 Based on the ZTNA tag, the security posture of the remote endpoint has changed.
What will happen to endpoint active ZTNA sessions?
Based on the ZTNA tag, the security posture of the remote endpoint has changed.
What will happen to endpoint active ZTNA sessions?Q: 1
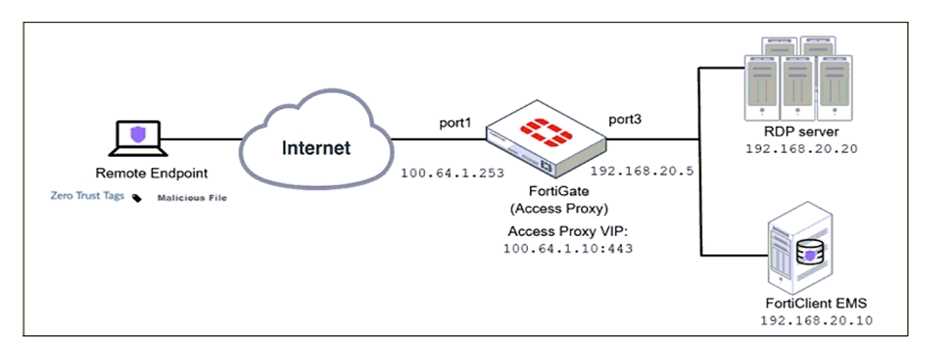
Refer to the exhibit.
 Based on the ZTNA tag, the security posture of the remote endpoint has changed.
What will happen to endpoint active ZTNA sessions?
Based on the ZTNA tag, the security posture of the remote endpoint has changed.
What will happen to endpoint active ZTNA sessions?
 Based on the ZTNA tag, the security posture of the remote endpoint has changed.
What will happen to endpoint active ZTNA sessions?
Based on the ZTNA tag, the security posture of the remote endpoint has changed.
What will happen to endpoint active ZTNA sessions?Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 2
Refer to the exhibits.
Exhibit A shows a network diagram. Exhibit B shows the firewall policy configuration and a VIP object
configuration.
The WAN (port1) interface has the IP address 10.200.1.1/24.
The LAN (port3) interface has the IP address 10.0.1.254/24.
The administrator disabled the WebServer firewall policy.
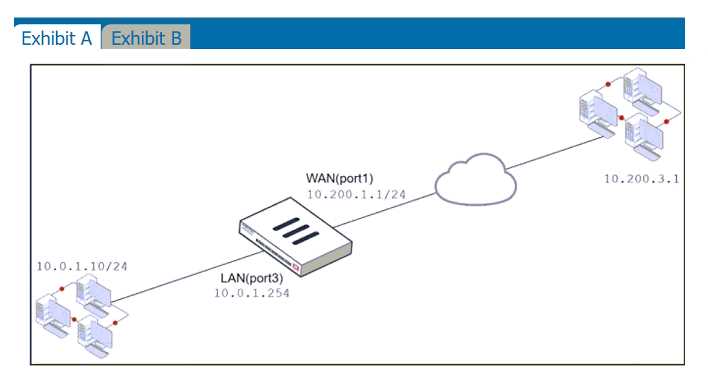
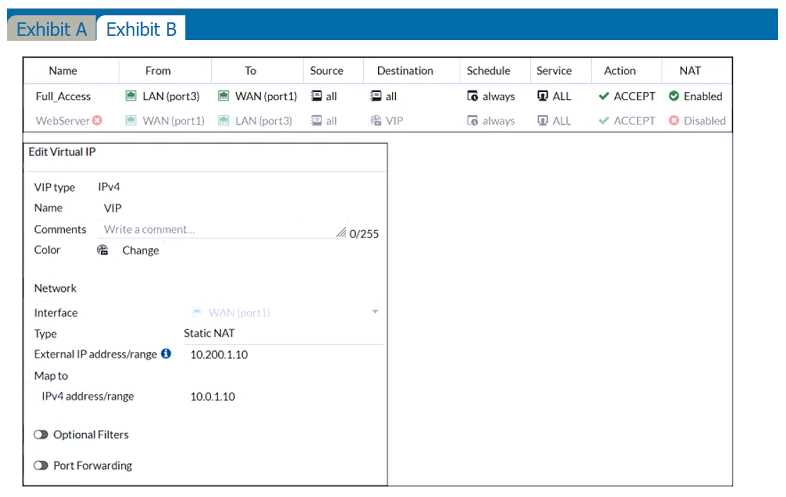 Which IP address will be used to source NAT the traffic, if a user with address 10.0.1.10 connects over
SSH to the host with address 10.200.3.1?
