Q: 15
HOTSPOT -You are a security analyst tasked with hardening a web server. You have been given a list of HTTP payloads that were flagged as malicious.
INSTRUCTION - Giving the following attack signatures, determine the attack type, and then identify the associated remediation to prevent the attack in the future. If at any time you would like to bring back the initial state of the simulation, please click the Reset All button. Hot Area:
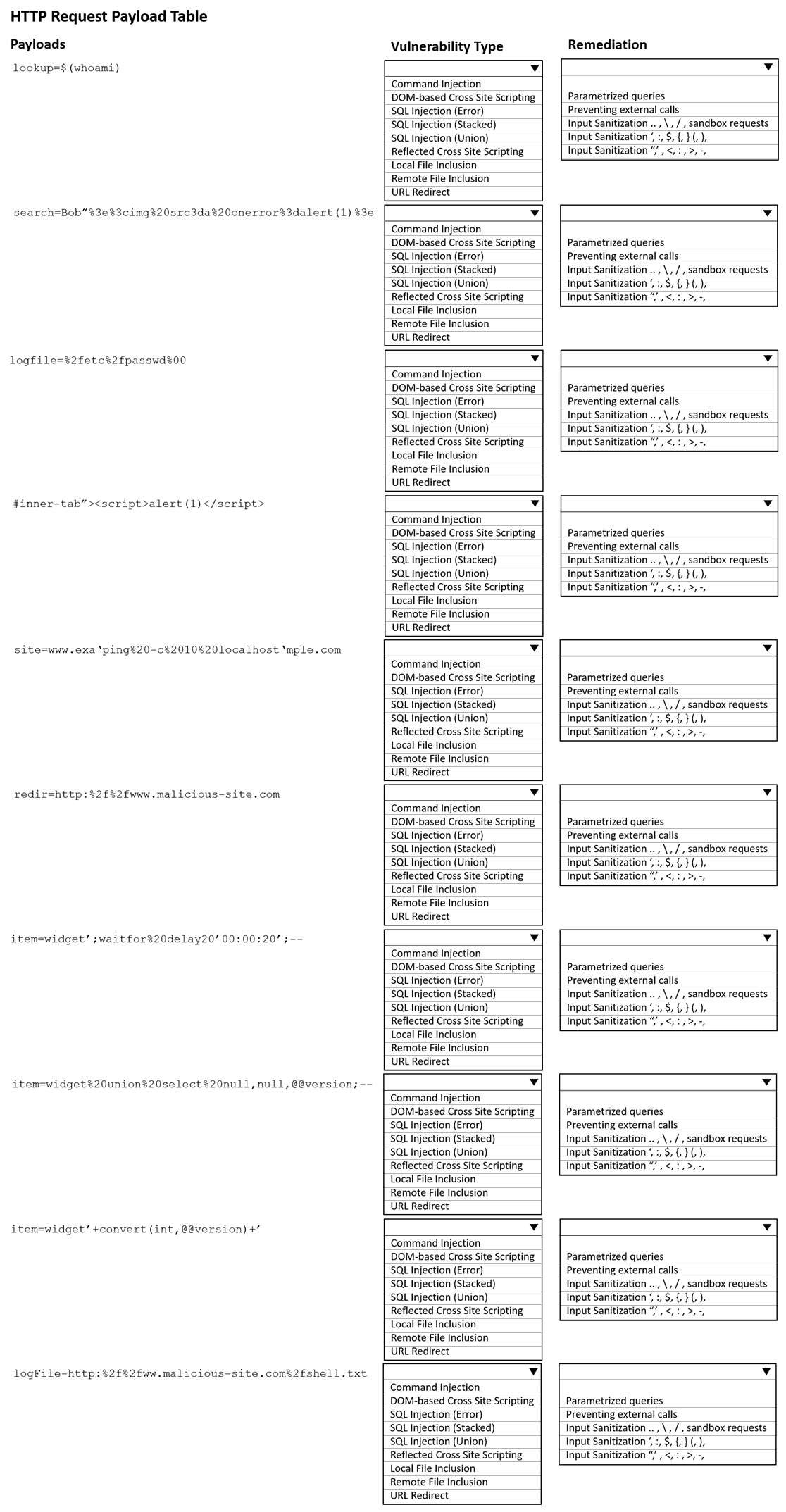
Your Answer
Discussion
Kinda tricky if you miss that file inclusion and command injection both usually show up, but the right mitigation flips for each. For command injection, just sanitizing input isn't enough, so blocking external system calls is needed. Seen exam reports flag that mismatch a lot. Agree?
Makes sense, the match between each payload type and remediation lines up with standard hardening controls. Stuff like parameterized queries for SQLi and input sanitization for XSS are pretty much textbook. Saw similar groupings in practice sets so I think this is right.
Anyone use the official Pentest+ practice test to prep for these remediation pairings?
Not totally sure but I think command injection is best blocked by disabling external calls, not just filtering inputs.
Not sure I agree with picking input sanitization for the command injection ones. Usually, preventing external calls is safer since just filtering input could miss some bypasses. Think that was a common trap on similar practice questions.
Ugh, these hotspot draggers are always confusing. I picked escaping quotes for the SQLi ones.
Great breakdown, really clear structure on each attack. Anyone else seeing similar payloads on practice sets?
Be respectful. No spam.

