Q: 11
SIMULATION
-
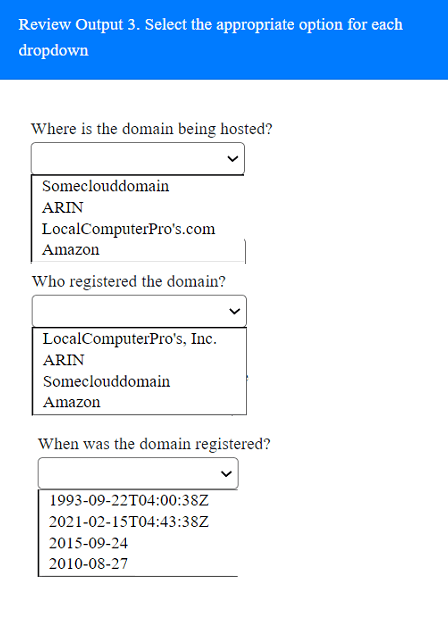
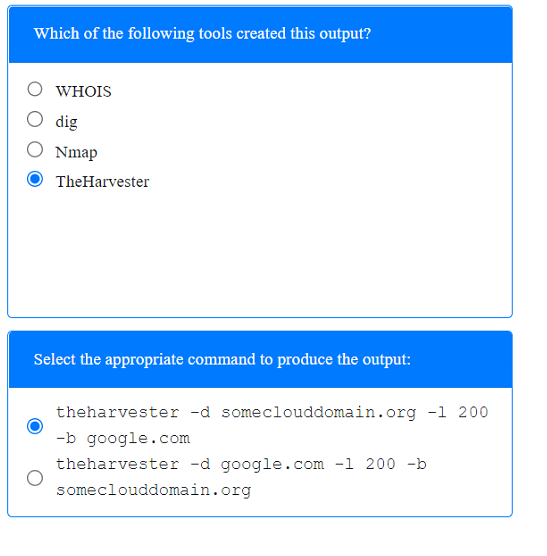
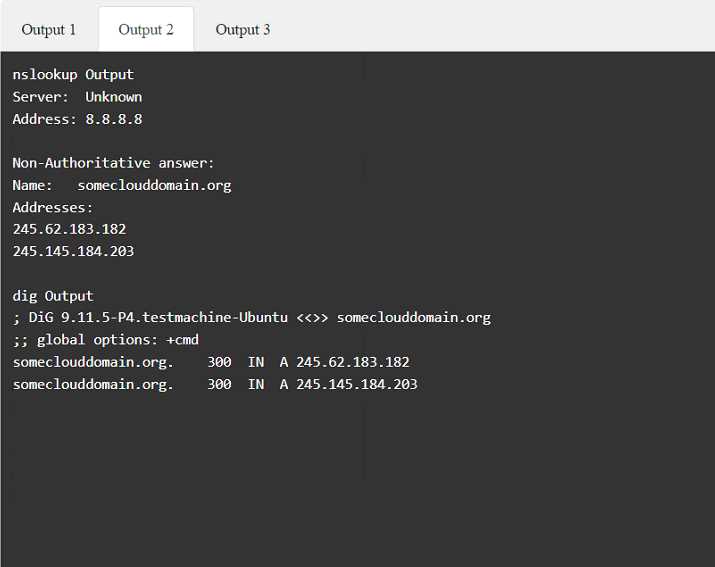
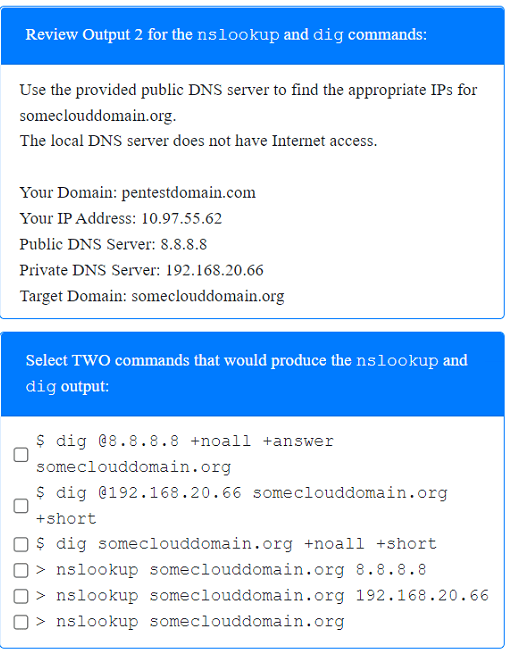
A penetration tester has been provided with only the public domain name and must enumerate additional information for the public-facing assets.
