Q: 4
Note: This question is part of a series of questions that present the same scenario. Each question in
the series contains a unique solution that might meet the stated goals. Some question sets might
have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these
questions will not appear in the review screen.
You have an Azure application gateway that has Azure Web Application Firewall (WAF) enabled.
You configure the application gateway to direct traffic to the URL of the application gateway.
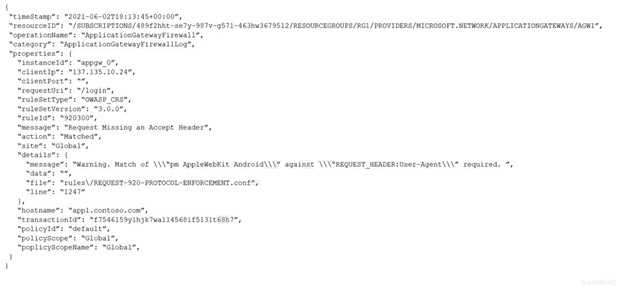
You attempt to access the URL and receive an HTTP 403 error. You view the diagnostics log and
discover the following error.
 You need to ensure that the URL is accessible through the application gateway.
Solution: You create a WAF policy exclusion for request headers that contain 137.135.10.24.
Does this meet the goal?
You need to ensure that the URL is accessible through the application gateway.
Solution: You create a WAF policy exclusion for request headers that contain 137.135.10.24.
Does this meet the goal?
 You need to ensure that the URL is accessible through the application gateway.
Solution: You create a WAF policy exclusion for request headers that contain 137.135.10.24.
Does this meet the goal?
You need to ensure that the URL is accessible through the application gateway.
Solution: You create a WAF policy exclusion for request headers that contain 137.135.10.24.
Does this meet the goal?Options
Discussion
Can Microsoft make these WAF config questions any less clear? Anyway, it's got to be B since the log flagged the ARGS value, not the header. Header exclusion won't bypass a block on request arguments. Someone correct me if I'm missing a subtlety.
Maybe B based on what I've seen in the official guide and some Microsoft practice sets.
Pretty sure it's B. Excluding headers won't help if WAF flagged ARGS. Needs to match the component where block happened, right?
I think A. Header exclusion should work since the solution targets requests from that IP, unless I’m missing something about ARGS.
Yeah, it's B here. The log flagged the request argument, not the header, so a header exclusion won't fix the issue. Pretty sure you need to set the exclusion for ARGS. Correct me if I'm wrong.
B , since the WAF is flagging ARGS, not headers. Header exclusion's a common trap here.
B for this. The WAF log shows ARGS got flagged (which means request params), so making a header exclusion won't un-block it. You'd need to target the same field the alert triggered on. Correct me if I'm missing something but pretty confident here.
Option B here. Had something like this in a mock, header exclusions don't cover ARGS so the request will still get blocked. You need to match the part WAF flagged, I think.
B tbh. Header exclusions don’t stop WAF if it blocks ARGS. Unless that log says header, this can’t work.
I get why you'd think A works, but the header exclusion doesn't fix an ARGS match. Still, I'm picking A here.
Be respectful. No spam.

