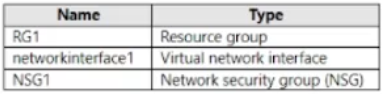
 NSG1 is associated to networkinterface1. User1 has role assignments for NSG1 as shown
in the following table.
NSG1 is associated to networkinterface1. User1 has role assignments for NSG1 as shown
in the following table.
 For each of the following statements, select Yes if the statement is true. Otherwise, select
No.
For each of the following statements, select Yes if the statement is true. Otherwise, select
No.
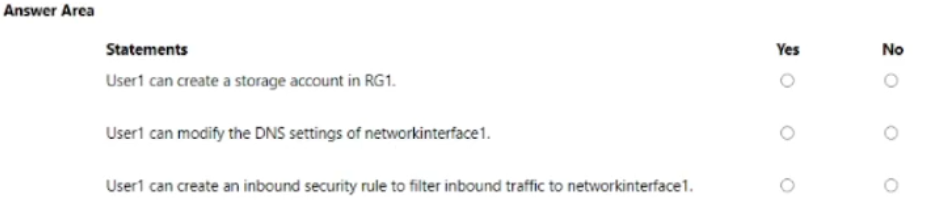
1. Yes
2. No
3. Yes
I remember a similar question on a practice test. User1 has Storage Account Contributor on RG1, so they can create storage accounts there. For the network interface DNS setting, they only have Reader rights so that's a no. But with Contributor on NSG1, User1 can definitely add inbound security rules to that NSG. Pretty sure this lines up with how Azure RBAC scopes work, but open to corrections if I missed something.
1. Yes, 2. No, 3. Yes
User1 has Storage Account Contributor on RG1 so that's enough to deploy storage accounts there. Changing DNS on networkInterface1 needs write access at the NIC which they don't have (just Reader at subscription). Contributor role on NSG1 gives permission to add inbound rules though. Pretty confident here, but open if someone spots a catch.
Yeah, this looks right to me. Storage Account Contributor at RG1 means User1 can make storage accounts, but can't mess with NIC DNS settings with just Reader rights. Contributor on NSG1 lets them add inbound rules for traffic filtering. Anyone see it differently?