INSTRUCTIONS
-
Select the appropriate answer(s), given the output from each section.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button. 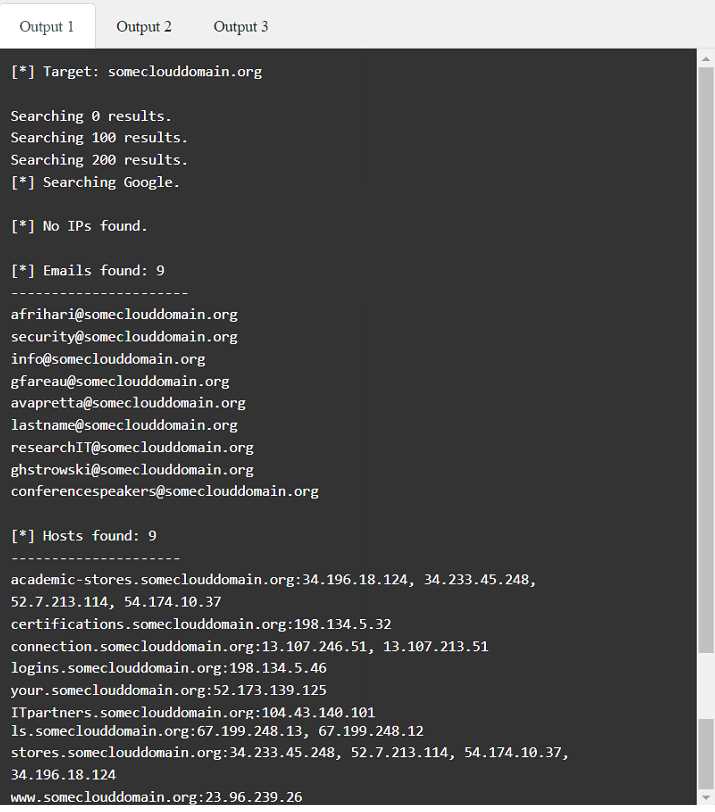
Your Answer
Discussion
Really like how direct this setup is!
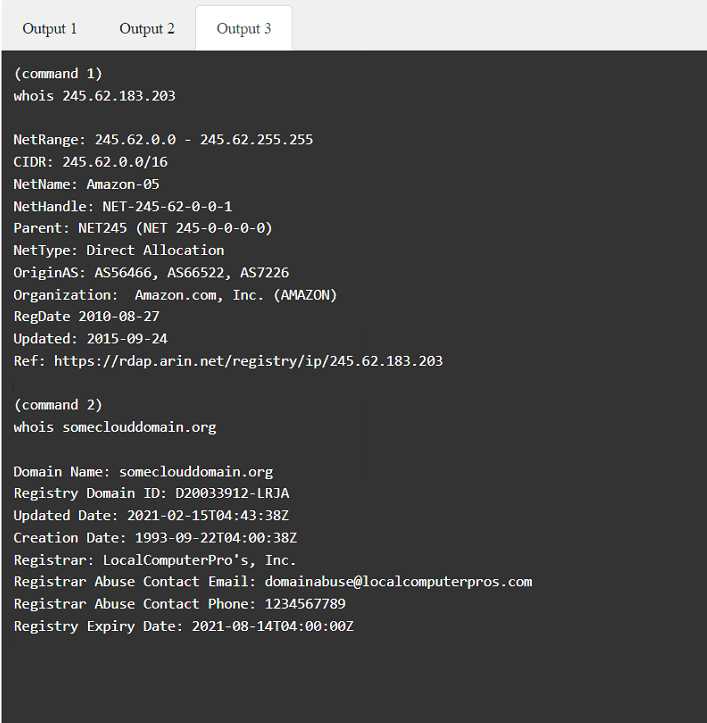
theharvester, dig/nslookup 8.8.8.8, amazon, LocalComputerPro's, 1993-09-22T04:00:38Z
theharvester, dig/nslookup 8.8.8.8, amazon, LocalComputerPro's, 1993-09-22T04:00:38Z
Had something like this in a mock-Amazon for hosting, LocalComputerPro's as registrar, 1993-09-22T04:00:38Z for registration date.
Totally hinges on which DNS server is accessible-if the local one is down, you have to point dig or nslookup at 8.8.8.8 for it to work. Pretty sure that's what they're testing here, especially since exam reports show similar twists.
Amazon for hosting, not Microsoft. Image clearly says Amazon owns the IP space, easy to miss if rushing.
Option: Microsoft.
Yeah, this one's pretty straightforward. For the OSINT part, it's theharvester with Google as the source, then dig and nslookup both pointed at 8.8.8.8 since local DNS is cut off. Hosting provider shows up as Amazon (so probably AWS), registered by LocalComputerPro's, date is 1993-09-22T04:00:38Z. I think that's solid but chime in if you spot anything off.
Anyone checked the official practice lab or reviewed output screenshots in the study guide for this? Not totally sure.
Be respectful. No spam.