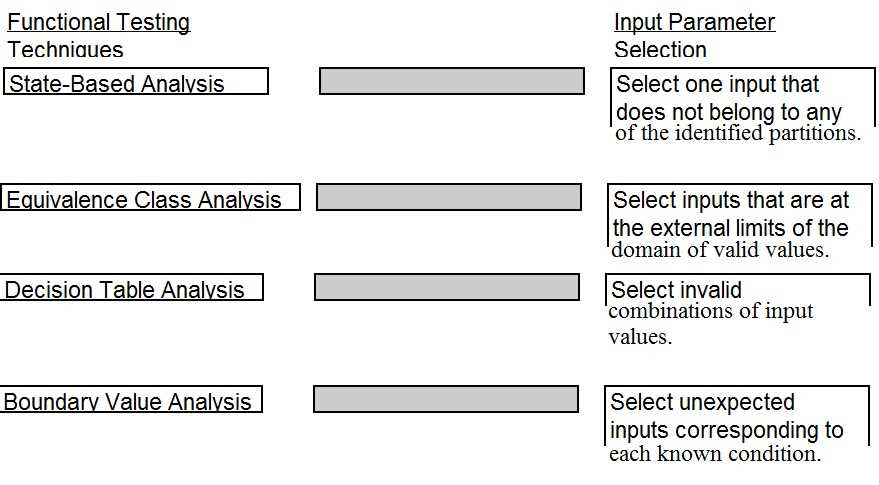
DRAG DROP A software security engineer is developing a black box-based test plan that will measure the system's reaction to incorrect or illegal inputs or unexpected operational errors and situations. Match the functional testing techniques on the left with the correct input parameters on the right.
Q: 16
Drag & Drop
Discussion
State-Based Analysis → not in any partition, Equivalence Class → external limits, Decision Table → invalid combos, Boundary Value → unexpected inputs for known condition. If these were defined by classic textbook examples the first two would actually be flipped.
State-Based → not in any partition, Equivalence Class → external limits, Decision Table → invalid combos, Boundary Value → unexpected inputs for each condition. Saw similar structure on official practice tests, this matches CISSP logic. Correct me if you see it another way.
Looks like it's State-Based Analysis → one input not in any partition, Equivalence Class Analysis → external domain limits, Decision Table Analysis → invalid combos, Boundary Value Analysis → unexpected inputs per known condition. Saw similar mapping in official guides, pretty sure this is correct but open to corrections.
State-Based Analysis → one input not in any partition, Equivalence Class Analysis → external domain limits, Decision Table Analysis → invalid combos, Boundary Value Analysis → unexpected inputs per condition. Had something like this in a mock, seems right.
State-Based Analysis -> unexpected inputs per known condition, Equivalence Class Analysis -> inputs at external domain limits, Decision Table Analysis -> invalid combo of input values, Boundary Value Analysis -> input outside all partitions. Official CISSP guide or practice tests cover these mappings.
Be respectful. No spam.
Question 16 of 35