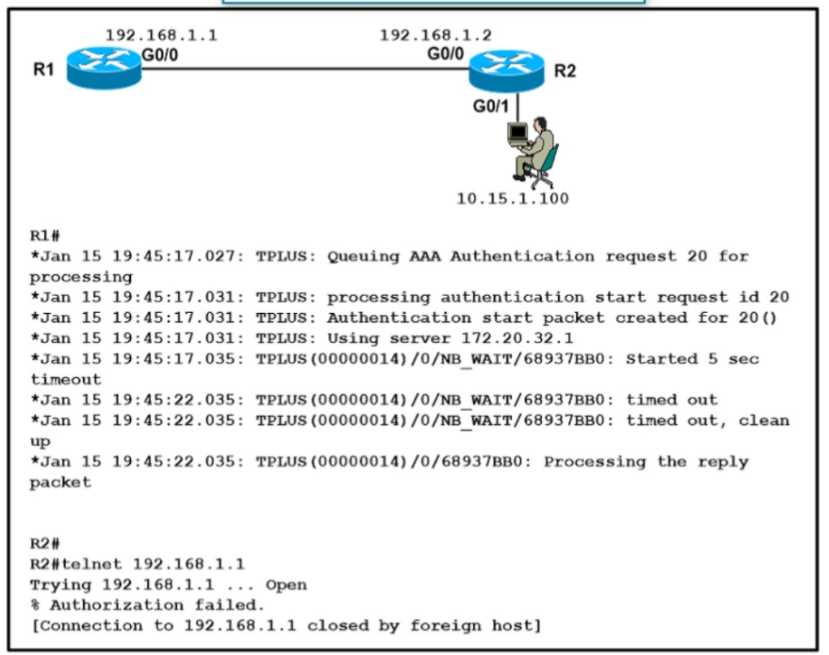
 Refer to the exhibit A network engineer is troubleshooting an AAA authentication issue for R1 from
R2 When an engineer tries to open a telnet connection to R1 it opens the connection but shows a
%Authorization failed error message on the terminal and closes the connection silently Which action
resolves the issue?
Refer to the exhibit A network engineer is troubleshooting an AAA authentication issue for R1 from
R2 When an engineer tries to open a telnet connection to R1 it opens the connection but shows a
%Authorization failed error message on the terminal and closes the connection silently Which action
resolves the issue?Q: 14
Refer to the exhibit.
 Refer to the exhibit A network engineer is troubleshooting an AAA authentication issue for R1 from
R2 When an engineer tries to open a telnet connection to R1 it opens the connection but shows a
%Authorization failed error message on the terminal and closes the connection silently Which action
resolves the issue?
Refer to the exhibit A network engineer is troubleshooting an AAA authentication issue for R1 from
R2 When an engineer tries to open a telnet connection to R1 it opens the connection but shows a
%Authorization failed error message on the terminal and closes the connection silently Which action
resolves the issue?
 Refer to the exhibit A network engineer is troubleshooting an AAA authentication issue for R1 from
R2 When an engineer tries to open a telnet connection to R1 it opens the connection but shows a
%Authorization failed error message on the terminal and closes the connection silently Which action
resolves the issue?
Refer to the exhibit A network engineer is troubleshooting an AAA authentication issue for R1 from
R2 When an engineer tries to open a telnet connection to R1 it opens the connection but shows a
%Authorization failed error message on the terminal and closes the connection silently Which action
resolves the issue?Options
Discussion
D . The fact that authentication works but you get '%Authorization failed' points to authorization rules on the TACACS+ server, not connectivity or host IP config. Usually means the user isn't allowed to start a shell session on R1. I'm not 100% sure, but similar issues in practice were always fixed by updating command authorization on the server. Someone double check?
Its D. Pretty sure the trap is option C but that would hit authentication not authorization. Seen similar on exam reports.
Be respectful. No spam.
Question 14 of 35

