Q: 3
Refer to the exhibit: 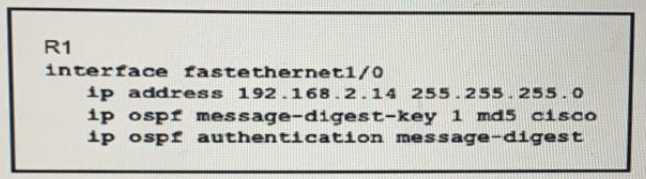
Options
Discussion
A , the key ID mismatch is what actually blocks OSPF MD5 peers in practice.
A is wrong, A. Both sides have to match key ID and key value for OSPF MD5 authentication, or they'll never form adjacency. I remember getting tripped up by this in lab before. Correct me if I'm missing a special case!
A is wrong, A. Official Cisco guide is clear on matching key ID and value for OSPF MD5.
I don’t think it’s A. B.
Had something like this in a mock, it's A.
Nah, it’s not B. The exhibit shows message-digest auth, so OSPF needs both key ID and key value to match on both peers or adjacencies won’t come up. B is a classic trap because some folks think just the value is enough. Pretty sure A is right here-correct me if I missed something.
A , both key ID and key value have to match for OSPF auth neighbors to come up. Seen this in lab setups, mismatched key IDs mean no adjacency, even if the value is right. B would only work if OSPF allowed any key ID as long as the value matched, which isn't the case here. Correct me if I'm missing some weird config.
B not A
A
A tbh. Seen a similar question in practice, always trips people up since key ID and key value both need to match, not just one. B is tempting but not right here.
Be respectful. No spam.

