Had something like this in a mock, and B was right. Application control is what uses those IPS protocol decoders to spot/block app signatures, not just web stuff like D. Pretty sure that's what they're after here, but correct me if you think otherwise.
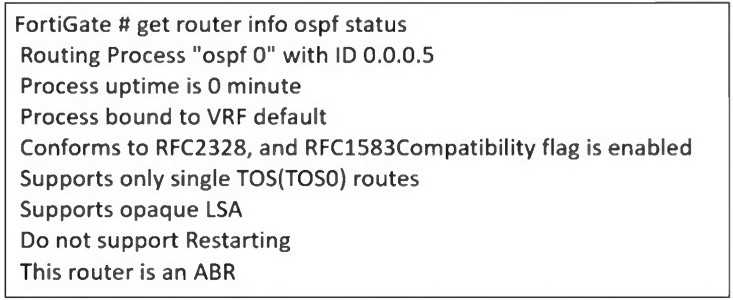 An administrator is checking the OSPF status of a FortiGate device and receives the output shown in
the exhibit.
What two conclusions can the administrator draw? (Choose two.)
An administrator is checking the OSPF status of a FortiGate device and receives the output shown in
the exhibit.
What two conclusions can the administrator draw? (Choose two.)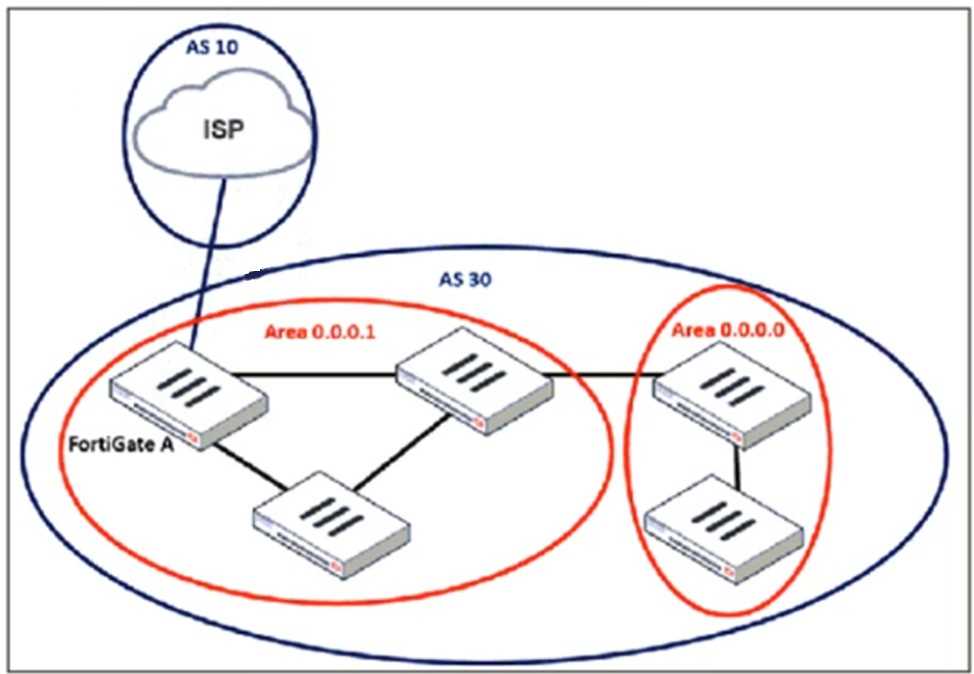 An administrator must configure a loopback as a BGP source to connect to the ISP.
Which two commands are required to establish the connection? (Choose two.)
An administrator must configure a loopback as a BGP source to connect to the ISP.
Which two commands are required to establish the connection? (Choose two.)A and B here. eBGP with loopback needs ebgp-enforce-multihop to let the connection work, and update-source points BGP to use the loopback IP. D is for next hop recursion which isn’t required in this ask. Pretty sure about this combo but correct me if you’ve done it differently in practice.
I think it should be A and B, since for eBGP with a loopback you need to allow multihop and set update-source. Not 100% but I don't see C or D fitting here, since they're for iBGP or recursive next hop situations. Agree?
 What two conclusions can you draw from the corresponding LAN interface? (Choose two.)
What two conclusions can you draw from the corresponding LAN interface? (Choose two.)B and C match what's in the official guide and practice tests for FortiLink with MCLAG. The LAG has to be 802.3ad, and FortiLink manages VLANs. Not 100% sure unless they ask about loop prevention, though. Disagree?
Kinda feel like A is valid here. Since you have multiple switches, enabling STP or RSTP seems important to prevent loops at L2. I've seen network loops in similar setups if STP isn't enabled. Not completely sure though, maybe I'm missing something about how FortiLink handles redundancy? Agree?

