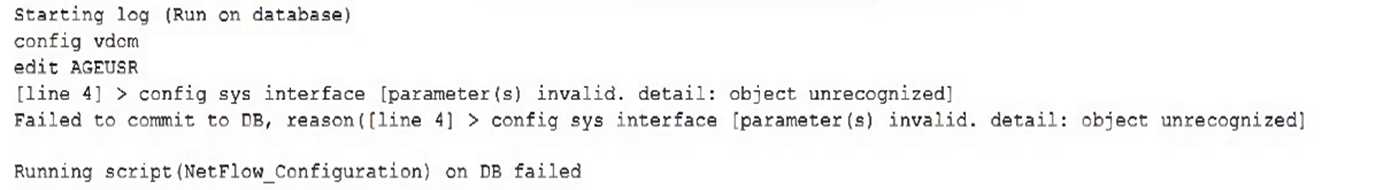
 What must the administrator do to successfully apply the NetFlow configuration script and avoid the
object unrecognized error?
What must the administrator do to successfully apply the NetFlow configuration script and avoid the
object unrecognized error?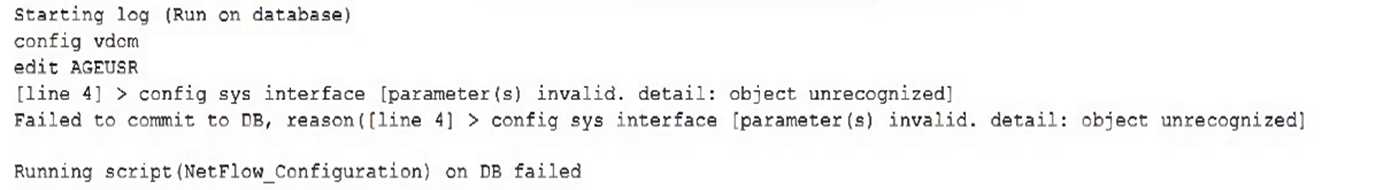 What must the administrator do to successfully apply the NetFlow configuration script and avoid the
object unrecognized error?
What must the administrator do to successfully apply the NetFlow configuration script and avoid the
object unrecognized error?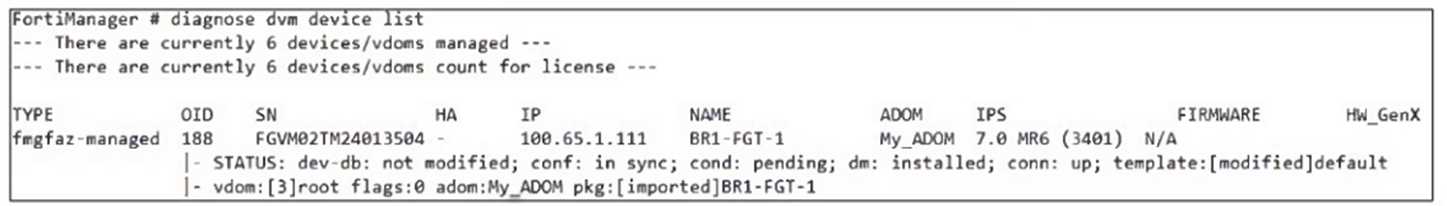 Which two statements about the output are true? (Choose two.)
Which two statements about the output are true? (Choose two.)If they're asking about current status, then A and D fit. The "Modified" highlights the DB mismatch (A), and the template override logic (D) is default FMG behavior. But if they'd specified after install, C could flip in. Anyone else catch that fine print?
I see why you might question C/D, but for this one A and D fit better. "Config Status: Modified" points to a mismatch between FortiGate and the device-level DB (A), and if there's a template change, it'll overwrite device-level settings (D). Pretty sure that's what they're after here, unless I'm missing something subtle in the exhibit.
 FortiManager is operating behind a network address translation (NAT) device, and the administrator
configured the FortiManager NATed IP address under the FortiManager system administration
settings.
What is the expected result during discovery?
FortiManager is operating behind a network address translation (NAT) device, and the administrator
configured the FortiManager NATed IP address under the FortiManager system administration
settings.
