Stallings, W. (2017). Network Security Essentials: Applications and Standards (6th ed.). Pearson.
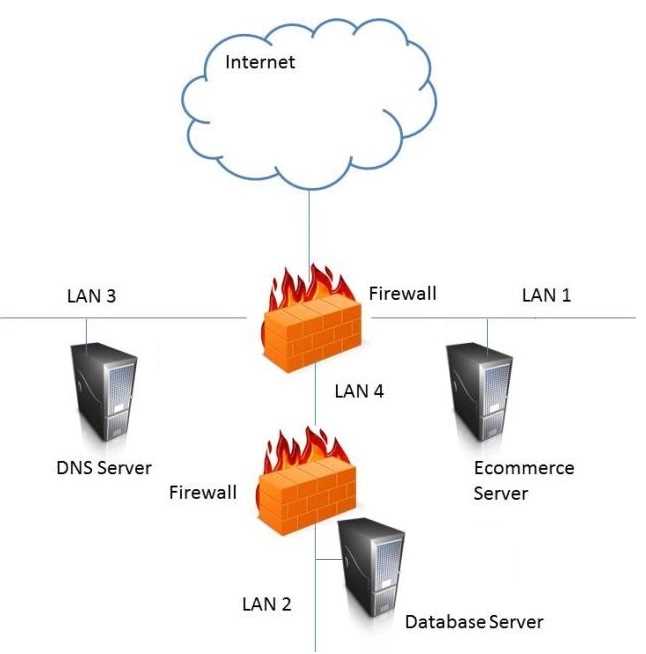
Reference: Chapter 9, Section 9.2, "Firewall Configurations," particularly the discussion on the "Screened Subnet Firewall System" (p. 297, Figure 9.5c). This section details the dual-firewall architecture where the DMZ is the isolated network between an external and internal firewall, which is the standard design for securely hosting systems that require external access without exposing the internal network.
Zwicky, E. D., Cooper, S., & Chapman, D. B. (2000). Building Internet Firewalls (2nd ed.). O'Reilly & Associates.
Reference: Chapter 6, "Firewall Architectures," specifically the section on "Screened Subnet" (pp. 138-142). This source describes the screened subnet (DMZ) as the canonical solution for allowing access from the Internet to selected hosts while protecting the internal network. Placing a WAP for semi-trusted users in this zone is a direct application of this principle.
Cheswick, W. R., Bellovin, S. M., & Rubin, A. D. (2003). Firewalls and Internet Security: Repelling the Wily Hacker (2nd ed.). Addison-Wesley Professional.
Reference: Chapter 4, "Firewall-Friendly Protocols and the DMZ." The chapter explains that the purpose of a DMZ is to create a "neutral zone" for machines that need to be accessible from the outside but should not be trusted on the internal network. This concept directly applies to creating a network segment for contractors.