Q: 17
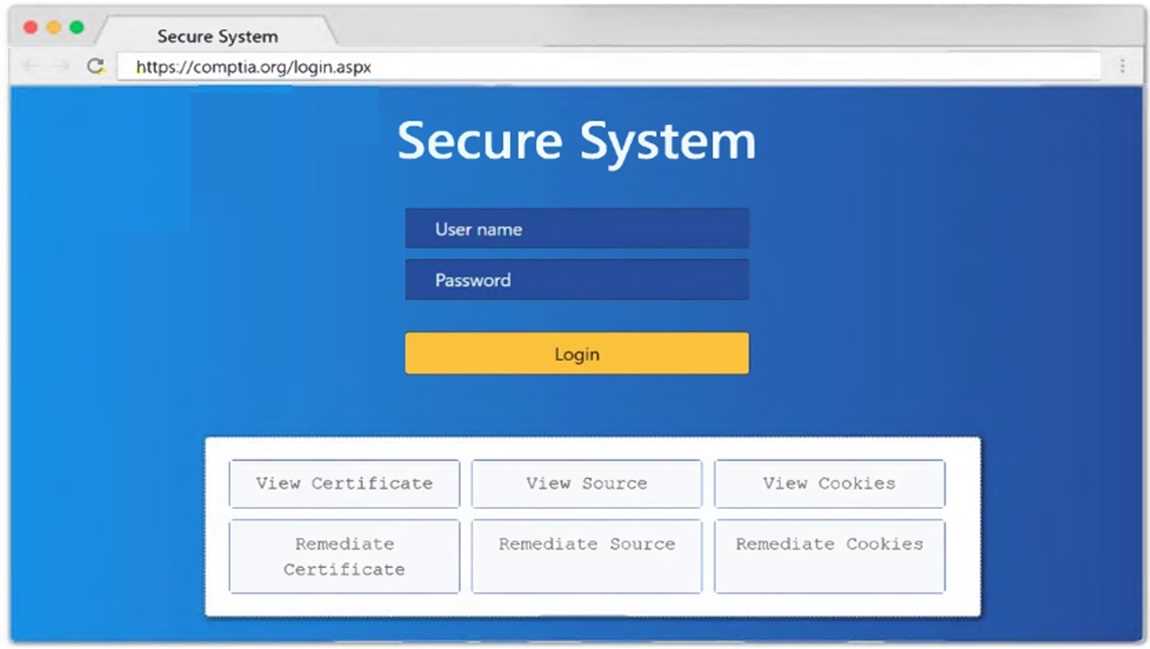
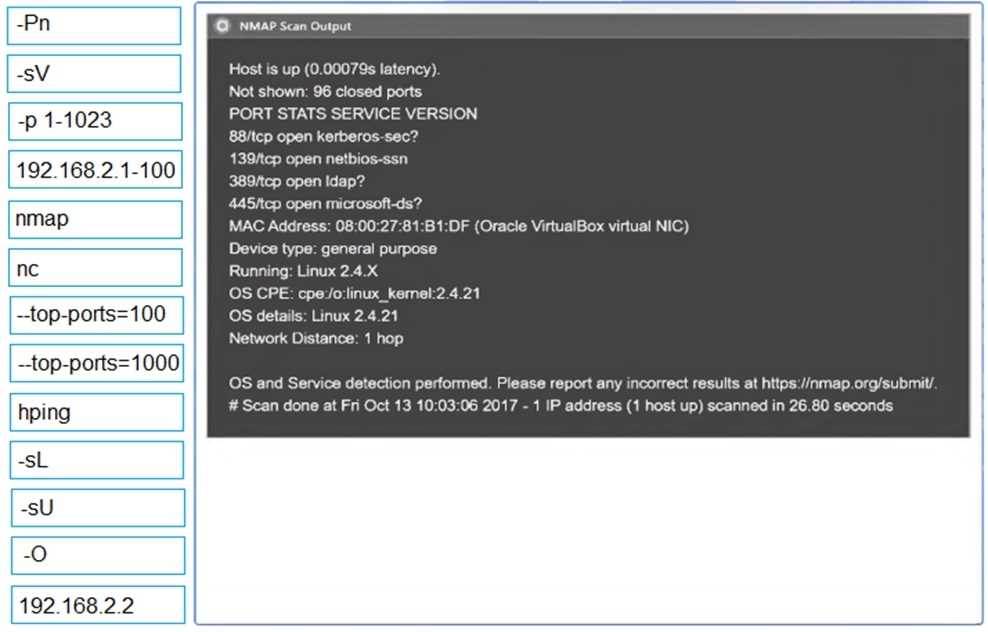
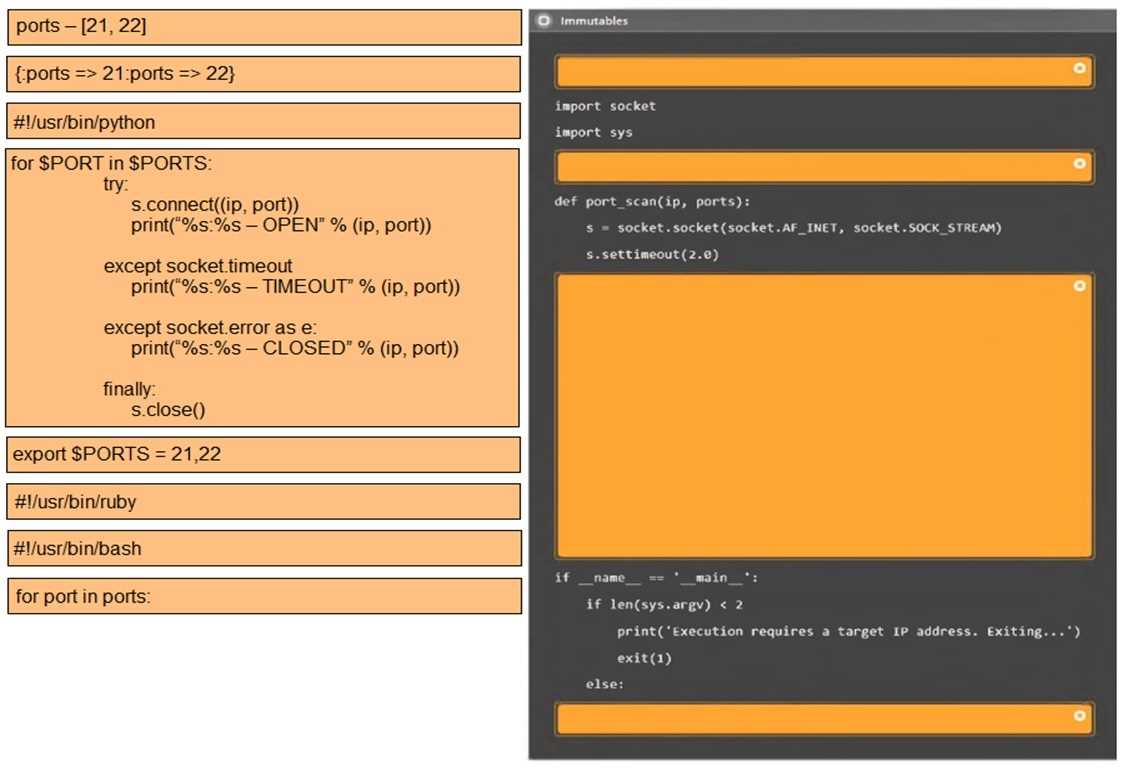
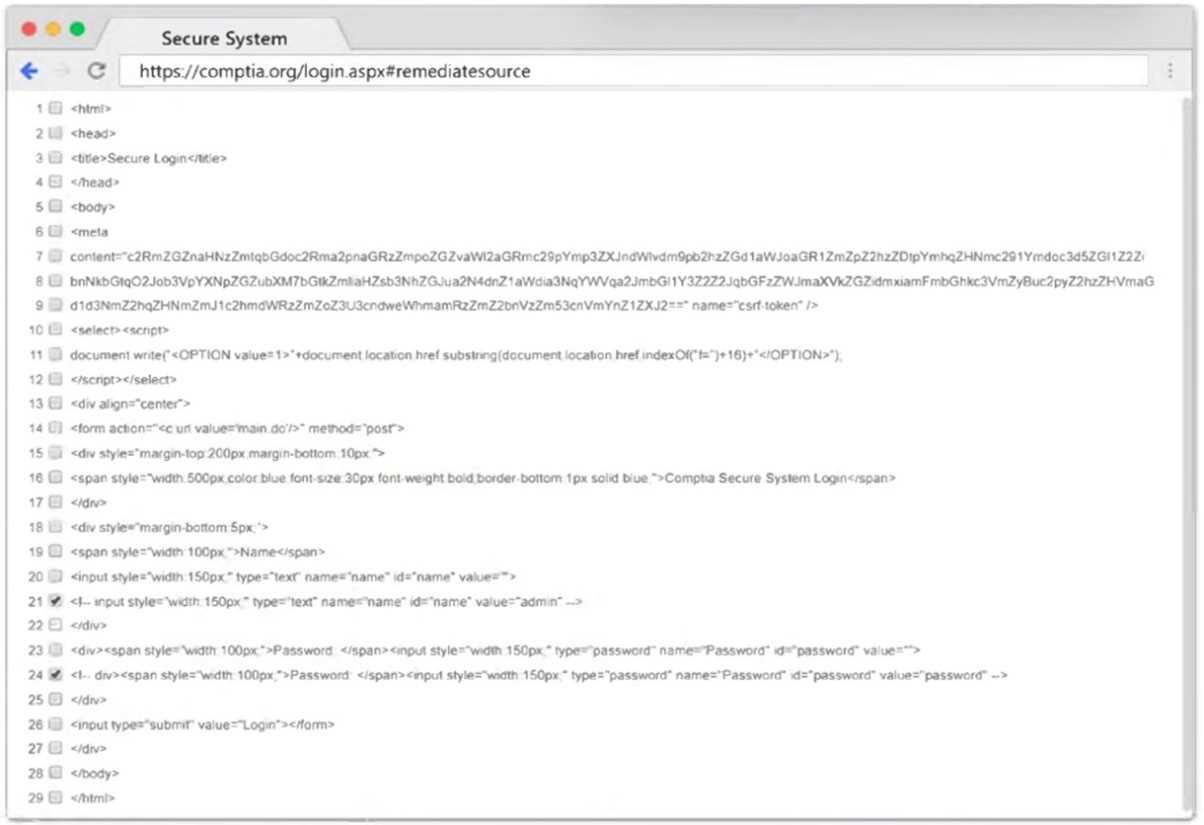
[Attacks and Exploits] SIMULATION Using the output, identify potential attack vectors that should be further investigated. 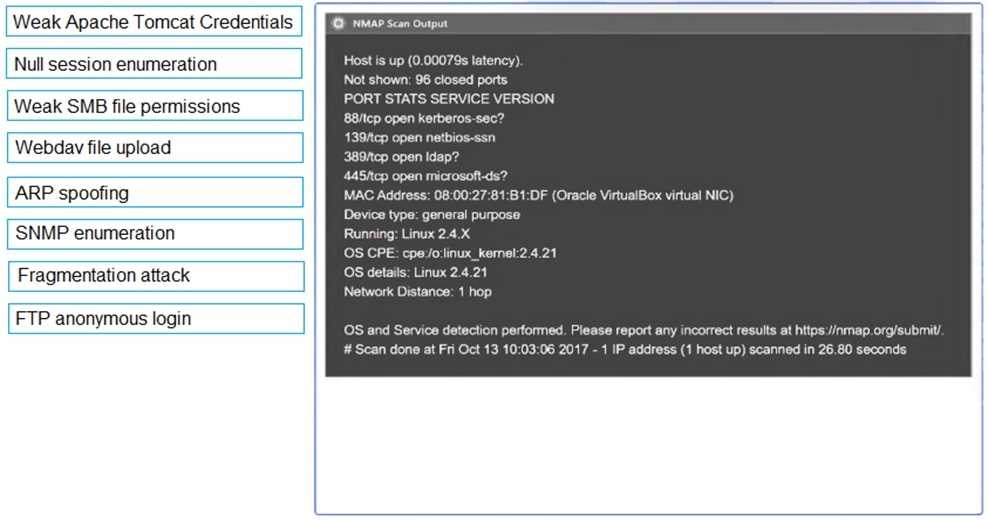
Your Answer
Discussion
Not FTP or SNMP here, those ports aren’t open based on the Nmap scan. Pretty sure it’s null session enumeration and weak SMB file permissions since SMB (139/445) is exposed. Wouldn’t focus on other vectors from these results.
Yeah, those ports (139/445) scream SMB risks to me. I'd say null session enumeration plus weak SMB file permissions should be looked at. That combo is classic for older systems based on the scan. Pretty sure that's what they're testing for but let me know if you see something else.
Yeah, this lines up with what I remember from recent exam reports, SMB ports open means check for null session and file share issues. Null session enumeration and weak SMB file permissions seem spot on.
Null session enumeration and weak SMB file permissions look like the right attack vectors here. Really clear details in those screenshots, makes this type of analysis a lot easier.
Makes sense to investigate null session enumeration and weak SMB file permissions in this case.
Anyone using the official CompTIA Pentest+ book or practice labs, which attack vectors match this kind of SMB scan output?
Null session enumeration and anonymous SMB share access. I picked those since ports 139 and 445 are open, which usually means SMB risks, but maybe anonymous shares is too generic compared to weak permissions. I'm not 100 percent on this, could be a trap if they're looking for specific wording.
Be respectful. No spam.