Q: 11
An organization wants to use DMARC to improve its brand reputation by leveraging DNS records.
Which two email authentication mechanisms are utilized during this process? (Choose two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 12
What is the order of virus scanning when multilayer antivirus scanning is configured?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 13
Email encryption is configured on a Cisco ESA that uses CRES.
Which action is taken on a message when CRES is unavailable?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 14
DRAG DROP
Drag and drop the AsyncOS methods for performing DMARC verification from the left into the correct
order on the right.

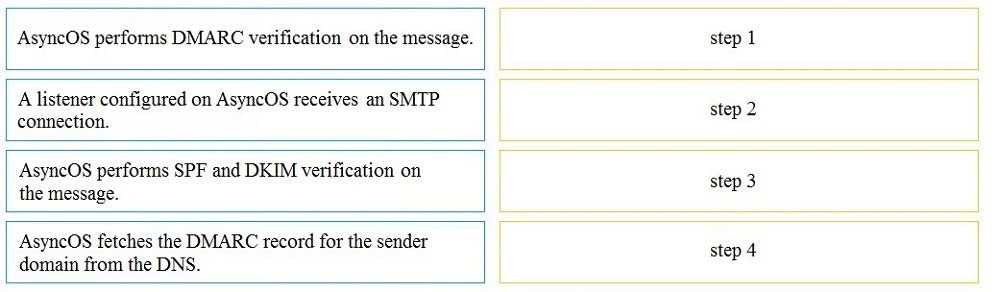
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 15
DRAG DROP
Drag and drop authentication options for End-User Quarantine Access from the left onto the
corresponding configuration steps on the right.

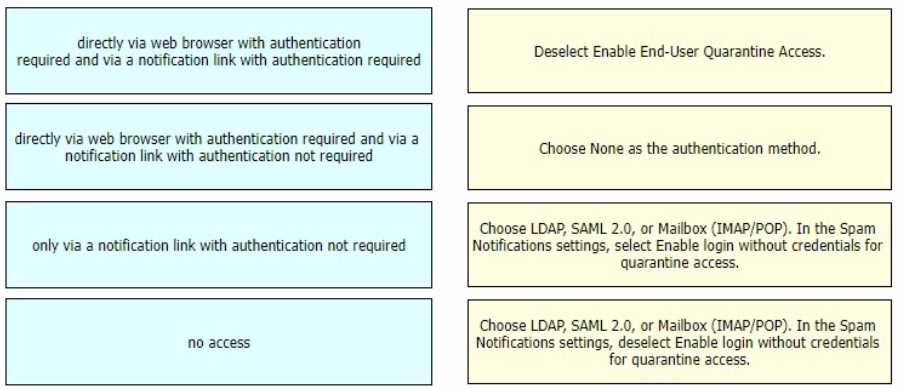
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 16
DRAG DROP
Drag and drop the Cisco ESA reactions to a possible DLP from the left onto the correct action types on
the right.

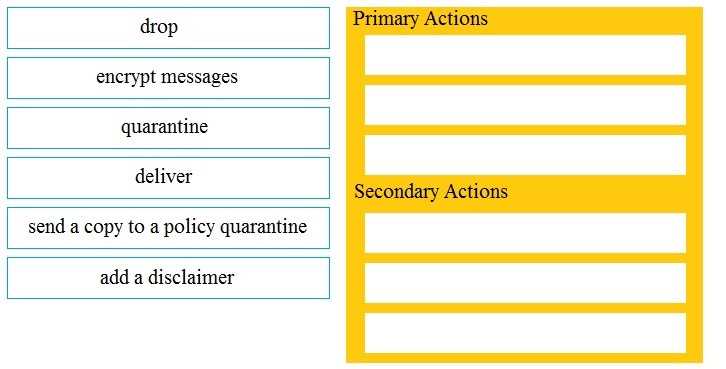
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 17
DRAG DROP
An Encryption Profile has been set up on the Cisco ESA.
Drag and drop the steps from the left for creating an outgoing content filter to encrypt emails that
contains the subject "Secure:" into the correct order on the right.

