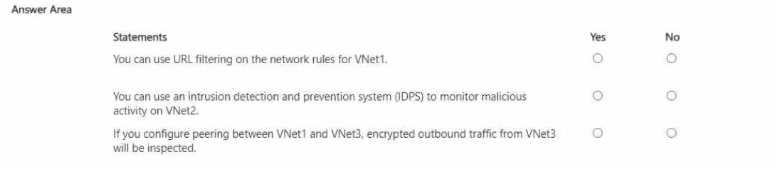
HOTSPOT You have an Azure subscription that contains the Azure Firewall policies shown in the following table. 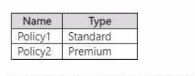
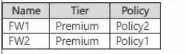
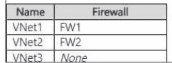
No, Yes, No. Network rules can't do URL filtering, that's for app rules only even with Premium firewall. IDPS is supported on VNet2 since it's using a Premium-tier firewall. The peering part doesn't guarantee inspection of encrypted outbound traffic from VNet3 unless routes and TLS inspection are set up. Used similar logic in the official docs/practice tests but correct me if I'm off.
Does anyone else think the first is a bit tricky because of the network vs application rule detail? Seems like "No" is right for URL filtering on VNet1 since that's only for application rules, not network ones. The encrypted inspection one is a trap too, peering alone isn't enough.
No, Yes, No here. Network rules can't do URL filtering, only application rules can. VNet2 can use IDPS since it's premium tier, and encrypted outbound from VNet3 won't get inspected just by peering alone. Pretty sure this is right but let me know if you disagree.
Careful with the wording, since it's network rules and not application rules for VNet1, you can't do URL filtering there. I've seen similar questions where just changing that detail flips the answer. So No for the first, but if it was 'application rules', it'd be Yes. Always check what rule type they're testing.
No, Yes, No for these. First one is a no because URL filtering only applies to application rules, not network rules in Azure Firewall (even if it's Premium tier). Second is yes since the Premium firewall on VNet2 includes IDPS. Third one is no, peering alone doesn't route traffic through the firewall for encrypted inspection. Pretty sure that's right but open to other views.
Not quite, it should be No for the URL filtering part. That feature only works on application rules, not network rules, even if you're using a premium policy. Easy to get caught by that wording! IDPS on VNet2 is Yes since it's premium, and the encrypted traffic inspection from just peering is No because nothing is forcing traffic through a firewall. Open to corrections if I missed something.