Pretty sure it should be C. To see if risk mitigation is really working, you have to look at whether the controls are actually cost-effective and reducing risk, not just if systems are documented (D is more about asset inventory). Seen similar questions in practice material. Anyone see an argument for B here?
Had something like this in a mock recently. The main goal of hardening is to securely configure devices to minimize vulnerabilities, so limiting the attack surface. Option A lines up with that. The others are more about detection or analysis after the fact, not prevention.
Option D might fit if the question was asking about incident response, but since it's about hardening, do they mean "best purpose" or just "one of the purposes"? That would change things here.
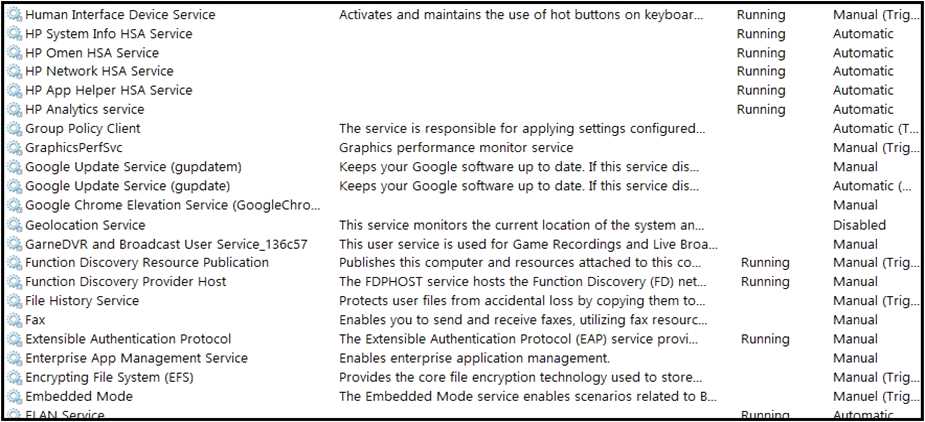 An engineer received multiple reports from employees unable to log into systems with the error: The
Group Policy Client service failed to logon – Access is denied. Through further analysis, the engineer
discovered several unexpected modifications to system settings. Which type of breach is occurring?
An engineer received multiple reports from employees unable to log into systems with the error: The
Group Policy Client service failed to logon – Access is denied. Through further analysis, the engineer
discovered several unexpected modifications to system settings. Which type of breach is occurring?Pretty sure it's C. Privilege escalation fits because of the system setting changes, that's a key sign from similar practice exams. You see DoS errors, but with those mods it's usually more than just denial-of-service. Disagree?
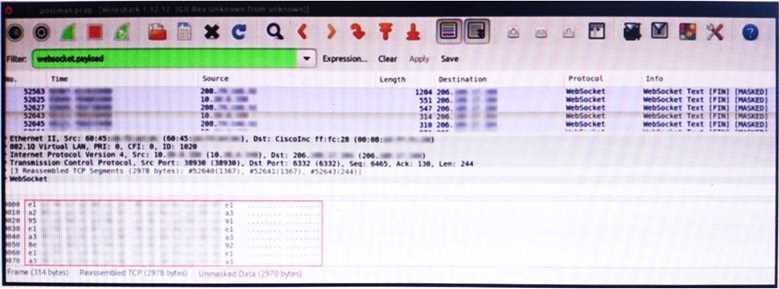 An engineer is analyzing this Vlan0386-int12-117.pcap file in Wireshark after detecting a suspicious
network activity. The origin header for the direct IP connections in the packets was initiated by a
google chrome extension on a WebSocket protocol. The engineer checked message payloads to
determine what information was being sent off-site but the payloads are obfuscated and unreadable.
What does this STIX indicate?
An engineer is analyzing this Vlan0386-int12-117.pcap file in Wireshark after detecting a suspicious
network activity. The origin header for the direct IP connections in the packets was initiated by a
google chrome extension on a WebSocket protocol. The engineer checked message payloads to
determine what information was being sent off-site but the payloads are obfuscated and unreadable.
What does this STIX indicate?I kind of see why C might seem right since HTTP status codes are part of the protocol, but for REST APIs, 2xx usually signals the request was handled successfully. Not totally convinced though-depends how strict they want to be with wording here. Agree?
D imo makes sense if the focus was on fixing payments quickly, but since it's asking what to do first, A fits better because you need to figure out what happened before jumping to manual fixes. Is there a specific company policy that prioritizes incident escalation over initial investigation?
Shouldn't we clarify exactly what caused the payment misdirection before alerting IR? If the SaaS tool was down and it's not confirmed as a breach, jumping straight to B seems premature. Anyone else think gathering info from the SaaS team (A) makes more sense as a first step?
Shouldn't we check with the SaaS tool team first to figure out what went wrong before escalating? Jumping to B seems like an easy trap here, since you don’t know the scope or if it’s a breach yet.
B tbh makes sense, since after behavioral analysis you'd typically want to unpack the specimen and dig into memory forensics to see any code or artifacts loaded in RAM. You get more insight before moving on to code-level static or dynamic analysis (A). That's the standard progression from what I've seen in Cisco-style guides. Pretty sure B is right, but open to comments if I missed something.
Why wouldn’t unpacking and memory forensics (B) come before code analysis here? Analyzing packed or obfuscated malware statically (A) seems premature unless the specimen’s already been fully extracted. Seen Cisco stress this order in exam reports. Anyone see it asked another way?