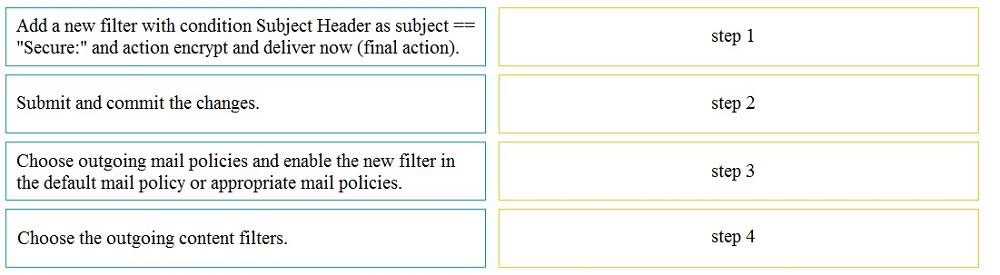
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 18
DRAG DROP
Drag and drop the graymail descriptions from the left onto the verdict categories they belong to on
the right.

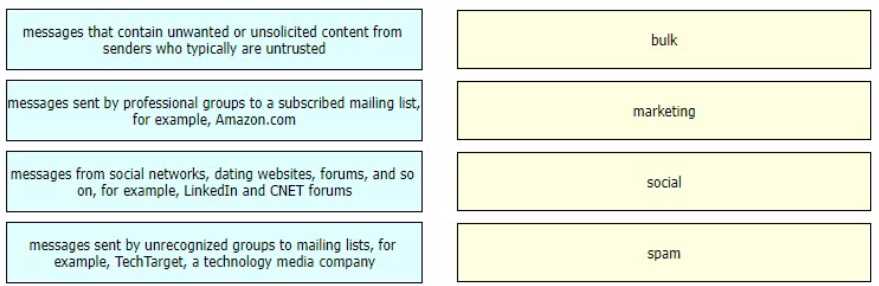
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 19
DRAG DROP
Drag and drop the steps to configure Cisco ESA to use SPF/SIDF verification from the left into the
correct order on the right.

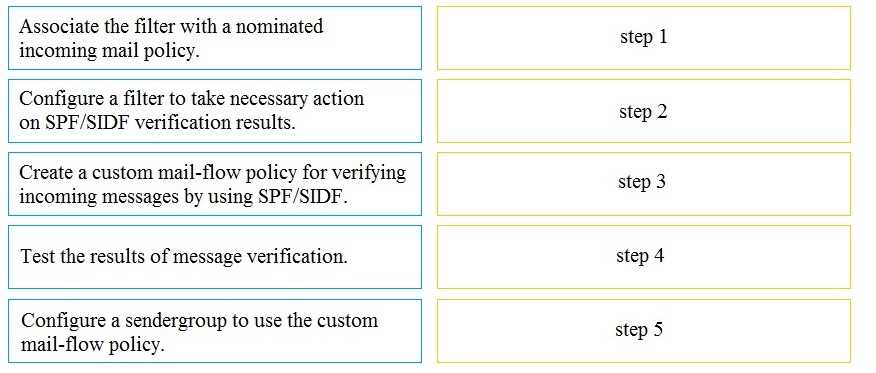
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 20
DRAG DROP
An administrator must ensure that emails sent from [email protected] are routed through
an alternate virtual gateway. Drag and drop the snippet from the bottom onto the blank in the
graphic to finish the message filter syntax. Not all snippets are used.

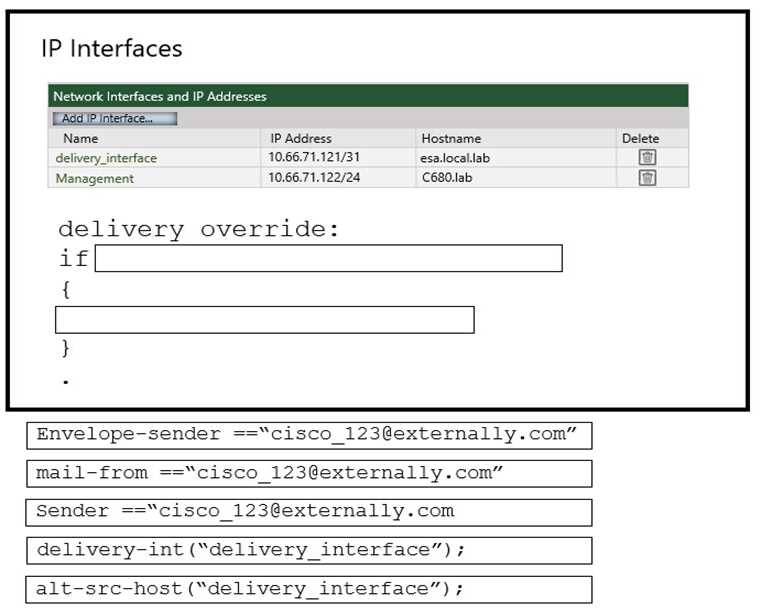
Your Answer
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Question 11 of 20 · Page 2 / 2

