FCSS_CDS_AR-7.6.pdf
Q: 1
Refer to the exhibit.
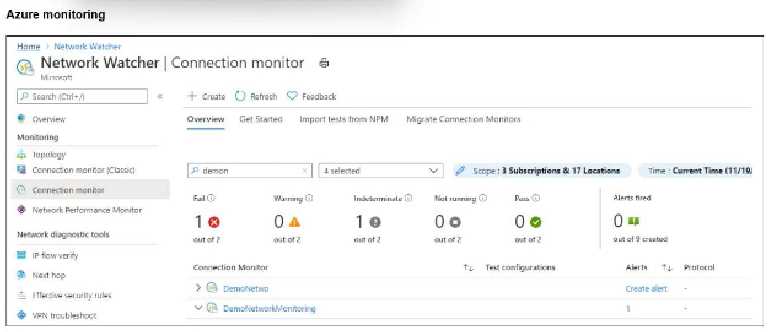 Refer to the exhibit.
After analyzing the native monitoring tools available in Azure, an administrator decides to use the
tool displayed in the exhibit.
Why would an administrator choose this tool?
Refer to the exhibit.
After analyzing the native monitoring tools available in Azure, an administrator decides to use the
tool displayed in the exhibit.
Why would an administrator choose this tool?
 Refer to the exhibit.
After analyzing the native monitoring tools available in Azure, an administrator decides to use the
tool displayed in the exhibit.
Why would an administrator choose this tool?
Refer to the exhibit.
After analyzing the native monitoring tools available in Azure, an administrator decides to use the
tool displayed in the exhibit.
Why would an administrator choose this tool?Options
Q: 2
An administrator decides to use the Use managed identity option on the FortiGate SDN connector
with Microsoft Azure. However, the SDN connector is failing on the connection.
What must the administrator do to correct this issue?
Options
Q: 3
Refer to the exhibit.
 An administrator implements FortiWeb ingress controller to protect containerized web applications
in an AWS Elastic Kubernetes Service (EKS) cluster.
What can you conclude about the topology shown in FortiView?
An administrator implements FortiWeb ingress controller to protect containerized web applications
in an AWS Elastic Kubernetes Service (EKS) cluster.
What can you conclude about the topology shown in FortiView?
 An administrator implements FortiWeb ingress controller to protect containerized web applications
in an AWS Elastic Kubernetes Service (EKS) cluster.
What can you conclude about the topology shown in FortiView?
An administrator implements FortiWeb ingress controller to protect containerized web applications
in an AWS Elastic Kubernetes Service (EKS) cluster.
What can you conclude about the topology shown in FortiView?Options
Q: 4
Which statement about Transit Gateway (TGW) in Amazon Web Services (AWS) is true?
Options
Q: 5
You need a solution to safeguard public cloud-hosted web applications from the OWASP Top 10
vulnerabilities. The solution must support the same region in which your applications reside, with
minimum traffic cost.
Which solution meets the requirements?
Options
Q: 6
Refer to the exhibit.
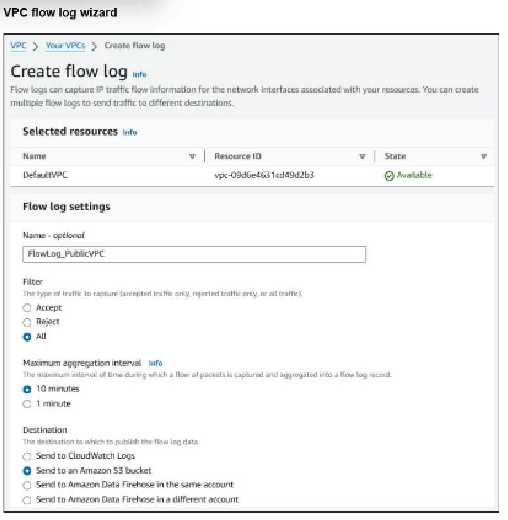 Refer to the exhibit.
An experienced AWS administrator is creating a new Virtual Private Cloud (VPC) flow log with the
settings shown in the exhibit.
What is the purpose of this configuration?
Refer to the exhibit.
An experienced AWS administrator is creating a new Virtual Private Cloud (VPC) flow log with the
settings shown in the exhibit.
What is the purpose of this configuration?
 Refer to the exhibit.
An experienced AWS administrator is creating a new Virtual Private Cloud (VPC) flow log with the
settings shown in the exhibit.
What is the purpose of this configuration?
Refer to the exhibit.
An experienced AWS administrator is creating a new Virtual Private Cloud (VPC) flow log with the
settings shown in the exhibit.
What is the purpose of this configuration?Options
Q: 7
You are using Ansible to modify the configuration of several FortiGate VMs.
What is the minimum number of files you need to create, and in which file should you configure the
target FortiGate IP addresses?
Options
Q: 8
In an SD-WAN TGW Connect topology, which three initial steps are mandatory when routing traffic
from a spoke VPC to a security VPC through a Transit Gateway? (Choose three.)
Options
Q: 9
Refer to the exhibit.
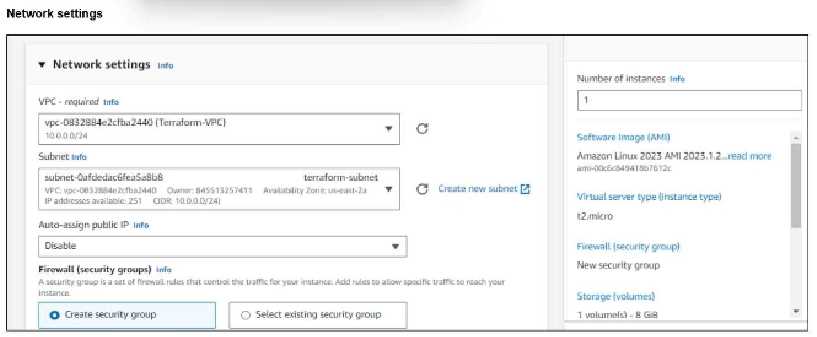 Refer to the exhibit.
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown in
the exhibit.
What next step must the administrator take to access this instance from the internet?
Refer to the exhibit.
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown in
the exhibit.
What next step must the administrator take to access this instance from the internet?
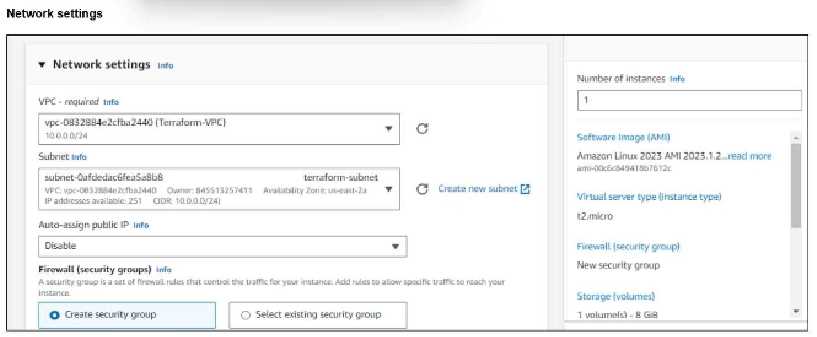 Refer to the exhibit.
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown in
the exhibit.
What next step must the administrator take to access this instance from the internet?
Refer to the exhibit.
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown in
the exhibit.
What next step must the administrator take to access this instance from the internet?Options
Q: 10
An administrator would like to use FortiCNP to keep track of sensitive data files located in the
Amazon Web Services (AWS) S3 bucket and protect it from malware.
Which FortiCNP feature should the administrator use?
Options
Question 1 of 10

