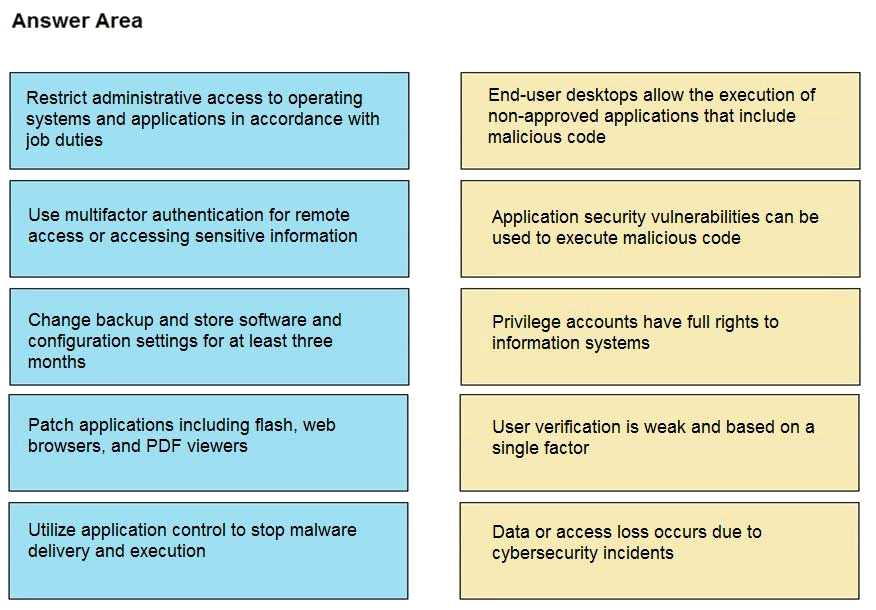
DRAG DROP Drag and drop the mitigation steps from the left onto the vulnerabilities they mitigate on the right.
Looks like standard mapping from official guide labs. App control for desktops, patching for vulnerabilities, restrict admin for privilege, MFA for weak auth, backups for data loss.
Yeah, this mapping makes sense. App control lines up with stopping non-approved desktop apps, patching is standard for app vulnerabilities, limiting admin rights handles privilege issues, MFA addresses weak verification, and backups are your answer for data loss. Seen similar matches on other practice sets, but open if someone has a different logic!
Pretty sure the mapping is: app control for blocking non-approved desktop apps, patching for app vulnerabilities, restrict admin for privilege account risks, MFA fixes weak single-factor auth, and backup retention covers data loss. That's what I'd expect from Cisco best practices. Let me know if you see a better fit.