Q: 10
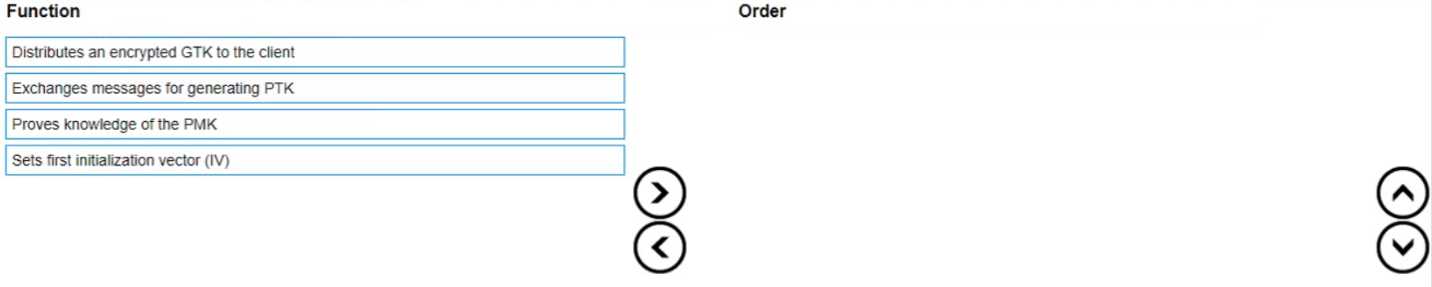
DRAG DROP List the WPA 4-Way Handshake functions in the correct order.
Drag & Drop
Discussion
Exchanges messages for generating PTK, then proves knowledge of the PMK, distributes encrypted GTK, sets first IV.
PTK exchange, then prove PMK, send encrypted GTK, finally set IV. Jason's order mixes up steps-GTK is after PMK proof.
I think it's PTK exchange first, then PMK proof, after that distribute encrypted GTK, and finally set the IV. That's how the 4-way handshake actually flows in WPA security. Pretty sure this is right based on how key establishment works.
Distributes GTK, proves PMK, exchanges for PTK, sets IV. I get why people put PTK first, but I remember from some practice exams the encrypted GTK step coming right after handshake. Maybe a wording trap here?
PTK exchange, distributes GTK, proves PMK, then set IV.
Honestly I think distributing the GTK happens right after PTK is generated, but I might be mixing up 3 and 2. Anyone else see it this way in their studies?
Honestly I think distributing the GTK happens right after PTK is generated, but I might be mixing up 3 and 2. Anyone else see it this way in their studies?
Be respectful. No spam.