Which IP address will be used to source NAT the traffic, if a user with address 10.0.1.10 connects over
SSH to the host with address 10.200.3.1?
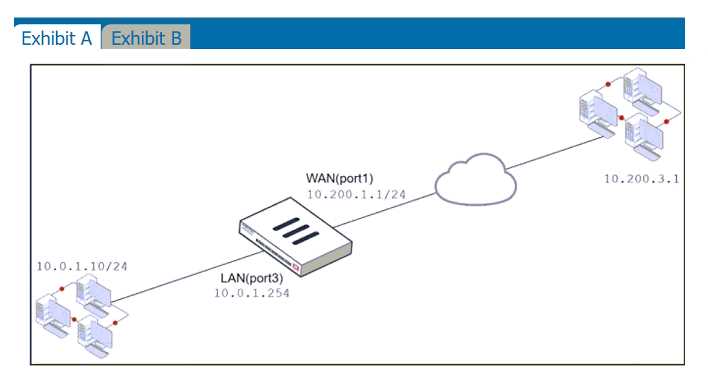
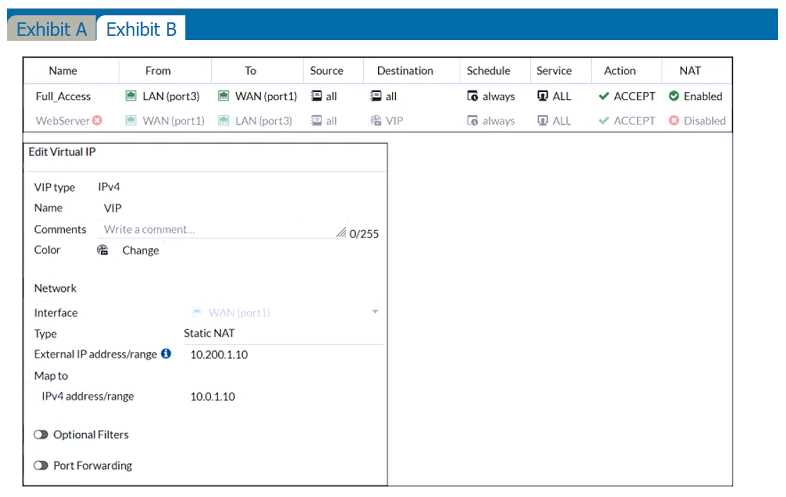 Which IP address will be used to source NAT the traffic, if a user with address 10.0.1.10 connects over
SSH to the host with address 10.200.3.1?
Which IP address will be used to source NAT the traffic, if a user with address 10.0.1.10 connects over
SSH to the host with address 10.200.3.1?Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 3
FortiGate is configured as a policy-based next-generation firewall (NGFW) and is applying web
filtering and application control directly on the security policy. Which two other security profiles can
you apply to the security policy? (Choose two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 4
Refer to the exhibit to view the firewall policy
 Why would the firewall policy not block a well-known virus, for
example eicar?
Why would the firewall policy not block a well-known virus, for
example eicar?
 Why would the firewall policy not block a well-known virus, for
example eicar?
Why would the firewall policy not block a well-known virus, for
example eicar?Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 5
Which three statements are true regarding session-based authentication? (Choose three.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 6
Which statement about the deployment of the Security Fabric in a multi-VDOM environment is true?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 7
Refer to the exhibits.
Exhibit A
 Exhibit B
Exhibit B
 The exhibit contains a network interface configuration, firewall policies, and a CLI console
configuration.
How will FortiGate handle user authentication for traffic that arrives on the LAN interface?
The exhibit contains a network interface configuration, firewall policies, and a CLI console
configuration.
How will FortiGate handle user authentication for traffic that arrives on the LAN interface?
 Exhibit B
Exhibit B
 The exhibit contains a network interface configuration, firewall policies, and a CLI console
configuration.
How will FortiGate handle user authentication for traffic that arrives on the LAN interface?
The exhibit contains a network interface configuration, firewall policies, and a CLI console
configuration.
How will FortiGate handle user authentication for traffic that arrives on the LAN interface?Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 8
When a firewall policy is created, which attribute is added to the policy to support recording logs to a
FortiAnalyzer or a FortiManager and improves functionality when a FortiGate is integrated with
these devices?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 9
Refer to the exhibit.
The exhibit shows the output of a diagnose command.
 What does the output reveal about the policy route?
What does the output reveal about the policy route?
 What does the output reveal about the policy route?
What does the output reveal about the policy route?Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Question 1 of 20 · Page 1 / 2

