looks like A is what they're going for. Anyone see a catch?
My pick: it's A because Azure AD pulls the manager info straight from the Manager property on each user. If you update those attributes, the access reviews will go to the right department heads. Correct me if I'm missing something in the scenario.
C seems like the way to go, since a Defender for Cloud Apps access policy could let you target Facebook traffic directly and see those users. I thought that would be the fastest route. Not super confident though, maybe I'm missing some shortcut in A?