What is the expected result during discovery?This just comes down to which address FortiGate will use after discovery. Since FMG is behind NAT, only the NATed IP (100.65.0.120) gets pushed to the FortiGate, not both public and private. So D makes sense here. If I'm missing something subtle in the exhibit, let me know.
Pretty sure it's D since backup mode disables using policy packages, only scripts can push changes out. Happened to me in a lab. If I'm missing some trick with firmware or ADOM, let me know!
I get why some pick C, but with ADOM in backup mode, policy package install isn't possible. Only scripts (D) can actually push changes in that state. Ran into this on a similar question before, so I'm pretty sure that's the catch here.
Workspace mode (D) makes sense here since it's specifically built to prevent admins from overwriting each other in the same ADOM. I've seen this called out in Fortinet's official docs and in a few practice exams. Not 100% sure if workflow (B) could also count, but workspace is usually what's expected for conflict prevention. Anyone using lab environments will see this in action.
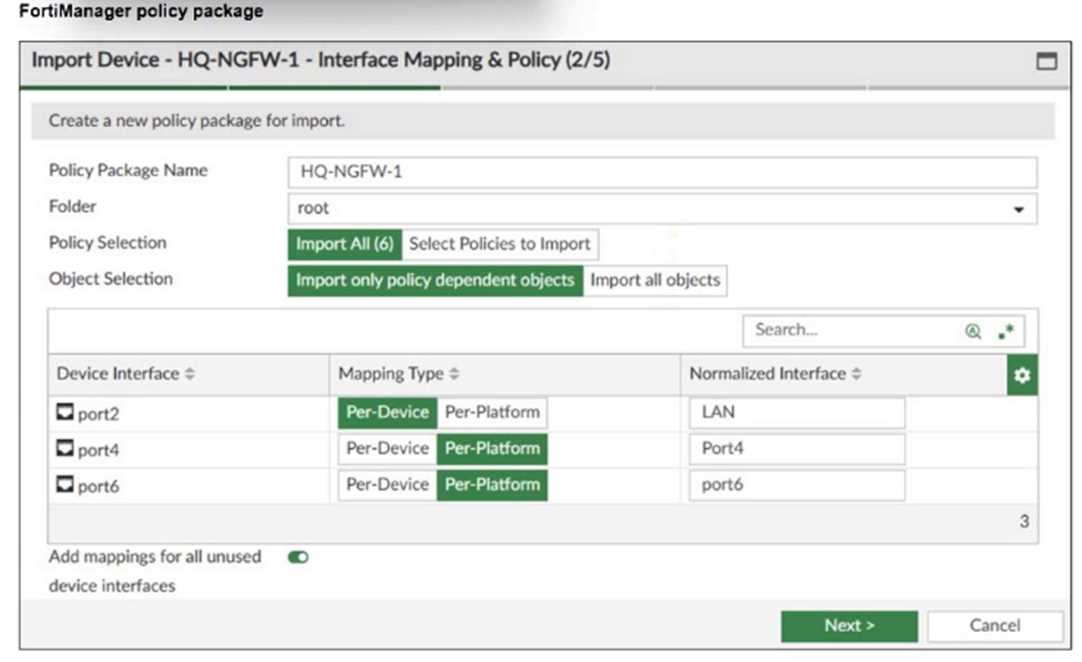 An administrator added a FortiGate device to FortiManager with the default object settings at the
ADOM layer.
What can you conclude from the import policy package process of the HQ-NGFW- 1 device?
An administrator added a FortiGate device to FortiManager with the default object settings at the
ADOM layer.
What can you conclude from the import policy package process of the HQ-NGFW- 1 device?Doesn't B make more sense if port4 wasn't mapped automatically? Feels like C is a trap if you miss how FortiManager handles interfaces that aren't pre-existing. Anyone else see this kind of confusion in the interface mapping step?
