F5 Networks F5CAB1
Q: 1
A BIG-IP device will be dedicated to functioning as a WAF, requiring only the ASM module to be
provisioned.
What provisioning level will ensure that the system allocates all CPU, memory, and disk resources to
this module exclusively?
Options
Q: 2
What will setting a Self IP to “Allow None” for Port Lockdown do?
Options
Q: 3
The BIG-IP Administrator uses Secure Copy Protocol (SCP) to upload a TMOS image to the
/shared/images/ directory in preparation for an upgrade.
After the upload is complete, what will the system do before the image appears in the GUI under:
System » Software Management » Image List?
Options
Q: 4
The BIG-IP Administrator uses Secure Copy Protocol (SCP) to upload a TMOS image to the
/shared/images/ directory in preparation for a TMOS upgrade.
After the upload is completed, what will the system do before the image is shown in the GUI under:
System » Software Management » Image List?
Options
Q: 5
Refer to the exhibit.
 An organization has purchased a BIG-IP license that includes all available modules but has chosen to
provision only the modules they require.
The exhibit displays the current resource allocation from the System → Resource Provisioning page.
Based on the information provided, which F5 modules have been provisioned?
An organization has purchased a BIG-IP license that includes all available modules but has chosen to
provision only the modules they require.
The exhibit displays the current resource allocation from the System → Resource Provisioning page.
Based on the information provided, which F5 modules have been provisioned?
 An organization has purchased a BIG-IP license that includes all available modules but has chosen to
provision only the modules they require.
The exhibit displays the current resource allocation from the System → Resource Provisioning page.
Based on the information provided, which F5 modules have been provisioned?
An organization has purchased a BIG-IP license that includes all available modules but has chosen to
provision only the modules they require.
The exhibit displays the current resource allocation from the System → Resource Provisioning page.
Based on the information provided, which F5 modules have been provisioned?Options
Q: 6
A BIG-IP Administrator needs to purchase new licenses for a BIG-IP appliance.
The administrator needs to know:
Whether a module is licensed
The memory requirement for that module
Where should the administrator view this information in the System menu?
Options
Q: 7
A BIG-IP Administrator needs to install a HotFix on a standalone BIG-IP device, which has HD1.1 as
the Active Boot Location.
The administrator has already re-activated the license and created a UCS archive.
In which sequence should the administrator perform the remaining steps?
Options
Q: 8
A BIG-IP Administrator discovers malicious brute-force attempts to access the BIG-IP device on the
management interface via SSH.
The administrator needs to restrict SSH access to the management interface.
Where should this be accomplished?
Options
Q: 9
Refer to the exhibit.
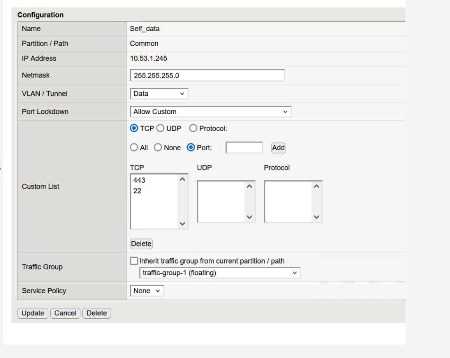 What traffic will be permitted to reach the BIG-IP?
What traffic will be permitted to reach the BIG-IP?
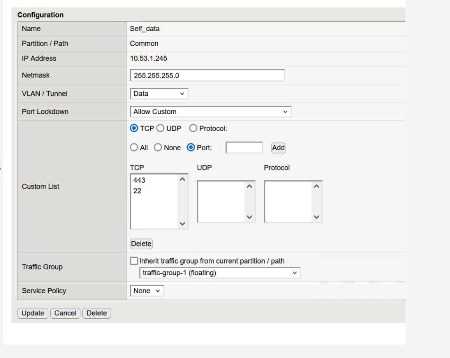 What traffic will be permitted to reach the BIG-IP?
What traffic will be permitted to reach the BIG-IP?Options
Q: 10
The device is currently on v15.1.2.1.
The BIG-IP Administrator needs to boot the device back to v13.1.0.6 to gather data for
troubleshooting.
The system shows:
Sys::Software Status
Volume Product Version Build Active Status Allowed
HD1.1 BIG-IP 15.1.2.1
0.0.10 yes
complete yes
HD1.2 BIG-IP 13.1.0.6
0.0.3 no
complete yes
Which is the correct command-line sequence to boot the device to version 13.1.0.6?
Options
Question 1 of 10

