Probably A, but does it specify if these servers use FSRM or just standard shares? That info could flip it between A and B.
Did you check the official guide or MS practice labs for how file screens work with FSRM in this scenario?
Probably A, but does it specify if these servers use FSRM or just standard shares? That info could flip it between A and B.
Did you check the official guide or MS practice labs for how file screens work with FSRM in this scenario?
You have a server that runs Windows Server 2022 and has the network adapters shown in the following table. 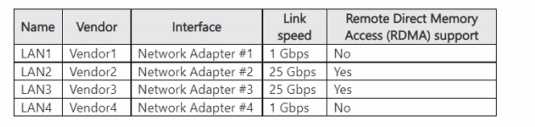
Your network contains an Active Directory forest. The forest contains two domains named contoso.com and east.contoso.com and the servers shown in the following table. 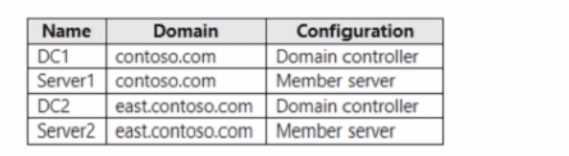
D here. Backup Operators in the contoso.com domain only get rights on DC1 and Server1, since those are in that domain. They won't have access to back up resources in east.contoso.com. Saw something similar pop up on practice sets, matches what they said too. Corrections welcome if I'm missing a detail!
Your network contains an Active Directory Domain Services (AD DS) domain. The domain contains a user named User1. User1 is a member of a group named Group1 and is in an organizational unit (OL)} named OU1. The domain has minimum password lengths configured as shown in the following table. 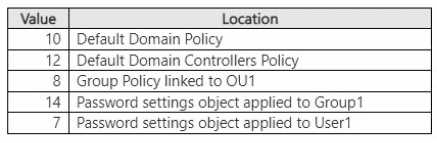
Doesn't the PSO with lowest precedence always override the domain policy if it's linked via Group1? Unless User1 has another direct PSO or a higher-precedence one applies somehow, looks like 7 chars is enforced. Someone correct me if I'm missing a nuance with OU-level policies here.
Pretty sure it's A here. JIT VM access specifically reduces the window that admin ports are open, which is what Azure exams usually focus on for security. D trips people up since Bastion hides public RDP, but it's not as granular for port lockdown. Disagree?
I get why people pick D, but for this you want to limit port exposure as much as possible, so A (JIT VM access) is better. Pretty sure Azure pushes JIT in these scenarios. Correct me if I'm missing some corner case.
Option C makes sense because Azure requires non-overlapping address ranges for S2S VPN, so reconfiguring VNet1 to 10.0.2.0/24 should be step one. The official docs and practice tests highlight this overlap issue a lot, but let me know if you see it differently!
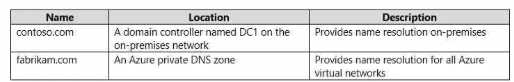 You need to ensure that names from fabrikam.com can be resolved from the on-premises network
Which two actions should you perform? Each correct answer presents part of the solution, NOTE:
Each correct selection Is worth one point
You need to ensure that names from fabrikam.com can be resolved from the on-premises network
Which two actions should you perform? Each correct answer presents part of the solution, NOTE:
Each correct selection Is worth one pointI actually thought B and E were enough since a stub zone can help with forwarding requests too. Pretty common to think stub zones do the trick, but maybe I'm missing something about the conditional forwarder requirement here. Trap for sure if you mix up stub vs forwarder.
A imo. Had something like this in a mock and the double-hop problem was exactly the scenario. Kerberos constrained delegation lets your creds pass from Server1 to Server3 through Server2, with less risk than unconstrained delegation. The other options don't really fix that hop issue. Pretty sure that's what they want here, but open to other takes.
I get why some might pick C, but that's more for cross-forest or when restricting which servers users can authenticate to. Here the double-hop issue is classic for remote PowerShell, so pretty sure A (Kerberos constrained delegation) is what solves it with minimal config. D's not relevant here since it's not about just relaxing restrictions overall. Let me know if I'm missing some nuance!
You have four testing devices that are configured with static IP addresses as shown in the following table. 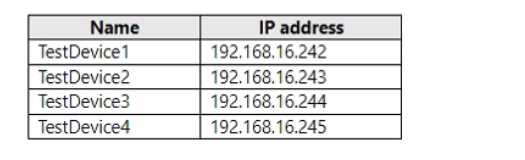
Conditional forwarder for contoso.com pointing to DC1 is what you want here. A standard forwarder would send all requests to DC1, which isn't right since only contoso.com should go that way. Pretty sure that's the intent, but open to other views if I'm missing a detail.
Yeah, you always start by creating the virtual network first so everything has a place to live. Then deploy the Azure AD DS instance, and finally tweak the vnet DNS settings so VMs can find the domain controllers. That sequence matches typical Azure domain join setups from what I remember. Let me know if anyone's seen a different order work!
All Yes here. Had something like this in a mock and the key is the replication scope-domain-wide for contoso.com means Server3 needs a secondary, but everything else lines up for AD DNS replication. Pretty sure that's right but open to correction if I missed anything subtle.
Looks like all three statements are true here. The replication scopes match up: contoso.com only replicates to DNS servers in its domain, so Server2 gets updates but Server3 would need a secondary zone. east.contoso.com is set to forest-wide replication, so Server1 will get those records too. Someone correct me if I missed a detail, but pretty sure it's Yes for all.