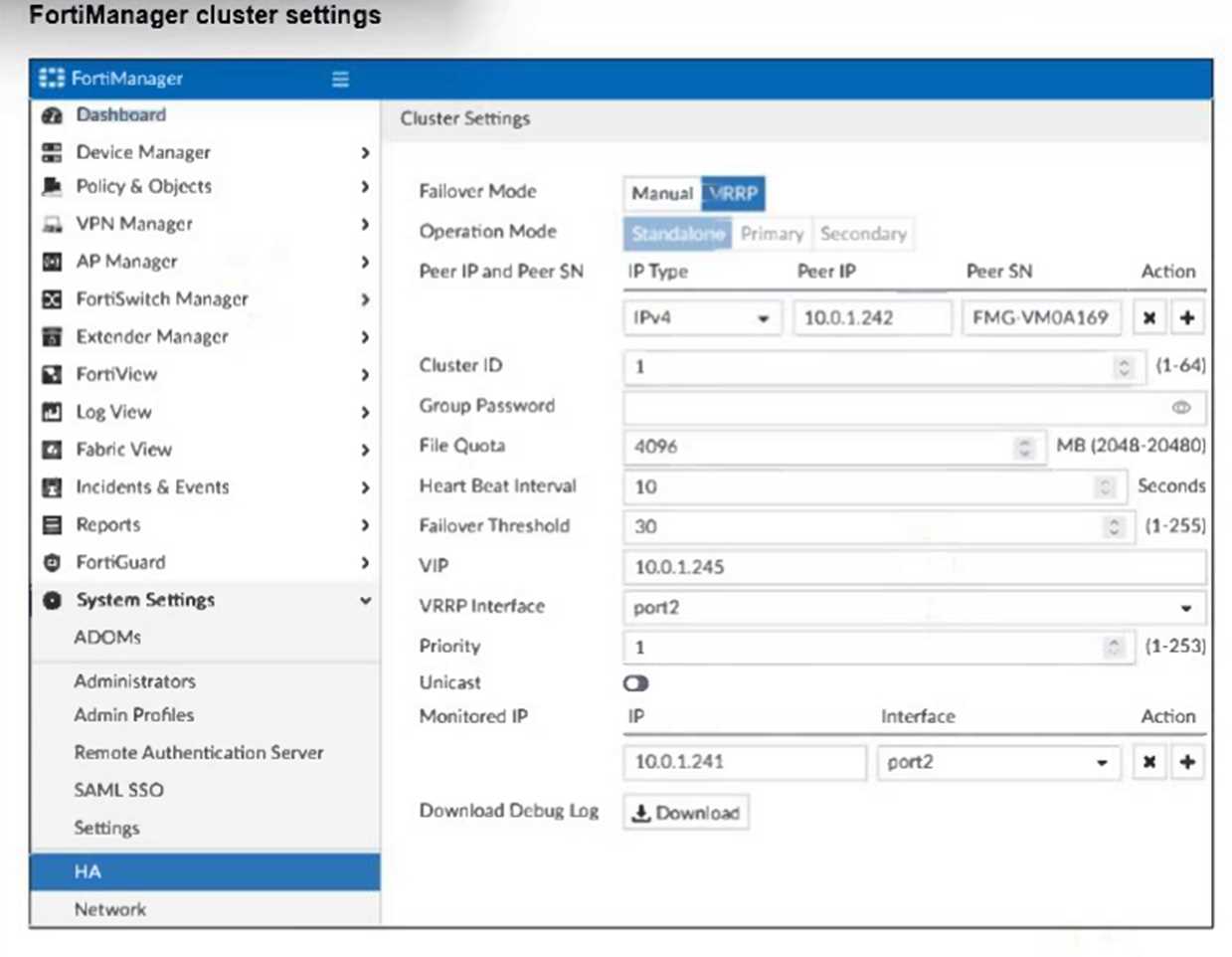 If the monitored interface for the primary FortiManager device fails, what must you do to maintain
high availability (HA)?
If the monitored interface for the primary FortiManager device fails, what must you do to maintain
high availability (HA)?Anyone tried implementing workflow approval in a real FortiManager lab? Official docs and hands-on labs explain this approach well, as it really blocks repeat misconfigs. I think D makes sense here but open to other experiences.
