FCP FWB AD 7.4
Q: 1
How are bot machine learning (ML) models different from API or anomaly detection models?
Options
Q: 2
Refer to the exhibit.
What is true about this FortiWeb device? (Choose two.)
Options
Q: 3
Which implementation is most suited for a deployment that must meet PCI DSS compliance criteria?
Options
Q: 4
Refer to the exhibit.
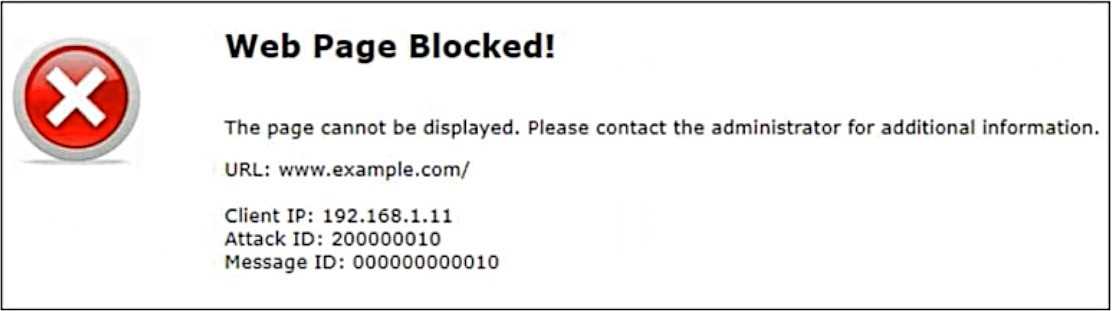 Attack ID 20000010 is brute force logins.
Which statement is accurate about the potential attack?
Attack ID 20000010 is brute force logins.
Which statement is accurate about the potential attack?
 Attack ID 20000010 is brute force logins.
Which statement is accurate about the potential attack?
Attack ID 20000010 is brute force logins.
Which statement is accurate about the potential attack?Options
Q: 5
Which Layer 7 routing method does FortiWeb support?
Options
Q: 6
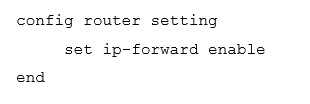
Review the following configuration:
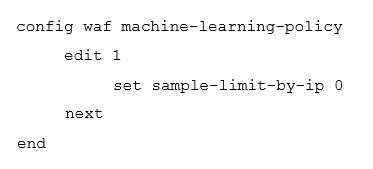 Which result would you expect from this configuration setting?
Which result would you expect from this configuration setting?
 Which result would you expect from this configuration setting?
Which result would you expect from this configuration setting?Options
Q: 7
An administrator notices multiple IP addresses attempting to log in to an application frequently,
within a short time period. They suspect attackers are attempting to guess user passwords for a
secure application.
What is the best way to limit this type of attack on FortiWeb, while still allowing legitimate traffic
through?
Options
Q: 8
Which high availability (HA) mode uses gratuitous Address Resolution Protocol (ARP) to advertise a
failover event to neighboring network devices?
Options
Q: 9
Refer to the exhibits. 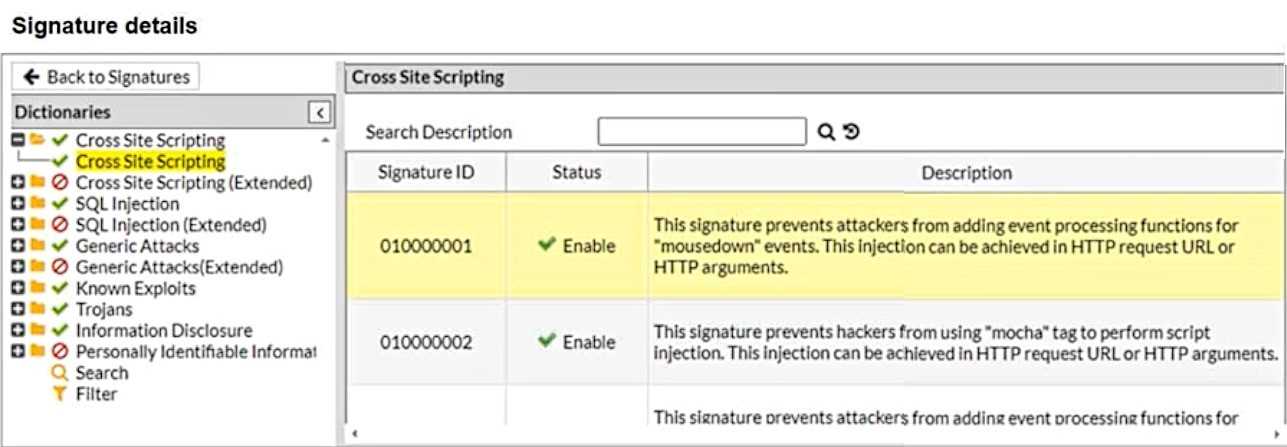
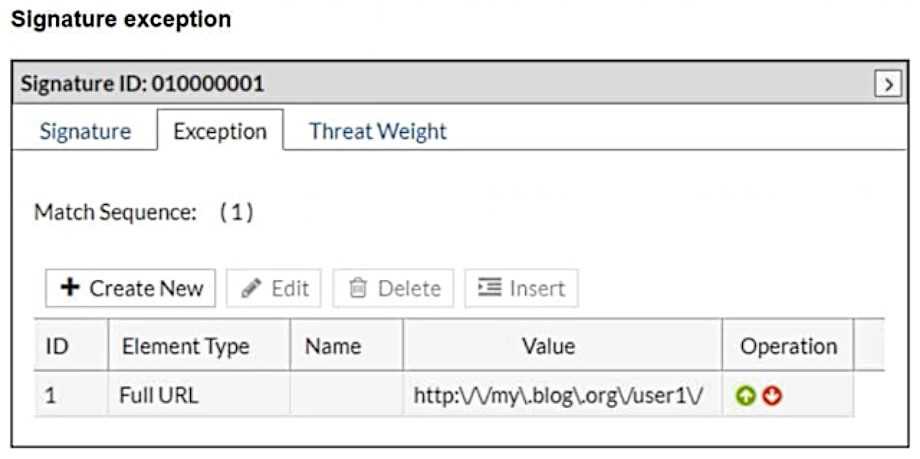 What will happen when a client attempts a mousedown cross-site scripting (XSS) attack against the site https://my.blog.org/userl1/blog.php and FortiWeb is enforcing the highlighted signature?
What will happen when a client attempts a mousedown cross-site scripting (XSS) attack against the site https://my.blog.org/userl1/blog.php and FortiWeb is enforcing the highlighted signature?
Options
Q: 10
Review the following configuration:
 What are two routing behaviors that you can expect on FortiWeb after this configuration change?
(Choose two.)
What are two routing behaviors that you can expect on FortiWeb after this configuration change?
(Choose two.)
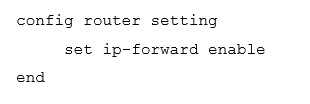 What are two routing behaviors that you can expect on FortiWeb after this configuration change?
(Choose two.)
What are two routing behaviors that you can expect on FortiWeb after this configuration change?
(Choose two.)Options
Question 1 of 10

