HOTSPOT [Information Gathering and Vulnerability Scanning] A penetration tester is performing reconnaissance for a web application assessment. Upon investigation, the tester reviews the robots.txt file for items of interest. INSTRUCTIONS Select the tool the penetration tester should use for further investigation. Select the two entries in the robots.txt file that the penetration tester should recommend for removal. 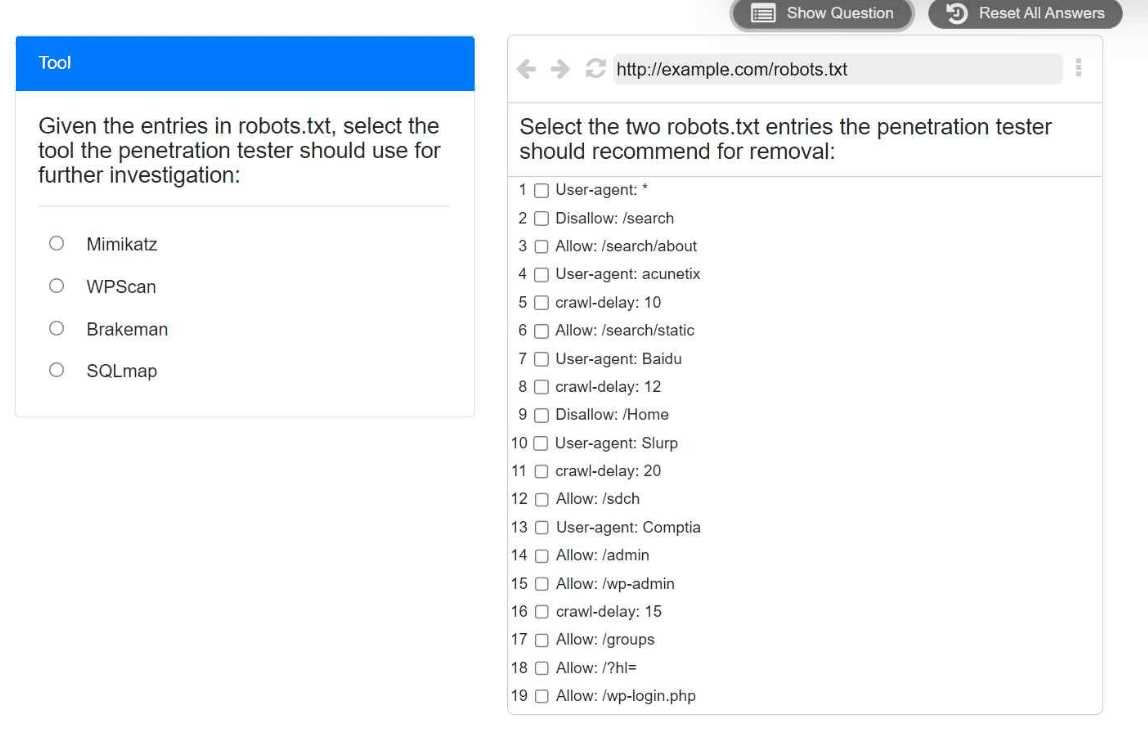
WPScan is the way to go since it's tailored for WordPress stuff. For removal, I’d pick the ALLOW: /ADMIN and ALLOW: /WP-ADMIN entries because they give away admin paths. Pretty sure that’s right based on similar practice questions.
Why not pick SQLmap here instead of WPScan? I get that WPScan is for WordPress, but if the robots.txt revealed some SQLi-prone paths, wouldn't SQLmap make more sense? Feels like a trap for people not checking the CMS details.