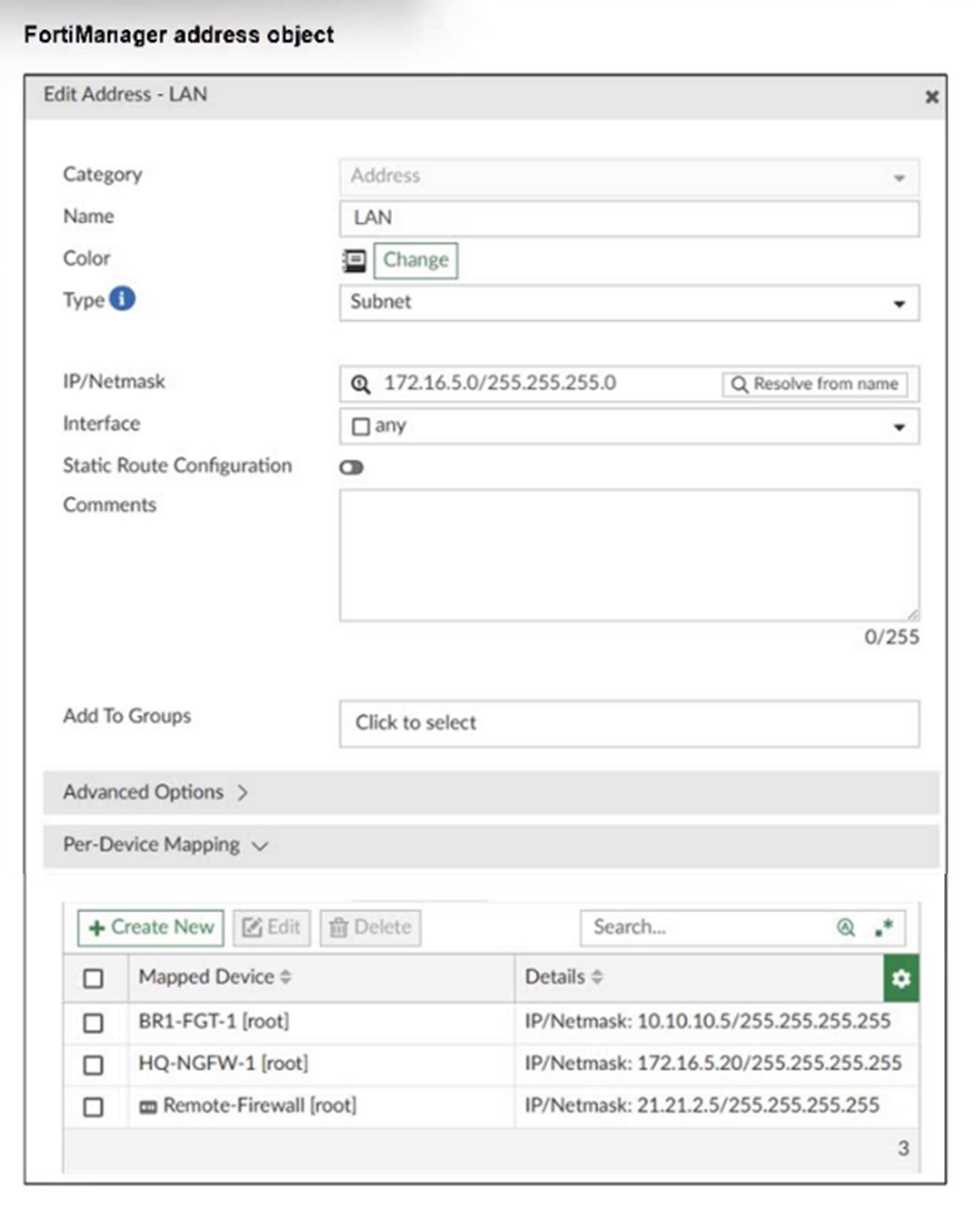 An administrator has created a firewall address object that is used in multiple policy packages for
multiple FortiGate devices in an ADOM.
After the installation operation is performed, which IP/netmask will be installed on Remote-Firewall
[VDOM1] for the LAN firewall address object?
An administrator has created a firewall address object that is used in multiple policy packages for
multiple FortiGate devices in an ADOM.
After the installation operation is performed, which IP/netmask will be installed on Remote-Firewall
[VDOM1] for the LAN firewall address object?C/D? The per-device mapping trips people up. If you just looked at the default address you'd say D, but since Remote-Firewall [VDOM1] has its own entry (21.21.2.5/32) that's what actually gets pushed by FortiManager. I'm 90% sure it's A for this scenario, unless I missed something subtle in the exhibit.

