Q: 7
Refer to the exhibit.
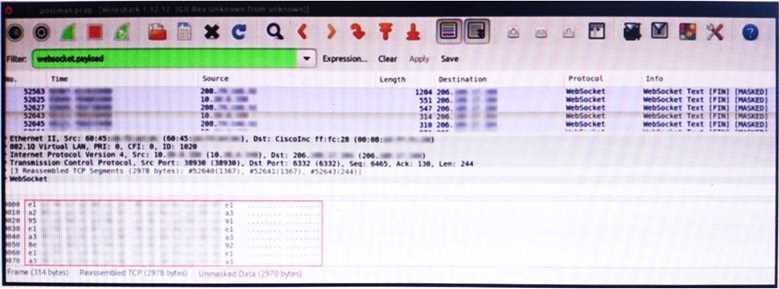
 An engineer is analyzing this Vlan0386-int12-117.pcap file in Wireshark after detecting a suspicious
network activity. The origin header for the direct IP connections in the packets was initiated by a
google chrome extension on a WebSocket protocol. The engineer checked message payloads to
determine what information was being sent off-site but the payloads are obfuscated and unreadable.
What does this STIX indicate?
An engineer is analyzing this Vlan0386-int12-117.pcap file in Wireshark after detecting a suspicious
network activity. The origin header for the direct IP connections in the packets was initiated by a
google chrome extension on a WebSocket protocol. The engineer checked message payloads to
determine what information was being sent off-site but the payloads are obfuscated and unreadable.
What does this STIX indicate?
 An engineer is analyzing this Vlan0386-int12-117.pcap file in Wireshark after detecting a suspicious
network activity. The origin header for the direct IP connections in the packets was initiated by a
google chrome extension on a WebSocket protocol. The engineer checked message payloads to
determine what information was being sent off-site but the payloads are obfuscated and unreadable.
What does this STIX indicate?
An engineer is analyzing this Vlan0386-int12-117.pcap file in Wireshark after detecting a suspicious
network activity. The origin header for the direct IP connections in the packets was initiated by a
google chrome extension on a WebSocket protocol. The engineer checked message payloads to
determine what information was being sent off-site but the payloads are obfuscated and unreadable.
What does this STIX indicate?Options
Discussion
C. not D. Malware is tempting but the clue is about obfuscated payloads that aren’t UTF-8, which can mean data leak via odd encoding. Similar exam questions tend to push toward C here.
C tbh. I remember similar scenarios mentioned in the official guide and practice tests where if payloads are obfuscated instead of readable UTF-8, it's a classic sign of data leakage, not confirmed malware. WebSockets by themselves aren't enough to call out malware activity unless you have more context. Pretty sure C is what they're after here but open to other ideas.
D , seen similar on some practice labs and official study guide questions where unreadable WebSocket payloads hinted at malware traffic.
Option C looks most likely to me. Payloads that aren't readable UTF-8 and appear obfuscated suggest possible data exfil, not just normal extension behavior. Not 100% sure, could be some rare legit case but that's my read.
Option C makes more sense here. The question just says the payloads are obfuscated, not that there’s confirmed malware or C2 activity-just a potential data leak. Not 100% though, could see why people pick D.
D , unreadable payloads over WebSockets from a browser extension screams C2 comms and malware trap option.
D imo. If the payloads are unreadable and using WebSockets directly from a Chrome extension, that feels like malware C2 comms to me. C could be right, but exam questions often use D when encrypted exfil is clear. Anyone see it differently?
Its C here. D's a classic trap, but STIX often points to data leak if the encoding isn't UTF-8-seen something similar on other exam reports. Open if anyone thinks different.
D doesn’t fit, C . Official guides and Wireshark labs both mention encoded payloads as red flags for exfil.
I think D. If the payloads are obfuscated and using non-standard encoding over WebSockets, could be malware talking to C2. I know C is possible but encrypted channels are classic for exfil. Not totally sure though, open to other ideas.
Be respectful. No spam.

