Had something like this in a mock and picked C and E. BFD (C) is used for subsecond failure detection with OSPF, while point-to-point links (E) simplify the topology, both speeding up convergence. If anyone disagrees let me know, but pretty sure that's Cisco's expected answer.
I was actually thinking D fits since it applies local authentication to the console, which sounds like what the question is after. It doesn’t have the explicit fallback, but if you only want local auth for console access when AAA is down, D makes sense. Pretty sure that's how I've seen it used before, though maybe I'm missing a nuance.
Refer to the exhibit. 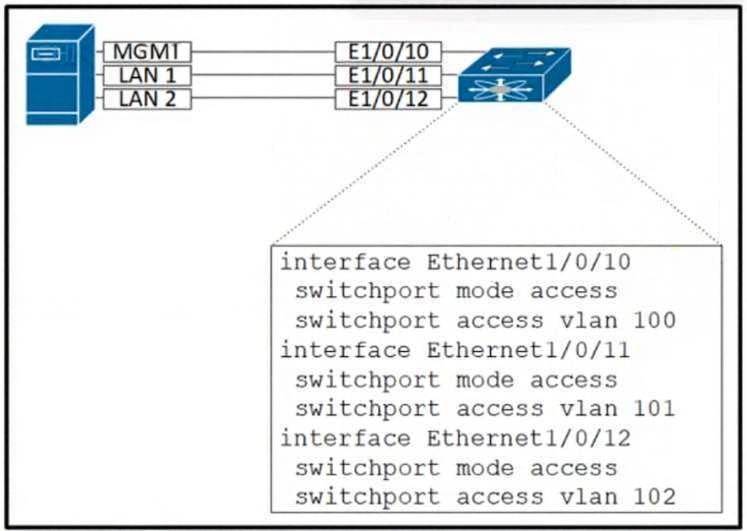
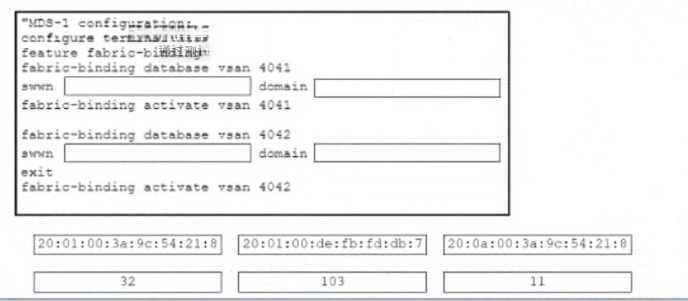
DRAG DROP Refer to the exhibit. 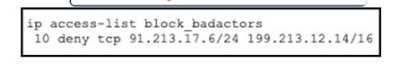
Looks like Target 1 should get 189.213.12.14, Target 2 gets 24, and the closing bracket goes at Target 3. That matches the ACL JSON format from similar exam reports. Pretty sure this is right but open to another view if I missed something!
DRAG DROP 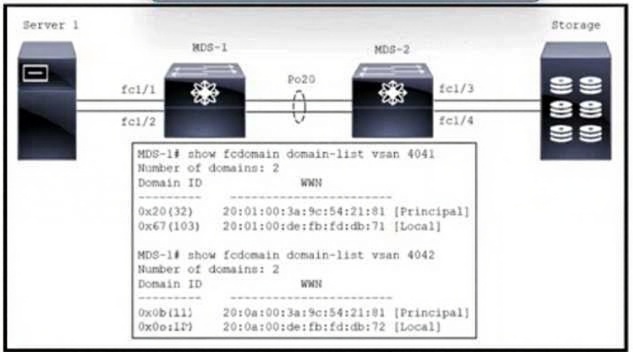
 B)
P-9
B)
P-9
 C)
C)
 D)
D)
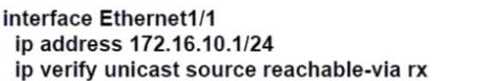
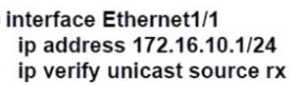
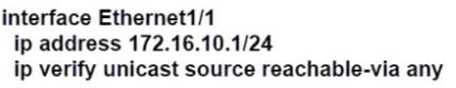
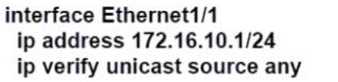
I remember seeing a similar question in some exam reports. D is the right pick because 'reachable-via rx' activates strict uRPF, forcing the packet's source to be reachable via the receiving interface. That matches Cisco's Nexus config for strict mode. If someone has seen it done another way let me know, but pretty sure it's D.
Honestly, Cisco's uRPF config options are easy to mix up-wish the syntax was more intuitive. C or D here. I picked C since it shows 'ip verify unicast source reachable-via any', and from what I remember, sometimes 'any' is used in strict mode examples. Strict mode should check the source on the incoming interface, which does make me doubt this slightly. If I'm missing something with Nexus specifics, let me know.
Probably C, but which mode are they specifically asking for if the requirement was just 'loose' not 'strict' mode? Official guide examples could flip it for me.
 Refer to the exhibit. An engineer is configuring Cisco Data Center Network Manager to automate the provisioning of
Cisco Nexus 9000 Series Switches. The engineer must configure user access for network engineers to permit device
operations in Interface Manager. The solution must hide Admin and Config Menu items in Interface Manager Which
two roles must be assigned to the network engineers to meet these requirements? (Choose two.)
Refer to the exhibit. An engineer is configuring Cisco Data Center Network Manager to automate the provisioning of
Cisco Nexus 9000 Series Switches. The engineer must configure user access for network engineers to permit device
operations in Interface Manager. The solution must hide Admin and Config Menu items in Interface Manager Which
two roles must be assigned to the network engineers to meet these requirements? (Choose two.)Option A makes sense, since UCS Lightweight upgrade is about only updating components that actually need new firmware. That way, you skip pushing updates and rebooting everything unnecessarily, so less downtime. D would do the opposite by rebooting all servers, which isn't 'lightweight' at all. Pretty sure this matches what Cisco docs explain. Agree?