Q: 1
An engineer wants to utilize a digital signature in outgoing emails to validate to others that the email
they are receiving was indeed sent and authorized by the owner of that domain Which two
components should be configured on the Cisco Secure Email Gateway appliance to achieve this?
(Choose two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 2
What are two primary components of content filters? (Choose two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 3
A Cisco Secure Email Gateway appliance is processing many messages that are sent to invalid
recipients verification. Which two steps are required to accomplish this task? (Choose two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 4
What are two prerequisites for implementing undesirable URL protection in Cisco ESA? (Choose
two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 5
A network engineer must tighten up the SPAM control policy of an organization due to a recent SPAM
attack. In which scenario does enabling regional scanning improve security for this organization?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 6
Which method enables an engineer to deliver a flagged message to a specific virtual gateway
address in the most flexible way?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 7
Which two actions are configured on the Cisco ESA to query LDAP servers? (Choose two.)
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 8
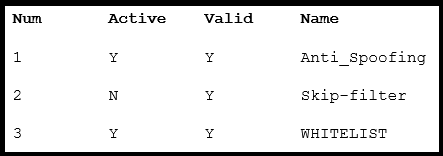 Refer to the exhibit. What is the correct order of commands to set filter 2 to active?
Refer to the exhibit. What is the correct order of commands to set filter 2 to active?Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 9
When DKIM signing is configured, which DNS record must be updated to load the DKIM public
signing key?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Q: 10
A network administrator notices that there are a high number of queries to the LDAP server. The mail
logs show an entry “550 Too many invalid recipients | Connection closed by foreign host.”
Which feature must be used to address this?
Options
Discussion
No comments yet. Be the first to comment.
Be respectful. No spam.
Question 1 of 20 · Page 1 / 2

